A new sophisticated, unique Linux malware dubbed HiddenWasp used in targeted attacks against victim’s who are already under attack or gone through a heavy reconnaissance.
The malware is highly sophisticated and went undetected; the malware is still active and has a zero detection rate. The malware adopted a massive amount of codes from publically available malware such as Mirai and the Azazel rootkit.
Unlike Windows malware, Linux malware authors won’t concentrate much with evasion techniques, as the trend of using Anti-Virus solutions in Linux machine is very less when compared to other platforms.
However, the Intezer report shows “malware with strong evasion techniques does exist for the Linux platform. There is also a high ratio of publicly available open-source malware that utilizes strong evasion techniques and can be easily adapted by attackers.”
In the past, we saw many malware focussed on crypto-mining or DDoS activity, but the HiddenWasp is purely a targeted remote control attack.
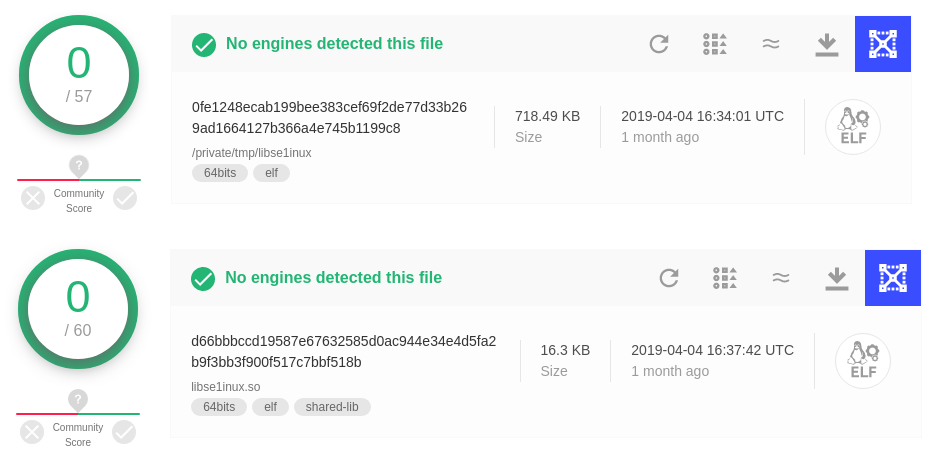
The malware is composed of a user-mode rootkit, a trojan, and an initial deployment script. Researchers spotted the files went undetected in VirusTotal and the malware hosted in servers of a hosting company ThinkDream located in Hong Kong.
While analyzing scripts, Intezer spotted a user named ‘sftp’ and hardcodes, which can be used for initial compromise and also the scripts has variable to clear the older versions from the compromised systems.
The scripts also include variables to determine server architecture of the compromised system and download components from the malicious server based on the compromised server architecture. Once the components installed, the trojan will get executed on the system.
“Within this script, we were able to observe that the main implants were downloaded in the form of tarballs. As previously mentioned, each tarball contains the main trojan, the rootkit, and a deployment script for x86 and x86_64 builds accordingly.”
According to the report, both the rootkits and the trojan help each other to maintain the persistence in the system “having the rootkit attempting to hide the trojan and the trojan enforcing the rootkit to remain operational.”

Researchers linked the malware with Chinese open-source rootkit for Linux known as Adore-ng, and this malware is aiming to intrude already compromised servers and the communication between the trojan and C&C server established over SNMP protocol.
Here is the list of trojan’s functionalities based on the requests. Enterprises can prevent Intrusion by blocking Command-and-Control IP addresses.

IOCs
IP
103.206.123[.]13
103.206.122[.]245
http://103.206.123[.]13:8080/system.tar.gz
http://103.206.123[.]13:8080/configUpdate.tar.gz
http://103.206.123[.]13:8080/configUpdate-32.tar.gz
SHA256
e9e2e84ed423bfc8e82eb434cede5c9568ab44e7af410a85e5d5eb24b1e622e3
f321685342fa373c33eb9479176a086a1c56c90a1826a0aef3450809ffc01e5d
d66bbbccd19587e67632585d0ac944e34e4d5fa2b9f3bb3f900f517c7bbf518b
0fe1248ecab199bee383cef69f2de77d33b269ad1664127b366a4e745b1199c8
2ea291aeb0905c31716fe5e39ff111724a3c461e3029830d2bfa77c1b3656fc0
d596acc70426a16760a2b2cc78ca2cc65c5a23bb79316627c0b2e16489bf86c0
609bbf4ccc2cb0fcbe0d5891eea7d97a05a0b29431c468bf3badd83fc4414578
8e3b92e49447a67ed32b3afadbc24c51975ff22acbd0cf8090b078c0a4a7b53d
f38ab11c28e944536e00ca14954df5f4d08c1222811fef49baded5009bbbc9a2
8914fd1cfade5059e626be90f18972ec963bbed75101c7fbf4a88a6da2bc671b
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity courses online to keep yourself updated.
Related Read
New Crypto Malware Spreading that Infects Linux Machines & Removes Anti-Virus
Cryptocurrency Mining Malware Targets Linux Machines Uses Rootkit to Hide From Monitoring Tools



.png
)
