TikTok is the most popular video-sharing app, it has more than 1.3 billion users worldwide. TikTok in news for the last few months, because of the potential risks embedded within the app.
Last December a lawsuit filed stating that “TikTok shared the created videos that include close-ups of faces and private acts with the TikTok app before the videos are saved.”
Recently U.S. Army announced bans for soldiers from using the TikTok app in government phones. The ban comes as the app may be used for surveillance purposes.
Dozens of TikTok Vulnerabilities
Security researchers from Check Point discovered multiple vulnerabilities with the application, allows attackers to perform the following on any TikTok account:
- Manipulating the user content
- Delete videos
- Upload videos
- Can Change video from private to public
- Retrieve personal information
A chain of vulnerabilities discovered includes SMS Link Spoofing, Open redirection, Cross-Site Scripting (XSS), Cross-Site Request Forgery (CSRF) and Sensitive Data Exposure.
Combining the vulnerabilities an attacker can take complete control of any TikTok user accounts.
The official website of the TikTok has an option to send an SMS message to any provide number, an attacker can capture the HTTP request by using a proxy tool like Burp Suite and they can change the download URL to a different link.

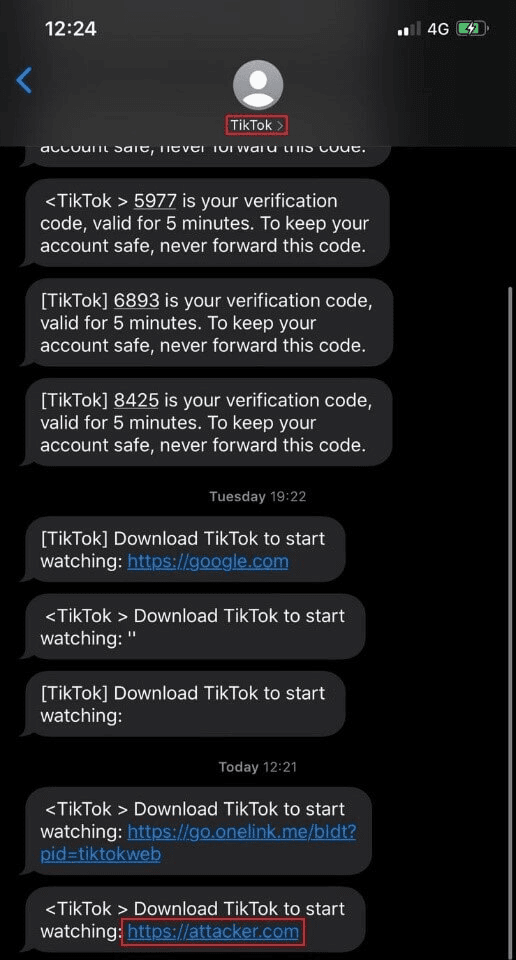
So that the recipient will get a spoofed link instead of the original link that used to download the TikTok application.
Researchers found that the app has deep links functionality, which lets users directly reach a specific destination within the app.
The TikTok login redirection process also found to be vulnerable, it allows attackers to perform a redirection to anything with tiktok.com. Following that, an XSS vulnerability was found in the ads.tiktok.com website.

“With the lack of anti-Cross-Site request forgery mechanism, we realized that we could execute JavaScript code and perform actions on behalf of the victim, without his/her consent.”
All the vulnerabilities have been reported to TikTok developers and the vulnerabilities have been fixed now. Android and iOS users are recommended to update with the latest version of TikTok.



.png
)
