Cybercriminals registered more than 100,000 look-alike domains that closely mimic the legitimate websites of popular retail websites.
As the growth of e-commerce increases year after year attackers tend to register more malicious look-alike domains that aimed to steal customer sensitive and financial data.
Most of the users believe everything with HTTPS is trusted and secure, but that is not the real scenario. HTTPS connection ensures only the data traveled between client and server is secure.
FBI recently warned that Hackers use Secure HTTPS Websites to Trick Users and to Steal Sensitive Logins.
Look-alike Domains
According to a recent investigation done by Venafi to find malicious domains targeting 20 retailers in the U.S., U.K., Germany, France, and Australia, they found over 100,000 fake domains that look like safe and trusted.
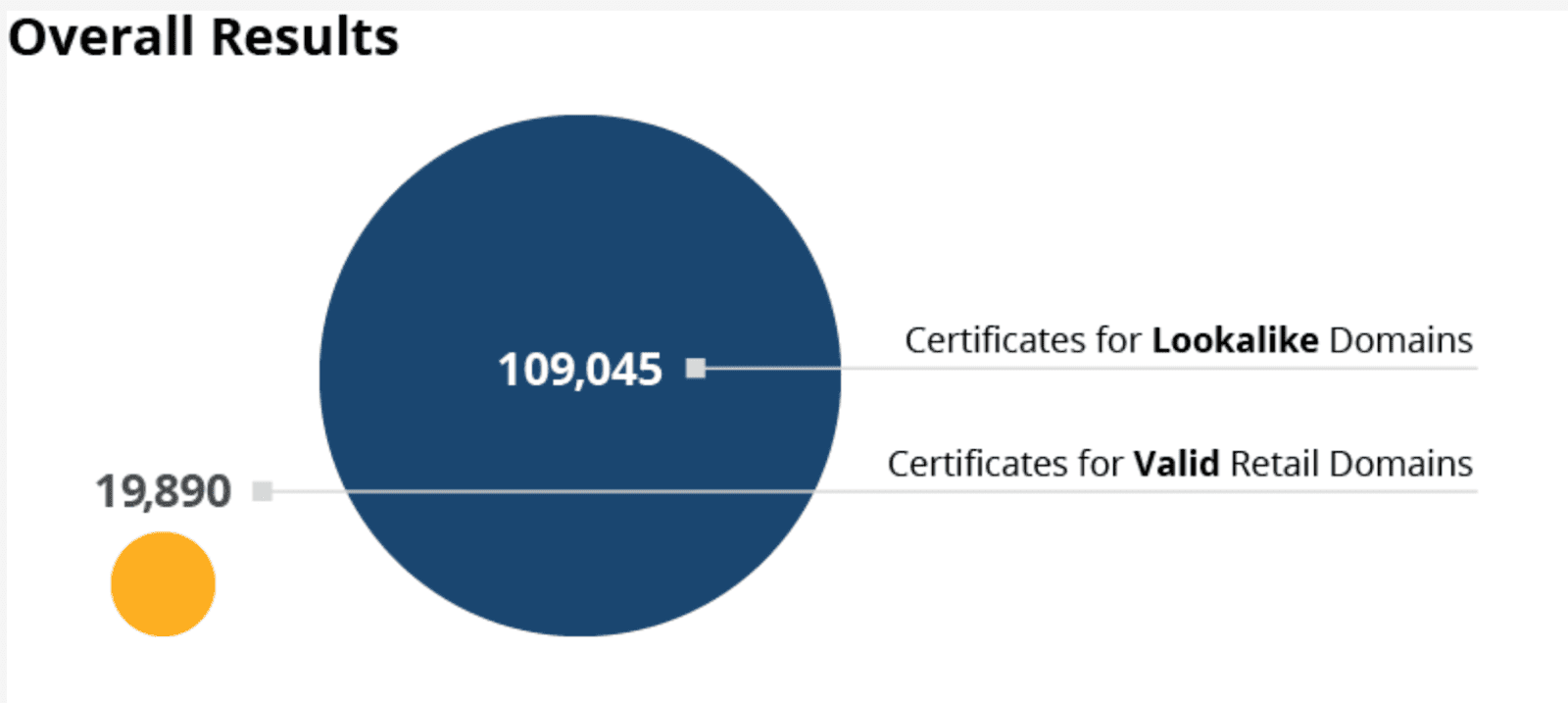
The research shows a sharp growth with the registration of fake domains, almost it doubled the growth when compared to 2018 and the TLS certificates used is 400% high, in that 60% of the domain using free SSL from Let’s Encrypt.
The registered fake domains vary between the country and the targeted retailer, among others, One of the top U.S. retailers has over 49,500 look-alike domains, United Kingdom (13,848), Germany (7,057), Australia (2,000), and France(1,569).
How Retailers can Mitigate
The Following are the two best prevention methods to avoid fake certificates.
- By using Certificate Transparency retailers can detect malicious certificates. The ultimate aim of Certificate Transparency is to reduce certificate-based threats.
- By adding CAA records retailers can specify which CA issue the TLS certificate.
For Customers
- Check the websites with online scanners to find it’s integrity.
- Check the Website Safety & Reputation
- Check the website spelling, logo and contact details.
You can find more details for checking with our article Is this website Safe: How to Check Website Safety to Avoid Cyber Threats Online.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
