Attackers are found to be exploiting Oracle WebLogic Servers via CVE-2020–14882 to install Cobalt Strike which will allow persistent remote access to the compromised devices.
Testing the vulnerability
The latter half of last week saw a flurry of scans against Oracle’s WebLogic Server to check the vulnerability of CVE-2020-14882.
It is important to note that CVE-2020-14882 was patched a couple of weeks back and this was covered by us in great detail.
In addition to the scans searching for vulnerabilities, it was found to be a few attempting to install crypto-mining tools.
On Friday, Oracle amended its patch for CVE-2020–14882 [2]. A new variation of the vulnerability (CVE-2020–14750) can be used to exploit WebLogic servers with a trivial modification of the exploit code.
What is a Cobalt Strike?
Cobalt Strike is a legitimate penetration testing tool that is used by threat actors in the post-exploitation tasks and to deploy beacons that enable them to gain continuous remote access.
This later allows them to access the compromised servers to harvest data and to deploy the second stage of malware payloads.
How did the attack happen?
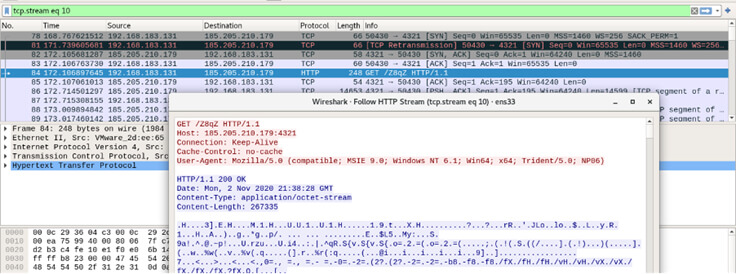
The attackers are using a chain of base64-encoded Powershell scripts to download and install Cobalt Strike payloads on unpatched Oracle WebLogic servers.
Cobalt Strike is normally used to detect system penetration but though the tool is intended to do good, cybercriminals have used this tool for malicious intents and purposes.
The Cisco Talos Q4 2020 CTIR report states that of all the ransomware attacks this quarter, 66% of them involved the use of Cobalt Strike
The result of this operation is a shellcode to download and execute a Cobalt Strike payload.
Immediate Action advised
As both CVE-2020-14882 and CVE-2020-14750 can easily be exploited by unauthenticated attackers to take over vulnerable WebLogic servers, Oracle advises companies to immediately apply the security updates to block attacks.
The Cybersecurity and Infrastructure Security Agency (CISA) also urged administrators to apply the security update as soon as possible to address the two critical vulnerabilities.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
