Gustuff banking malware returns with new features, the threat actors behind Gustuff malware made changes with distribution hosts and disabled C2 infrastructure. The malware uses SMS messages for propagation.
The Gustuff malware is a fully automated one, the malware is capable of stealing login credentials by abusing Accessibility Services in Android devices.
Researchers observed that the latest version of Gustuff uses a “poor man scripting engine” based on JavaScript language, which provides an ability to execute scripts while using its internal commands backed by the power of JavaScript language. This is very innovative in the Android malware space.”
Gustuff Malware Campaigns
Talos researchers first observed the new campaign around June 2019, the campaign uses Instagram to trick the users into downloading the malware. The malware campaign uses SMS messages as the primary method to infect users.
A new wave of the campaign observed starting this month, just like the June campaign. The malware primarily observed targets Australian banks and digital currency wallets. But the new campaign targets Australia based hiring sites’ mobile apps.

As the campaign based only on SMS, the malware-hosting domains receive only a few hits.
“This method of propagation has a low footprint since it uses SMS alone, but it doesn’t seem to be particularly effective, given the low number of hits we’ve seen on the malware-hosting domains.”
Malware Activation Cycle
The malware attempts creating an uu.dd in the external storage, which has a UUID value and the value is used as ID for the C2 server. It pings with C2 at a predetermined interval and will get commands for execution.
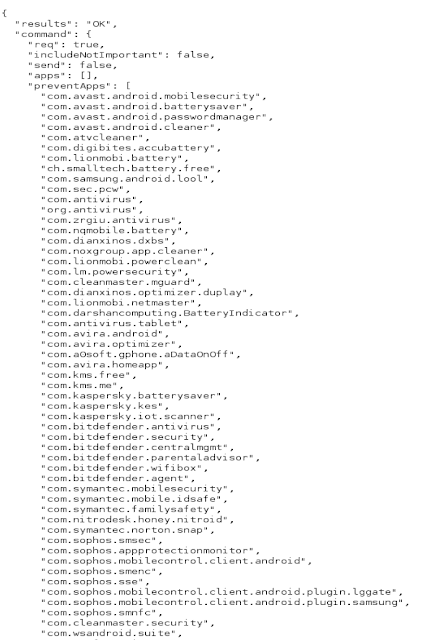
It checks for the list of apps installed and blocks the list of anti-virus/anti-malware software present in the below list.
The malware sends commands requesting credit card information, but it won’t present a form to enter the details, instead, it leverages the Android Accessibility API to harvest it.

The malware was initially designed to target only as a banking trojan, later it’s capabilities are expanded to target crypto services, online stores, payment systems, and messengers.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
