A severe Remote Code Execution (RCE) vulnerability in pgAdmin (CVE-2025-2945), the popular PostgreSQL database management tool, has been patched after researchers discovered attackers could hijack servers through malicious API requests.
The flaw affects pgAdmin versions ≤9.1 and allows authenticated users to execute arbitrary commands on affected systems.
Technical Breakdown
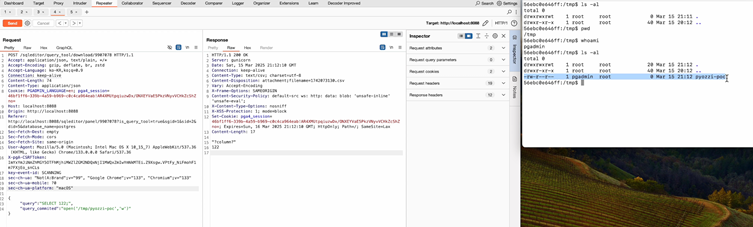
The vulnerability stems from improper use of Python’s eval() function in two endpoints:
- /sqleditor/query_tool/download/<int:trans_id>
query_commited = eval(value) if isinstance(value, str) else value # Vuln codeAttackers could send crafted POST requests containing Python code (e.g., open(‘/tmp/pyozzi-poc’, ‘w’)) to write files or execute commands.
- /cloud/deploy
high_availability = 'REGIONAL' if eval(args.high_availability) else 'ZONAL' # Vuln codeMalicious inputs like reverse shell payloads could grant full server access:
exec('import socket,subprocess,os;s=socket.socket(...)')Both endpoints processed user input without sanitization, enabling attackers to abuse the eval() function’s ability to execute code.
Attack Scenarios & Impact
Successful exploitation could lead to:
- Database Manipulation: Theft or destruction of sensitive PostgreSQL data.
- Lateral Movement: Compromise of internal networks via server access.
- Credential Theft: Extraction of API keys, passwords, and tokens from configuration files.
- Persistent Backdoors: Installation of malicious scripts for long-term access.
Notably, the flaw requires authentication, limiting immediate widespread exploitation. However, compromised accounts or phishing attacks could bypass this barrier.
Patch & Remediation
The pgAdmin team resolved the issue in version 9.2 by eliminating eval() usage. For example, in the query_commited parameter patch:
- query_commited = eval(value) if isinstance(value, str) else value + query_commited = value.lower() == 'true' # Secure boolean parsing Users must update to pgAdmin 9.2 immediately. Organizations unable to patch should restrict pgAdmin instance access to trusted networks and audit user privileges.
The bug hunter who discovered the flaw noted:
“Why use eval() here? The logic didn’t need it at all. This was an avoidable risk.”
The pgAdmin security team addressed the report within 24 hours, highlighting the importance of coordinated disclosure.
Find this News Interesting! Follow us on Google News, LinkedIn, & X to Get Instant Updates!



.png
)
