DeathRansom – A new ransomware strain that evolves from no encryption to using a combination of encryption algorithms to encrypt files.
The ransomware strain observed first in earlier November, it pretends to encrypt files, but it only appends the extension, users able to recover the files by just removing the extension.
Researchers from Fortinet observed that the threat is evolving and uses a combination of algorithms to encrypt files.
DeathRansom Ransomware
Like other ransomware, it enumerates and encrypts files on local and network drives. It avoids encrypting important folders such as (Program Files, Windows, etc) and system files.
Before encryption, the ransomware performs language checks if the system is from Eastern European countries then it avoids encrypting.
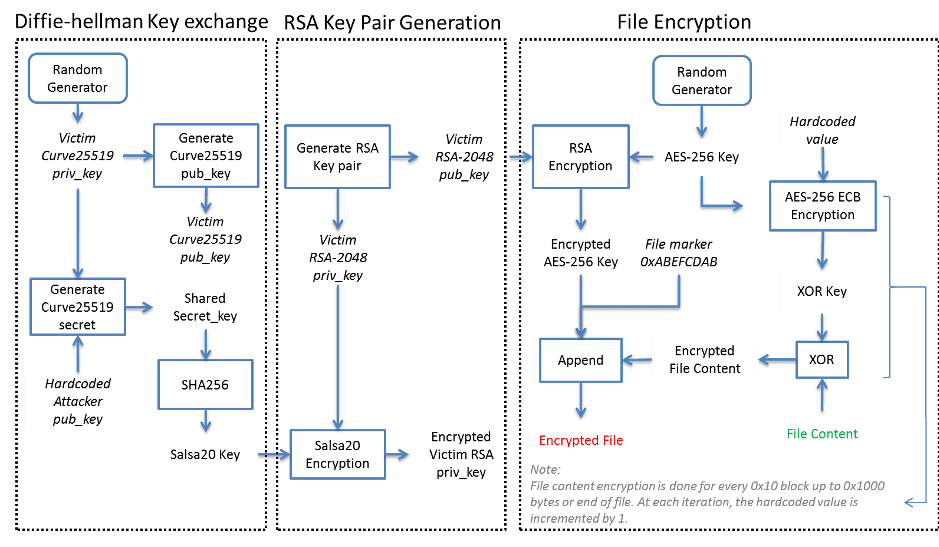
The New version capable of encryption includes “a combination of Curve25519 algorithm for the Elliptic Curve Diffie-Hellman (ECDH) key exchange scheme, Salsa20, RSA-2048, AES-256 ECB, and a simple block XOR algorithm to encrypt files,” reads Fortinet blog post.
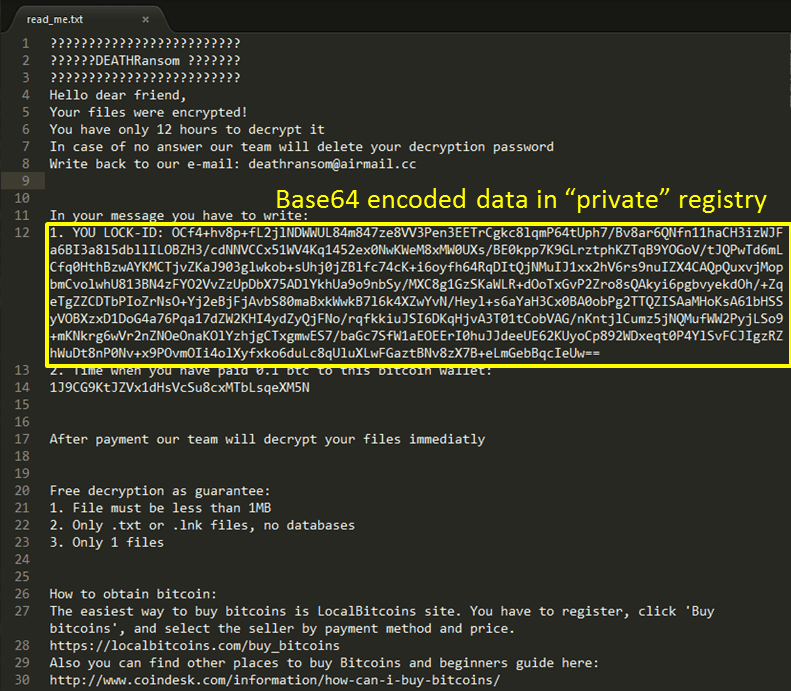
Once the encryption process completed it drops a ransom note and it includes a lock-ID unique to every user.
The samples observed by researchers found to be compiled on a machine that has the Slovak language installed by default. Most of the samples downloaded from the hacked .es, but one sample is from a different URL.
This gives a lead to researchers, the link contains a profile “scat01”, further analysis reveals it has a connection to Vidar stealer malware family.

So researchers decided to look for the malware associated with profile “scat01”, the number of malware samples found to be associated that includes;
- DeathRansom
- Vidar stealer
- Azorult stealer
- Evrial stealer
- 1ms0rryStealer
- Supreme miner
All the samples found to be purchased on Russian underground forums, so researchers started searching for “scat01” and “Vidar” on underground forums, several posts found associated with profile “scat01”. More details of attribution can be found here.

DeathRansom is a new ransomware strain, and the actor behind ransomware continues to implement new features. “Researchers believe the user with the nickname “scat01″ could be responsible for the latest DeathRansom attack.”
Also Find: Ransomware Attack Response and Mitigation Checklist



.png
)