Microsoft has removed two widely-used Visual Studio Code (VS Code) extensions, “Material Theme Free” and “Material Theme Icons Free,” from its marketplace after cybersecurity researchers discovered malicious code embedded within them.
These extensions, developed by Mattia Astorino (also known as equinusocio), had amassed nearly 9 million installations combined, with Astorino’s total extension downloads exceeding 13 million.
Following the removal, users received alerts notifying them that the extensions had been disabled for security reasons.
The investigation revealed that the malicious code was likely introduced through a compromised dependency or during a recent update.
This suggests a possible supply chain attack or unauthorized access to the developer’s account.
Researchers noted that themes like these should typically consist of static JSON files and not execute any code, making the presence of obfuscated JavaScript in the extensions a significant red flag.
Malicious Intent Uncovered
The malicious behavior was initially flagged by cybersecurity experts Amit Assaraf and Itay Kruk, who specialize in detecting harmful VS Code extensions.
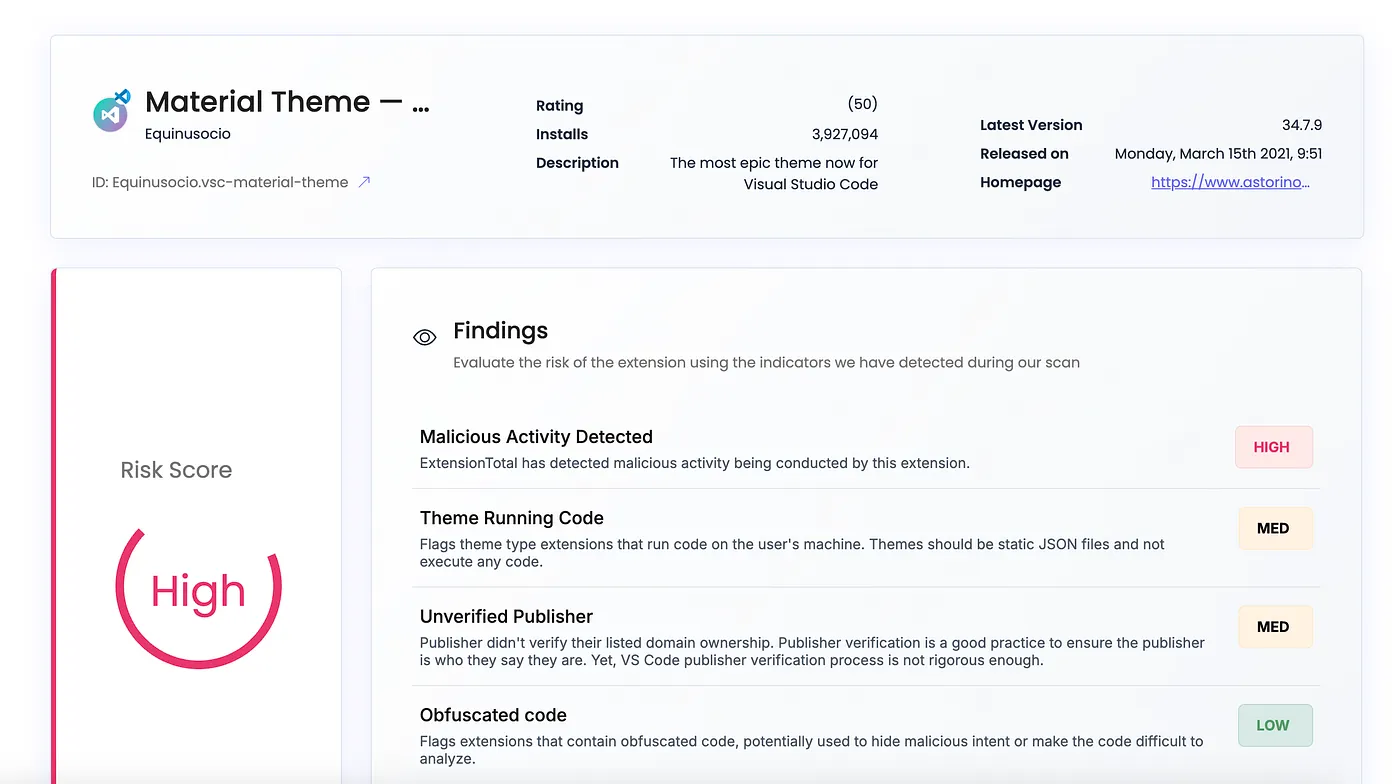
The analysis revealed heavily obfuscated JavaScript code in the extensions, which included references to usernames and passwords.
Although the exact purpose of this code remains unclear due to its complexity, its presence was sufficient to warrant immediate action by Microsoft.
Astorino has denied any intentional wrongdoing, attributing the issue to an outdated Sanity.io dependency used since 2016.
He criticized Microsoft for not notifying him before removing the extensions, claiming that fixing the dependency would have been a quick process.
However, Microsoft’s independent analysis corroborated the researchers’ findings, leading to the removal of all extensions associated with Astorino from the marketplace.
Potential Risks and Recommendations
The incident underscores the risks posed by malicious components in software supply chains.
Threat actors often exploit open-source platforms like VS Code Marketplace to distribute harmful code under the guise of legitimate extensions.
In this case, developers who installed these compromised extensions may have unknowingly exposed sensitive information or systems to potential breaches.
To mitigate risks, developers are advised to uninstall all extensions published by equinusocio, including:
- equinusocio.moxer-theme
- equinusocio.vsc-material-theme
- equinusocio.vsc-material-theme-icons
- equinusocio.vsc-community-material-theme
- equinusocio.moxer-icons.
This incident highlights the importance of scrutinizing third-party dependencies and maintaining robust supply chain security practices.
Developers should regularly audit their tools and avoid extensions with suspicious or obfuscated code.
Collect Threat Intelligence on the Latest Malware and Phishing Attacks with ANY.RUN TI Lookup -> Try for free



.png
)
