Security researchers from ZecOps discovered two zero-day vulnerabilities with default email mailing app present in Apple iPhones and iPads let attackers take over the devices by just sending an email.
The vulnerability has been exploited by attackers since at least January 2018, targeting iOS high-profile users.
An attacker could exploit the vulnerability by sending a specially crafted email to a victim’s mailbox enabling it to trigger vulnerability with the context of the email application with iOS MobileMail application on iOS 12 or maild on iOS 13.
It affects all the devices above iOS 6 and unable to confirm with earlier versions as they are not available in the market. The vulnerability affects iOS 13.4.1 also.
Two zero-day Vulnerabilities
The flaw resides with the implementation of MFMutableData present in the MIME library that lacks checking ftruncate() that leads to the Out-Of-Bounds write.
Researchers also found a way to trigger OOB-Write without waiting to fail for ftruncate and also found a heap overflow that can be triggered remotely.
The vulnerability can be triggered even before the email downloaded is complete, so the email doesn’t reside in the device.
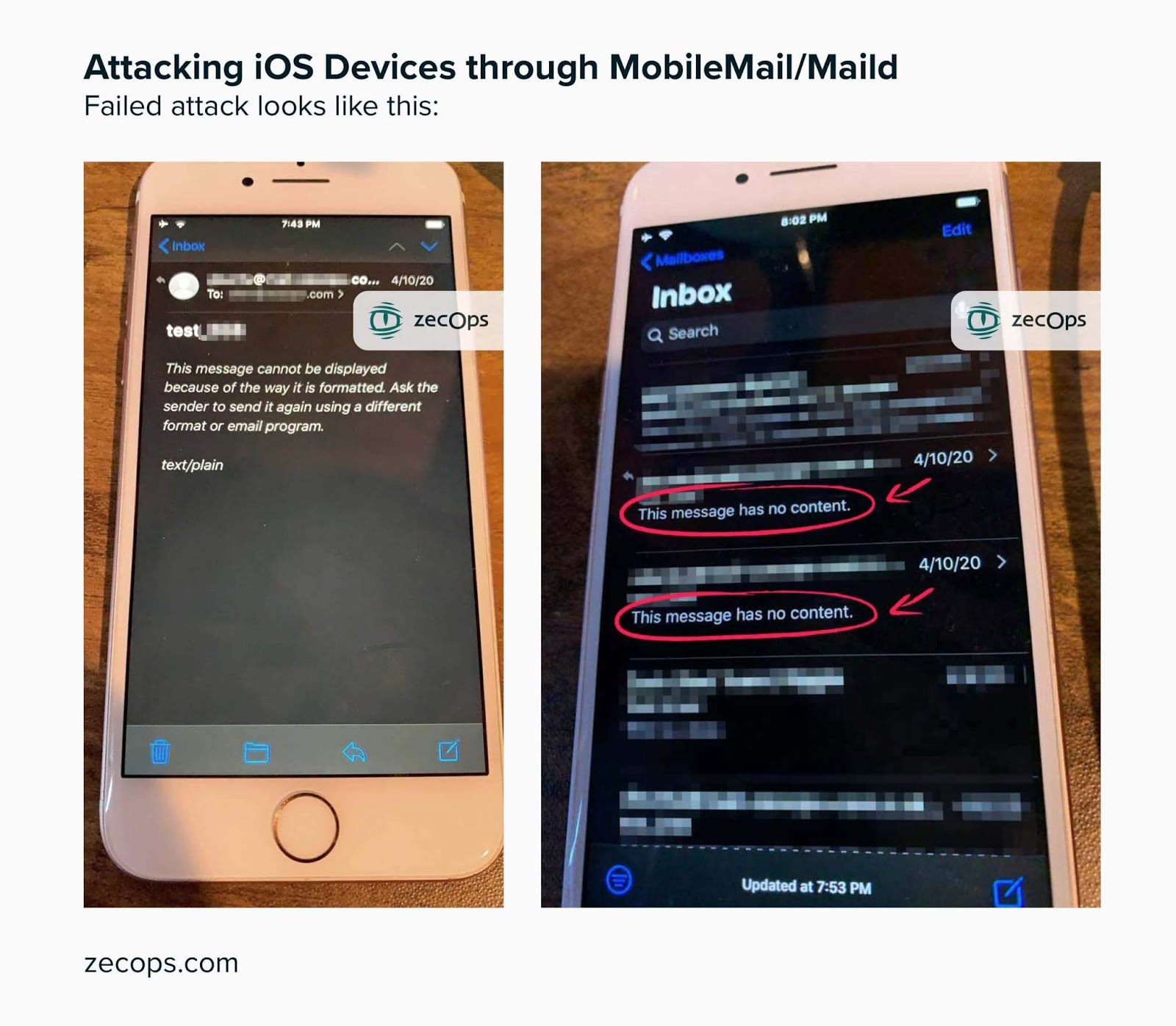
In case if the attack is failed then a message stating “This message has no content” sent to the attacker.
With iOS 13 the vulnerability can be triggered without user interaction, and on iOS 12 users need to click on the email to get hacked.
Successful exploitation of the vulnerability allows attackers to leak, modify, and delete emails, chaining with kernel vulnerabilities allow attackers to get complete remote access.
If the vulnerability exploited on the device, then users a temporary slowdown of a mobile mail application, and no other anomalous behavior observed.
The vulnerability was discovered by the researchers on February 19th, 2020 and it has been fixed newly released beta update of 13.4.5.
If you are unable to update then it is recommended to switch with other email clients not vulnerable to these bugs.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
Over 3.5 Million iPhone & iPad Users Installed Malicious Fleeceware from Apple’s App Store
Apple Agrees To Pay $500 Million in Settlement For Slowing Down The Older iPhones to Buy New Models



