Researchers discovered a new wave of spyware apps named Stalkerware emerging in wide for the past few months that spies victims’ online activities and steal sensitive data from the infected devices.
Recently FTC warned that Retina-X developed and sold MobileSpy, PhoneSheriff and TeenShield shared sensitive information about your smartphone activities – such as call history, text messages, photos, GPS locations, and browser history.
Following this FTC report, a new set of Stalkerware apps emerging and spying the victim’s device by installing the spyware apps in victims’ devices without knowledge.
Attackers using various social engineering techniques to install spyware apps instead of physically access the device and also these spyware apps are capable of gaining the admin level privilege to steal the data and send it to the C2 server that controlled by the attackers.
These Stalkerware (stalking apps or spyware) apps are capable of performing various malicious activities such as, Stealing contacts, Spying on text messages, Stealing photos, Spying on browsing history, Spying on banking apps, Stealing GPS locations.
Spyware Apps That recently Found in Wide
Researchers from Zscaler observed several spyware apps in different names with sophisticated evasion techniques to bypass the Google Play Protect security framework.
Android Monitors
Dubbed Android Monitors app cleverly bypass the Play protect and act as a keylogger to log the user’s activities.
The app has various features and spies personal WhatsApp messages, Facebook chats, emails, banking activities, and much more.

Based on the appearance of the app, researchers believe that the app still under the development phase.
Package Name: com.ibm.fb
Hash : 97c6c8b961d57d4ebad47f5c63ec6446
Russ City
Dubbed Russ City with the package name of city.russ.alltrackercorp posed as a Thief hacker app and it has 3 similar samples that is capable of performing various malicious activities.
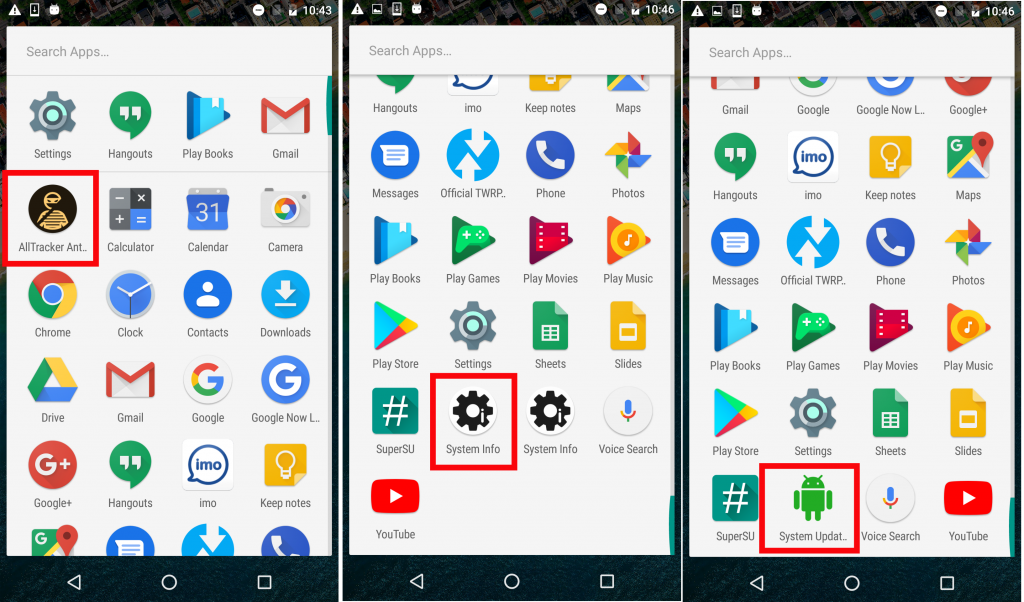

