India’s leading outsourcing giant, Wipro, confirmed the security breach earlier this month as the company Employees’ were subjected to very advanced phishing activity.
According to Flashpoint analysis, the attackers used many of the legitimate security applications used by penetration testers. The attackers used a remote access tool, Powerkatz, and Powersploit in the campaign.
“The ScreenConnect is a remote access tool that used to provide desktop support or for remote meetings and the Powerkatz is the PowerShell version of Mimikat used in post-exploitation. Another tool is the Powersploit, a collection of PowerShell modules used for penetration-testing engagements.”
KrebsOnSecurity reported that the attackers responsible for phishing campaigns compromised more than 100 computer system and they also targeted Infosys and Cognizant.
The threat actors ultimate aim is to gain access to the portals, in multiple industries that use to manage gift card and rewards programs.
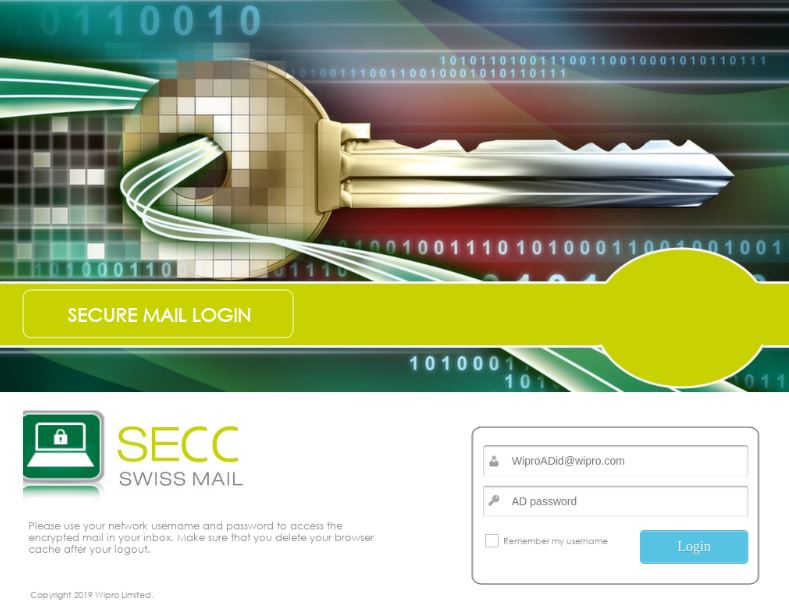
Flashpoint determines that phishing domains are used as a primary attack vector, the phishing domain hosting templates lure victims to enter their Windows usernames and passwords in order to allegedly access encrypted email.
Further investigation reveals another malware Imminent Monitor, a remote administration tool distributed through Word document. “The document contained a URL that redirected to a file hosted at flexmail[.]tv, which appeared to have been used multiple times to deliver documents and payloads in other campaigns.”
“We assess with high confidence that the threat actors are linked to the 2017 phishing campaign. Overlapping infrastructure was configured to utilize the resources of multiple servers in multiple campaigns,” said Flashpoint.
The hacker group not only hit Wipro, but the campaign also targeting similar companies, according to Kerbs the campaign targets Cognizant, Infosys, Rackspace, Capgemini, and Slalom detected similar patterns of phishing attack activity faced by Wipro.
Earlier this month Wipro Spokesperson said, “We came to know of a potentially abnormal activity from our network, which was related to very few employee accounts. These employee accounts were subjected to very advanced phishing activity.”
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity courses online to keep your self-updated.
Also Read:
Hackers Abuse GitHub Service to Host Variety of Phishing Kits to Steal Login Credentials
Wipro Security Breach – Employees’ accounts Hacked Through Advanced Phishing Campaign



.png
)
