Thousands of Facebook accounts have been stolen due to a trojanized version of the legitimate ChatGPT extension for Google Chrome. The trojanized version of the ChatGPT extension managed to gain popularity with more than 9,000 downloads.
Cybercriminals replicated the genuine “ChatGPT for Google” Chrome extension, providing seamless search results integration.

Besides the Facebook session cookies, the malicious version has additional code to steal them from Facebook.
This extension was published by the publisher on February 14, 2023, and made available to Chrome Web Store users. However, the publisher did not promote the title until March 14, 2023, when it used Google Search advertisements.
Malvertising on Facebook
The extension has been found to communicate with the same infrastructure as the main earlier version. An identical Chrome add-on was removed from the Chrome Web Store earlier this month after accumulating 4,000 installations.
The operators kept a backup of this new variant on the Chrome Web Store as part of the same campaign. In short, if the first one is reported and removed, this will be used as the backup proxy.
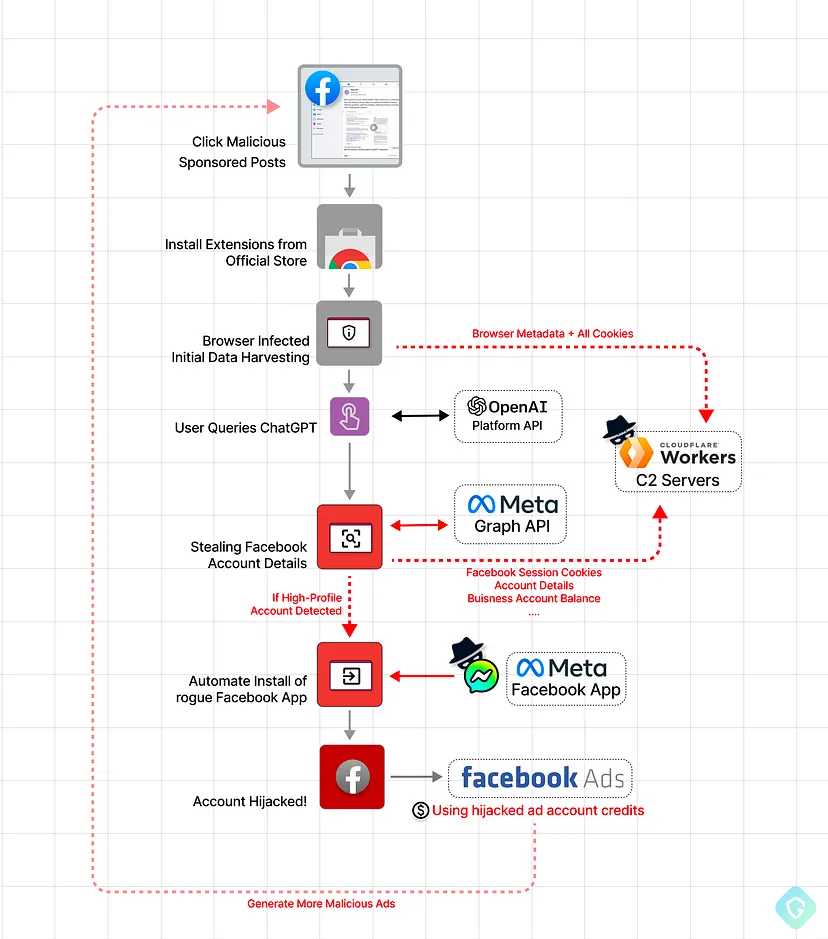
When you search for Chat GPT 4 in Google Search results, you will notice that several advertisements accompanying the malicious extension are prominently displayed in the search results. In short, threat actors actively promote the extension through Google Ads.

Users can access the official add-on store for Chrome by clicking on the sponsored search results, which are actually fake landing pages for “ChatGPT for Google.”
It is important to note that when the victim installs the extension, the victim will get the functionality they were promised since the code of the legitimate extension is still intact.
After gaining access to your pilfered data, the malicious actor will likely peddle it off to the highest bidder.
However, upon closer examination of their modus operandi, we have discovered that they exhibit greater attentiveness towards Facebook business accounts with a higher public profile.
A threat actor can use these stolen cookies to log into a Facebook account in the user’s name and gain complete access to the user’s profile and any advertising features for the business that may be available.
Here a list of Facebook-related cookies is obtained by the malware using a Chrome Extension API, and then they are encrypted using an AES key and sent to the malware through a secure channel.
After securing the stolen information, it will send it to the attacker’s server using a GET request.
Once the stolen cookies have been decrypted, the threat actors use them to hijack the Facebook sessions of their victims to run malvertising campaigns or to promote prohibited material, such as propaganda from ISIS.
To prevent victims from regaining control over their Facebook accounts, the malware automatically changes the login information on breached accounts so they can’t gain access to their accounts in the future.
Since its release, this extension has gained much popularity among users worldwide, with over 2000 installed daily.
This malicious extension for Google Chrome is still available in the Google Chrome Web Store and needs to be removed. In spite of this, the Chrome Web Store team was alerted to the malicious extension and is expected to be removed shortly.
Building Your Malware Defense Strategy – Download Free E-Book
Related Coverage:



.png
)
