Winnti group has been active at least since 2012 and specializes in cyberattacks against the online video game industry. The main goal of the hacker group is to steal the source code of online game projects as well as digital certificates.
The group is also responsible for high-profile supply-chain attacks against software companies that result in the distribution of trojanized software.
Winnti Group Attacks
Starting from 2019, the Winnti group started using PipeMon malware since 2019, to compromise various software companies.
ESET researchers observed that the current campaign targets video game developers who developing MMO (Massively Multiplayer Online) games based in South Korea and Taiwan.
The attacker tries to compromise the company’s build orchestration server which allows attackers to take control of the automated build systems. This would allow attackers to include arbitrary code of their choice in the video game executables.
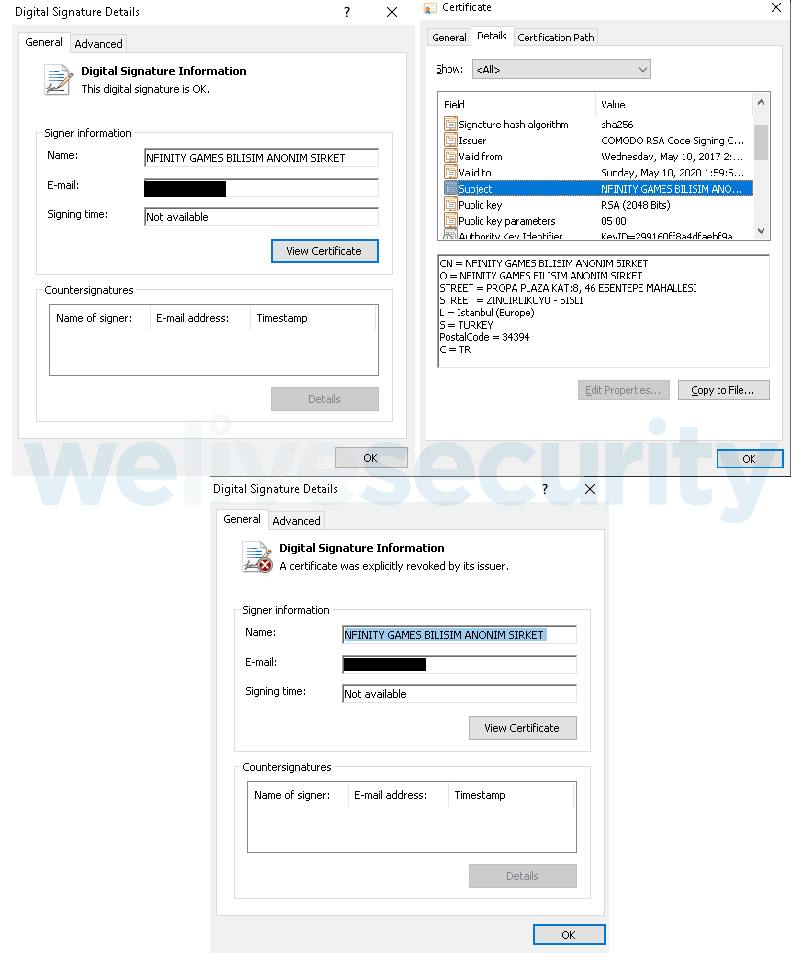
ESET observed that the certificate used to sign the PipeMon installer, modules, and additional tools is linked to a video game company that was compromised in a supply-chain attack in late 2018 by the Winnti Group and was likely stolen at that time.
The first stage of the malware is a password-protected RARSFX executable and the password is different from each sample.
Once the password-protected file sis extracted, setup.exe main executable get’s executed, it’s purpose is to load the setup.dll file.
Following are the files with RARSFX
- rLnc.dat – Encrypted payload
- Duser.dll – Used for UAC bypass
- osksupport.dll – Used for UAC bypass
- PrintDialog.dll – Used for the malicious print processor initialization
- PrintDialog.exe – Legitimate Windows executable used to load PrintDialog.dll
- setup.dll – Installation DLL
- setup.exe – Main executable
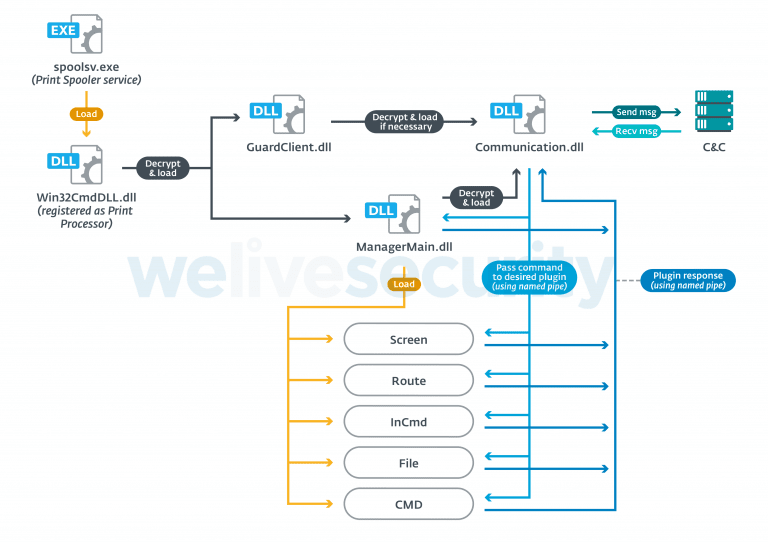
To maintain the persistence setup.dll registers the malicious DLL loader as an alternative Print Processor by adding registry keys.
Once it got registered it restarts the print spooler service (spoolsv.exe) so that the malicious DLL loader loads every time when spoolsv.exe starts.
C&C Communication
The module was named PipeMon as it contains inter-module communication, to its PDB path, and the name of the Visual Studio project named by developers.
ESET researchers observed that “Inter-module communication is performed via named pipes, using two named pipes per communication channel between each individual module, one for sending and one for receiving.”
The communication module with loader responsible for establishing C&C communication, all the data transferred are encrypted using RC4 with the hardcoded key Com!123Qasdz.
To initiate C&C communication following are the details shared first includes;
- OS version
- Physical addresses of connected network adapters concatenated with %B64_TIMESTAMP%
- the victim’s local IP address
- backdoor version/campaign ID; we’ve observed the following values
- “1.1.1.4beat”
- “1.1.1.4Bata”
- “1.1.1.5”
- Victim computer name
The malware modules are signed with Stolen valid code-signing certificate, now the certificate was revoked by the user after notification from ESET.
The new attack shows that Winnti Group uses a new set of tools using multiple open-source projects and they are targeting Massively Multiplayer Online developer companies.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity, and hacking news updates.



.png
)
