A researcher discovered a critical vulnerability in Citrix Application Delivery Controller (NetScaler ADC) & Citrix Gateway (NetScaler Gateway) let external hackers access to the company’s local network remotely.
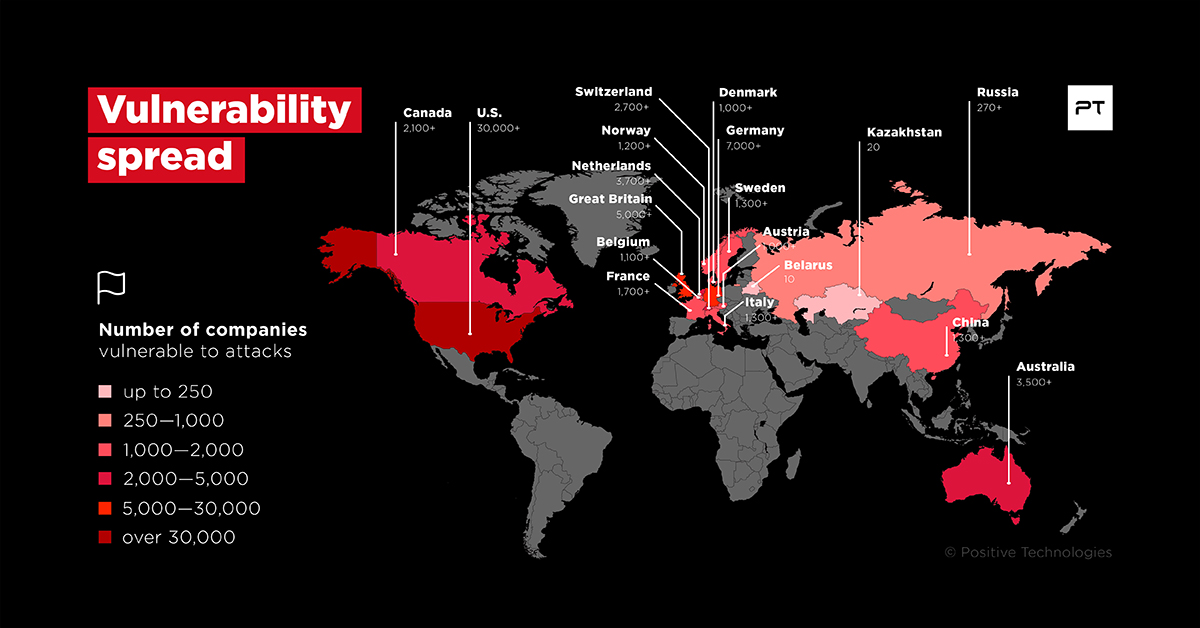
Experts believe that at least 80,000 companies could have affected around the globe including the United States with over 38 percent of all vulnerable organizations, the UK, Germany, the Netherlands, and Australia.
The Delivery Controller is the server-side component that is responsible for managing user access, plus brokering and optimizing connections. Controllers also provide the Machine Creation Services that create desktop and server images.
The vulnerability can be tracked as CVE-2019-19781, and the vulnerability severity is “high” which creates a serious threat to the organization deployed with Citrix Application Delivery Controller and gateway.
This vulnerability affects all supported versions of the product, and all supported platforms, including the following:
- Citrix ADC and Citrix Gateway 13.0
- Citrix ADC and NetScaler Gateway 12.1
- Citrix ADC and NetScaler Gateway 12.0
- Citrix ADC and NetScaler Gateway 11.1
- Citrix NetScaler ADC and NetScaler Gateway 10.5.
According to Positive Technologies report, The vulnerability affects the company depends on the specific configuration, and it allows any unauthorized attacker to not only access published applications but also attack other resources of the company’s internal network from the Citrix server,
According to Dmitry Serebryannikov from PT, “Citrix applications are widely used in corporate networks. This includes their use for providing terminal access of employees to internal company applications from any device via the Internet. Considering the high risk brought by the discovered vulnerability, and how widespread Citrix software is in the business community, we recommend information security professionals take immediate steps to mitigate the threat,”
Citrix security bulletin Report said CTX267027: A vulnerability in Citrix Application Delivery Controller (ADC), formerly known as NetScaler ADC, and Citrix Gateway, formerly known as NetScaler Gateway, that could lead to arbitrary code execution.”
To avoid such attacks, companies are recommended to use web application firewalls.
Also Read: Unpatched Dropbox for Windows Zero-Day Bug Let Hackers get SYSTEM Privileges



.png
)
