A Chinese technology firm has been siphoning text messages and call records from cheap Android-based mobile smart phones and secretly sending the data to servers in China, researchers revealed this week.
Often retailing for between $50 and $100, the sleek and powerful devices sell so cheaply because they also require the user to accept on-screen advertisements.
According to research released this week, the low up-front cost of these smart phones may be subsidized not just by ads but by also by the theft of private information stolen from users.
The revelations came the same day the White House and the U.S. Department of Homeland Security issued sweeping guidelines aimed at building security into Internet-connected devices, and just hours before a key congressional panel sought recommendations from industry in regulating basic security standards for so-called “Internet of Things” (IoT) devices.
Researchers at Fairfax, Va.-based security firm Kryptowire say the ADUPS software gives the company near-total control over the devices that it runs on, and that they have proof ADUPS has abused that control to siphon personal data from countless consumers
The ADUPS technology is typically bundled with smart phones made by dozens of global wireless firms including ZTE, BLU and Huawei, and sold at popular consumer destinations like Amazon and BestBuy.
According to research released this week, the low up-front cost of these smart phones may be subsidized not just by ads but by also by the theft of private information stolen from users.
Researchers at Fairfax, Va.-based security firm Kryptowire say the ADUPS software gives the company near-total control over the devices that it runs on, and that they have proof ADUPS has abused that control to siphon personal data from countless consumers.
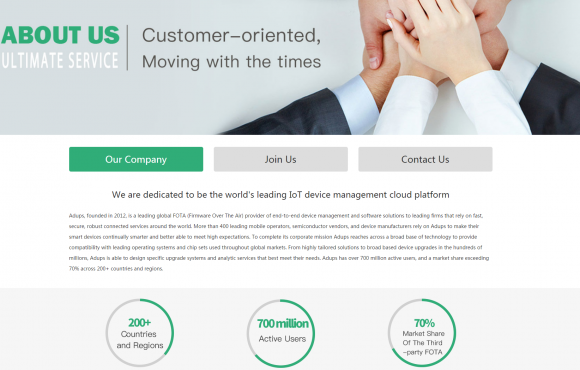
In September 2016, Adups claimed on its web site to have a world-wide presence with over 700 million active users, and a market share exceeding 70% across over 150 countries and regions with offices in Shanghai, Shenzhen, Beijing, Tokyo, New Delhi, and Miami.
The web site also stated that it produces firmware that is integrated in more than 400 leading mobile operators, semiconductor vendors, and device manufacturers spanning from wearable and mobile devices to cars and televisions.
Comparison of Adups with 2011 CarrierIQ capabilities based on publicly available sources.

ADUPS claims on its Web site to have worldwide presence with more than 700 million active users, and that its firmware is integrated into “more than 400 leading mobile operators, semiconductor vendors and device manufacturers spanning from wearable and mobile devices to cars and televisions.”
“This is just one random device of theirs that we looked at,” Benameur said. “For a company that claims to provide over-the-air updates for 700 million devices, including cars and millions of IoT devices…this is really scary and unacceptable behavior.”
.webp?w=696&resize=696,0&ssl=1)