A security vulnerability with TikTok allows attackers to inject any videos in the User feeds, the bug affects verified users also. Attackers may exploit this vulnerability to ake their videos popular.
TikTok is a Chinese based popular video-sharing mobile platform and which is owned by Beijing-based ByteDance.It is the most popular video-sharing app, it has more than 1.3 billion users worldwide.
TikTok Vulnerability
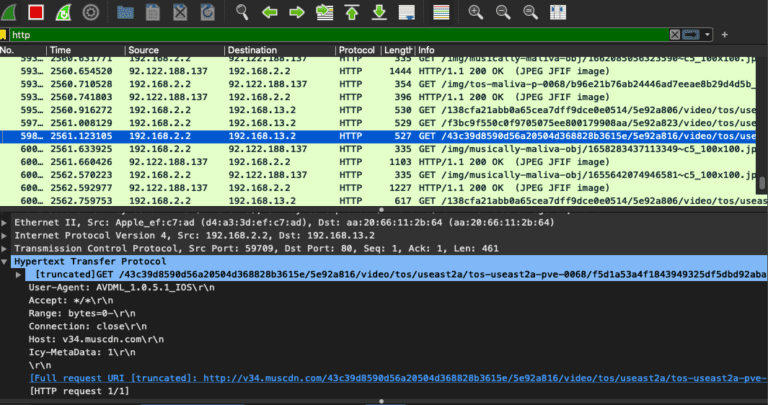
TikTok app uses insecure HTTP to process the data transfer, according to the analysis by researchers Talal Haj Bakry and Tommy Mysk the videos and images transferred are unencrypted.
An attacker between the “TikTok app and TikTok’s CDNs can easily list all the videos that a user has downloaded and watched, exposing their watch history.”
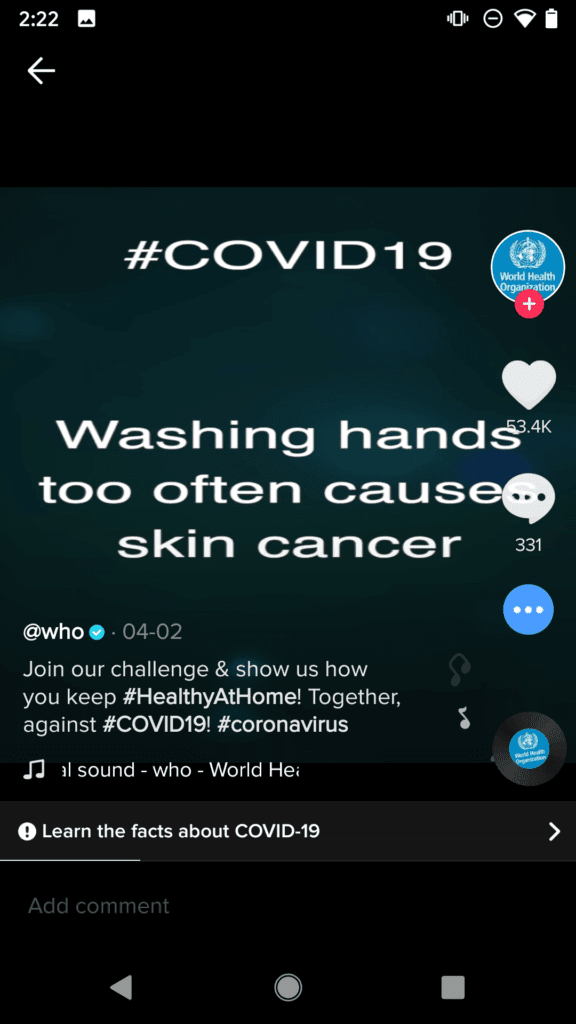
By launching a man-in-the-middle attacker can download the content and modify it, aiming to provide the fake facts in a spam video instead of the original one posted.
The vulnerability can be abused by an attacker to spread misleading information and change public opinion.
In their proof-of-concept attack, researchers set up a fake CDN server “v34[.]muscdn[.]com” and their TikTok app directed to the fake server. “The fake server then picks a forged video and returns it to the app which, in turn, plays the forged video to the user as shown in the demo video.”
TikTok for iOS (Version 15.5.6) and TikTok for Android (Version 15.7.4) are still using the connection unencrypted for connecting with TikTok CDN.
To launch this attack, threat actors need to have access to the router used to access the internet and TikTok. By having the access they can redirect and manipulate the videos.
“The circulation of misleading and fake videos in a popular platform such as TikTok poses huge risks,” researchers said.
The impact will be huge if the Wi-Fi operators, VPN providers, and ISPs configure the servers with the corrupt DNS server.
“We successfully intercepted TikTok traffic and fooled the app to show our videos as if they were published by popular and verified accounts,” researchers said.



.png
)
