Researchers observed a new malware family in May involved in various cyberespionage campaigns advertised as a chat app dubbed “Chatrious” downloaded from the malicious website by clicking the download button on the site.
The campaign back in action again with a different app called “Apex App”, that steals the user’s infection on the affected device. Trend Micro detected the threat as AndroidOS_CallerSpy.HRX.
CallerSpy Malware Distribution
CallerSpy distributed as a chat app when the app launched in the victim device connects with the C&C server via Socket.IO and to monitor commands from the C&C server. Also, it schedules new tasks by using Evernote for stealing information.
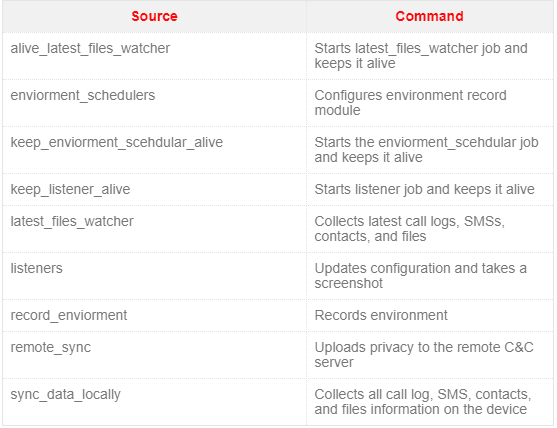
The malware is capable of stealing various information such as call logs, SMSs, contacts, and files on the device. It also takes screenshots of the infected device and later sends it to the C&C server.
According to Trend Micro research “The malware creates a local storage on the infected device and they will be uploaded to the C&C server periodically, it looks for the following file formats in the infected device that includes jpg, jpeg, png, docx, xls, xlsx, ppt, pptx, pdf, doc, txt, csv, aac, amr, m4a, opus, wav, and amr.”
All the collected data encoded as Base64 and the data uploaded to the C&C server. To trick the users the threat actors used typo squatted domain gooogle[.]press.
Researchers able to find four C&C IP addresses hosted on the legitimate service and they are connected with port 3000. The malicious app doesn’t provide any user interface (UI) and it uses only the default android app icon labeled as the rat.

The download section of the malicious page provides options to download the app indicating Apple, Android and Windows platforms. But now the app supports only for the Android device.
The good news is that the app is not available to download from the play store and the victims of the malware are still unclear.



