A threat actor is selling account databases containing a total of 34 million user records that they claim were stolen from seventeen companies during data breaches.
This was first advertised on October 28th by a data breach broker, who created a new topic on a hacker forum to sell the stolen user databases for seventeen companies.
“Selling Exclusive private databases. These databases are fresh and have never been sold before. Limited sales”
This has gone viral now, questioning what information would be included in this sale?
Who is responsible for the data breaches?
The Seller has been clear to their point that they were not responsible for hacking into the seventeen companies and is only acting as a broker for the databases.
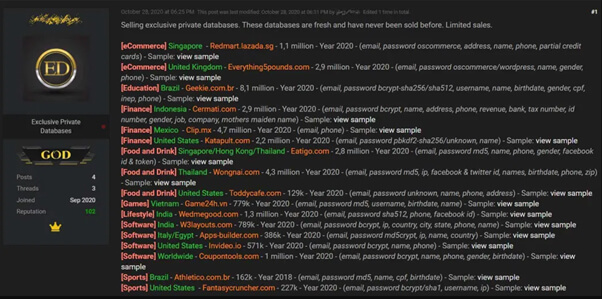
Also, according to the Seller, the account databases are the results of data breaches that took place in 2020, but none of the affected companies have disclosed security breaches prior to this week.
Companies and Data which had Supposedly breached in 2020
It is important to know that all of the seventeen databases being sold were obtained in 2020, and data like phone numbers, credit card information, email, passwords and SHA256/512,md5crypt and bcrypt passwords, etc are likely to be disclosed.
According to the seller, the following information is exposed per breach:
- Redmart.lazada.sg: emails, SHA1 hashed passwords, mailing and billing addresses, full name, phone numbers, partial credit cards numbers and exp dates
- Everything5pounds.com: emails, hashed passwords, name, gender, phone number
- Geekie.com.br: emails, bcrypt-sha256/sha512 hashed passwords, usernames, names, DoB, gender, mobile phone number, Brazilian CPF numbers
- Cermati.com: – emails, password bcrypt, name, address, phone, revenue, bank, tax number, id number, gender, job, company, mothers maiden name
- Clip.mx: email, phone
- Katapult.com: email, password pbkdf2-sha256/unknown, name
- Eatigo.com: email, password md5, name, phone, gender, facebook id & token
- Wongnai.com: email, password md5, ip, facebook & twitter id, names, birthdate, phone, zip
- Toddycafe.com: email, password unknown, name, phone, address
- Game24h.vn: email, password md5, username, birthdate, name
- Wedmegood.com: email, password sha512, phone, facebook id
- W3layouts.com: – email, password bcrypt, ip, country, city, state, phone, name
- Apps-builder.com: email, password md5crypt, ip, name, country
- Invideo.io: email, password bcrypt, name, phone
- Coupontools.com: email, password bcrypt, name, phone, gender, birthdate
- Athletico.com.br: email, password md5, name, cpf, birthdate
- Fantasycruncher.com: email, password bcrypt/sha1, username, ip
Safer Precaution
If you are a user of one of these sites, it is suggested to change your password and it is also advisable to change the password of all other sites if you are likely to be using the same password everywhere.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
VOIP Service Provider Exposes 350M Customer Records
Food Delivery Platform Hacked – More than 400K Customer Impacted


