A new flaw discovered with the Facebook Messenger app for Windows lets attackers hijack a call for a resource with messenger code to run the malware.
The flaw was discovered by Reason Labs researchers with Facebook Messenger app, Version 460.16 and now it was fixed with version 480.5.
Facebook Messenger app used for Persistence
It was observed that with messenger app supplied a strange call to Powershell.exe from the Python27 directory. This directory can be accessed without admin privileges.
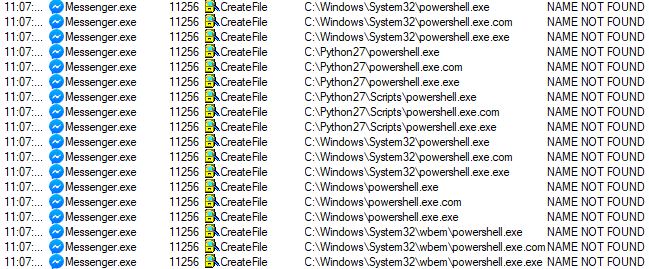
On observing that researchers decided to reverse shell with msfvenom and a listener with Metasploit. A new payload was created and the name changed to Powershell.exe to hijack the messenger app call.

Then researchers got executed the “Messenger” application on the machine and got the reverse shell connection.

For a malware infection, chain persistence is more important, an attacker needs to make sure that he should not lose the connection with the target machine.
Using the persistence on the system malware author can also use the effected system to exploit the other system in the local network or the remote location.
The complexity of the persistence method defined by the attackers based on the privileges of the target machine.
Due to this Covid-19 situation, people started spending more time online than ever before, the usage of mobile and desktop chat applications increases at least by 40%. Facebook alone reported a 70% increase in time and time with messenger increases by 50%.
Starting this coronavirus pandemic, many companies around the world asked employees to work from home, which increases the usage of video conferencing apps and other social media apps.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