This app performs various background services:
- Read text messages
- Get browser history
- Fetch call logs
- Get GPS location
- Get clicked photos
- Record audio
- Record voice calls
- Capture screenshots
Wi-Fi Settings
Another spyware app named as “Wi-Fi settings” portrays itself as a settings app for Wi-Fi and it installed as Update Settings wit persistent capability.
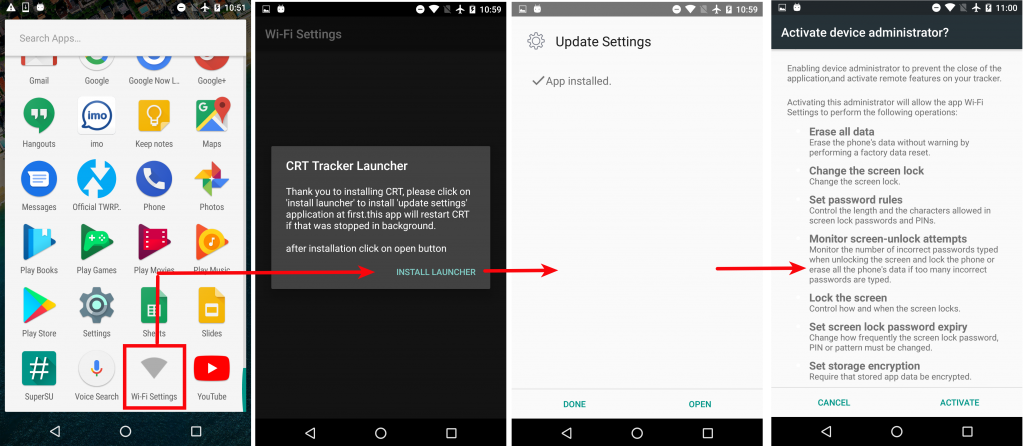
According to Zscaler’s research, Once the initial setup is done, the attacker can enter his/her credentials and leave the rest on spyware. As soon as the spyware gets an internet connection, it starts sending the stolen data to a command & control (C&C) center/server.
The Wifi settings stalkerware has a major flaw that the app sending all the stolen information over plain-text (unencrypted HTTP).

Auto Forward
The portrait as parental control apps to perform its spying activities with the name of Auto Froward.
“As soon as the spyware is installed, it displays itself as an app named Device. It asks for all available permissions necessary to spy”
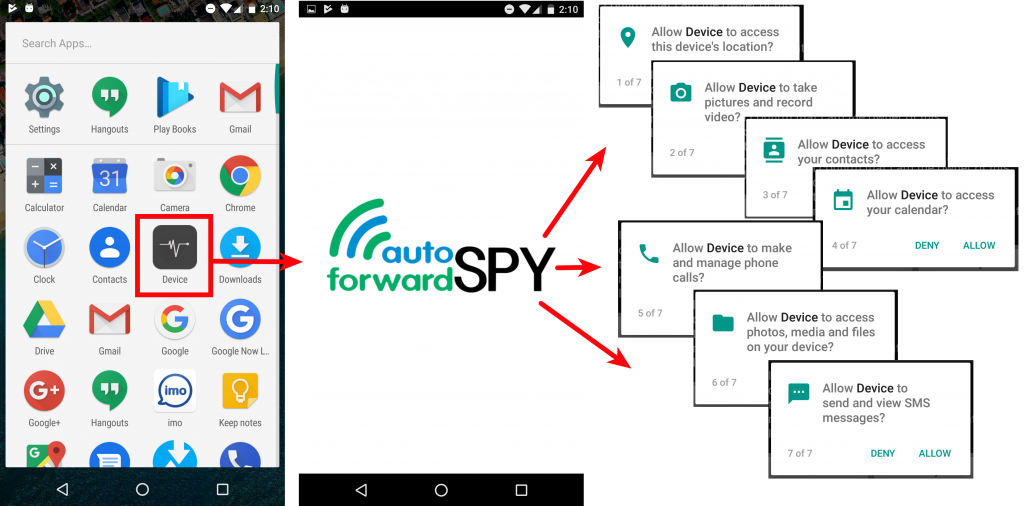
After the successful installation, it harvests the infected victim’s sensitive data and sends it to its command control server and also the attacker can easily view stolen data such as text messages, WhatsApp activities, GPS locations, photos, a list of installed apps, and so on.
Remediations: (zscaler)
Smartphone users who suspect their privacy may have been compromised by such apps can consider following these steps:
- Use a legitimate antivirus app that is regularly updated
- Try factory-resetting your device
- Remove suspicious apps from device administrator list
( settings –> security –> device administrators)
IOCs
| Hash |
| 97c6c8b961d57d4ebad47f5c63ec6446 |
| b0e68b66a5ba47612f2a6a33b343503b |
| 93e969ea1118a9d00be7f1c74b50fce9 |
| b44a98af29b021ad5df4ac6cc38fecf5 |
| d4ecbf666d17326deab49f75588e08b3 |
| 9eaf38020f898073af1a3ce34226c91f |
| ea1546f34a6cd517dcfec07861b7fb4f |
| 5fbb1b497c5a86815e5e8cc092d09af0 |
| 10322c7dea57269d69a85699e0357f5f |
| 3b388138584ad3168e745097d5aa4206 |
| 369a17a8e1031101f41cc31caac56b9c |
| ba63ae94bdec93abc144f3b628d151ad |
| 8dab7a558f91e72e3edae8e20ee55c86 |
| 001209b1e2760f88f2bb4b68f159a473 |
| 33dcfd84589c6ccf00fa5a302cefd0fe |
| 66dbd2d7614555440b657ae24527034a |
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
