Researchers discovered a new Android malware “Cerberus” that is being rented (Malware-as-a-service) on underground forums for the last two year and the malware used for various private operation.
Unlike other banking trojans such as Anubis that derives the code from other banking trojans, Cerberus developed for several years from scratch and is not using any trojan parts and code.
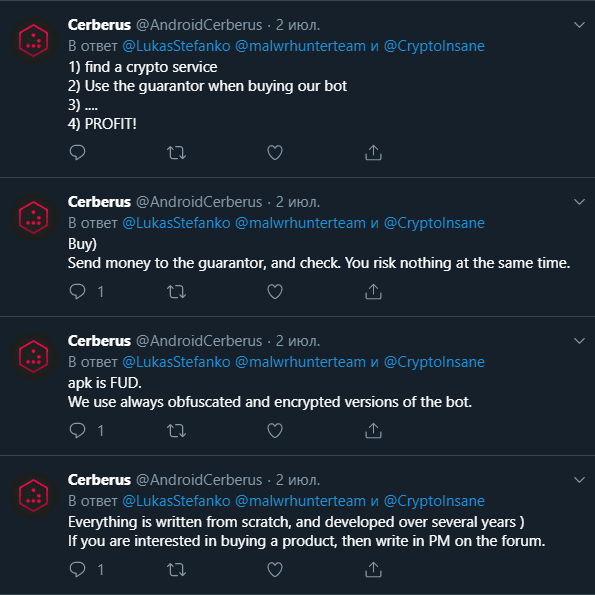
Malware author or threat group who developed this Android malware Cerberus has made a public statement on official twitter account about the malware features, share the Virustotal detection screenshot, promotional videos, and also directly community with security researcher anonymously.
Researchers believe that this kind of unusual behavior for seeking attention and growing the malware rental business.
Before Cerberus, another famous rental malware RedAlert, and Anubis was being sold in underground forums but the life span of this rental malware is less likely no more than 2 years.
“Due to this Cerberus will come in handy for actors that want to focus on performing fraud without having to develop and maintain a botnet and C2 infrastructure”
Cerberus developers using obfuscation technique to evade the detection and protect from analyzing the trojan.
Cerberus Android Malware Infection Process
Once the malware infects the device, it hiding the icon and requesting the permission for the accessibility service privilege.
After gaining the Accessibility service, Cerberus granting the additional privileges such as send messages, make calls without any further user interaction.
During the installation process, it also disables the Google play protect to prevent the detection and gain additional permission to register the infected device with its botnet and waiting for commands from the controller of the malware.
According to Threat Fabric research, Cerberus can perform the following attack without detecting by the security software.
Overlaying: Dynamic (Local injects obtained from C2)
Keylogging
SMS harvesting: SMS listing
SMS harvesting: SMS forwarding
Device info collectionContact list collection
Application listing
Location collection
Overlaying: Targets list update
SMS: Sending
Calls: USSD request making
Calls: Call forwarding
Remote actions: App installing
Remote actions: App starting
Remote actions: App removal
Remote actions: Showing arbitrary web pages
Remote actions: Screen-lockingNotifications: Push notifications
C2 Resilience: Auxiliary C2 list
Self-protection: Hiding the App icon
Self-protection: Preventing removal
Self-protection: Emulation-detection
Architecture: Modular
It is also capable of launch an overlay attack to trick victims to give away sensitive details such as credit card information, banking credentials, mail credentials, and more.
“Even though Cerberus have sold in underground forums with a variety of features, it doesn’t contain a full-blown set of Android banking malware features (such as RAT, RAT with ATS (Automated Transaction Script), back-connect proxy, media streaming), or providing an exhaustive target list, Cerberus should not be taken lightly”. researchers said.
Sponsored: – Manage all the Endpoint networks from a single Console.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity course online to keep yourself updated.



.png
)
