Researchers discovered new malicious Android apps from Google Play Store bypassing SMS-based two-factor authentication (2FA) mechanisms and steal the OTP without SMS’s permission.
Google recently restrict other apps to use of high risk or sensitive permissions, including the SMS or Call Log in March 2019 that leads malware and credentials stealing apps lost its permissions.
Newly uncovered malicious apps using a novel technique to bypassing SMS 2FA messages without using SMS permissions, eventually steal the OTP by evading the new permission restriction.
Threat actors also using the technique to obtain OTPs from some email-based 2FA systems.
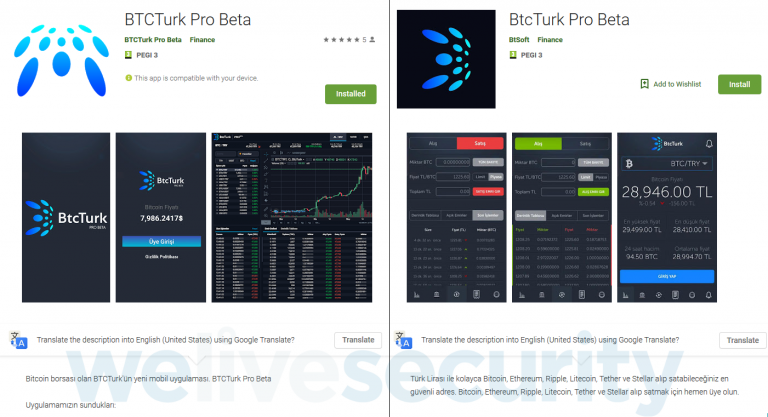
Malicious apps in Google play store called “BTCTurk Pro Beta,” “BtcTurk Pro Beta” under the developer name “BTCTurk Pro Beta and BtSoft” impersonate the Turkish cryptocurrency exchange BtcTurk and fool users to steal login credentials to the service.
BtcTurk is a Turkish cryptocurrency exchange; its official mobile app is linked to the exchange’s website and only available to users in Turkey.
Unlike other malicious apps that are intercepting SMS messages to bypass 2FA protection on users’ accounts and transactions, these apps stealing the OTP from the notification bar and also it cleverly dismiss the notification to divert victims from noticing fraudulent transactions happening.
2FA Bypass Technique
First App “BTCTurk Pro Beta” was uploaded to Google Play on June 7, 2019, and the App was installed nearly 50 users.
Within the next five day, another malicious app was uploaded in Google play store with similar tactics of the first one.
Threat actors later removed the second app and uploaded another app with the same functionality with the name of “BTCTURK PRO” with the same Icon and same developer name.
Once the app installed on victims device, initially it requests permission named Notification access, once allowed, it gains an ability to read all the notifications displayed by the other apps and dismiss the notification.
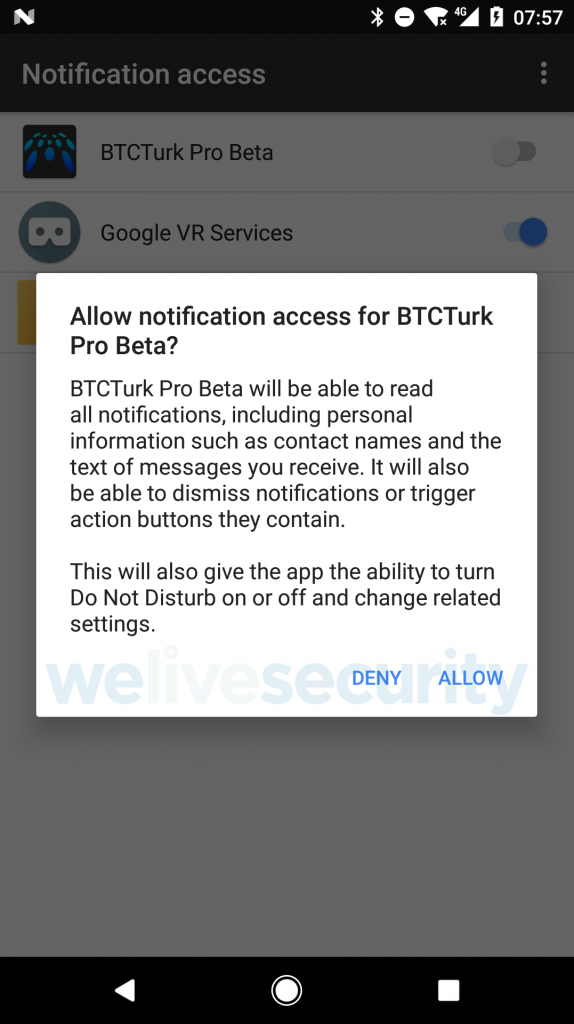
Since the notification access permission was introduced in Android version 4.3 (Jelly Bean), all the higher version of 4.3 is reportedly affected, which means it could affect around 90% of Android devices.
Once the permission granted by the user, the app instantly displays the fake login page and request to BtcTurk login credentials.
According to ESET research, After the user entered the credentials The English translation of the message is: “Opss! Due to the change made in the SMS Verification system, we are temporarily unable to service our mobile application. After the maintenance work, you will be notified via the application. Thank you for your understanding.”
In the background, stolen credentials are sent to attacker server, and also the developer of the malicious apps target only notifications from apps whose names contain the keywords “gm, Yandex, mail, k9, outlook, SMS, messaging”,
“The displayed content of all notifications from the targeted apps is sent to the attacker’s server. The content can be accessed by the attackers regardless of the settings the victim uses for displaying notifications on the lock screen.” ESET reported.
Mitigation Steps Suggested by ESET
- Only trust cryptocurrency-related and other finance apps if they are linked from the official website of the service
- Only enter your sensitive information into online forms if you are certain of their security and legitimacy
- Keep your device updated
- Use a reputable mobile security solution to block and remove threats; ESET systems detect and block these malicious apps as Android/FakeApp.KP
- Whenever possible, use software-based or hardware token one-time password (OTP) generators instead of SMS or email
- Only use apps you consider trustworthy, and even then: only allow Notification access to those that have a legitimate reason for requesting it
Indicators of Compromise (IoCs)
| Package name | Hash |
| btcturk.pro.beta | 8C93CF8859E3ED350B7C8722E4A8F9A3 |
| com.app.btsoft.app | 843368F274898B9EF9CD3E952EEB16C4 |
| com.app.elipticsoft.app | 336CE9CDF788228A71A3757558FAA012 |
| com.koinks.mobilpro | 4C0B9A665A5A1F5DCCB67CC7EC18DA54 |
Related Read
New Android Malware that Uses Chrome to Load Malicious websites through Notifications
Bypassing and Disabling SSL Pinning on Android to Perform Man-in-the-Middle Attack



.png
)
