Romanian police forces have arrested two individuals this week, for allegedly running two malware crypting services like CyberSeal and DataProtector to escape antivirus software detection.
These services were purchased by quite 1560 criminals and used for crypting several different types of malware, including Remote Access Trojans, Information stealers, and Ransomware.
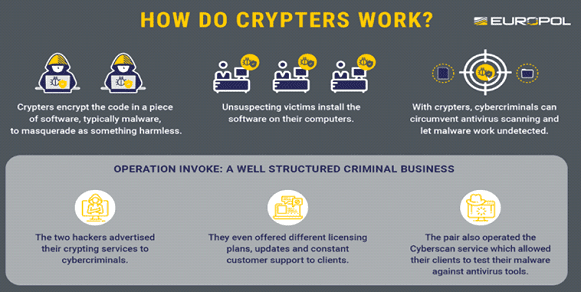
The pair used the Cyberscan service also which allowed their clients to test their malware against antivirus tools.
How do Criminals Bypass Antivirus Software?
Generally, hackers bypass antivirus detection through the utilization of crypters that encrypt or hide the primary code in a piece of software, usually malware to pretend to be something harmless until it gets installed on the victim’s device.
In this case, the services provided by these two suspects fall into a similar category and are offered for sale in the underground criminal market since 2010. Their clients paid between US$40 to US$300 for these crypting services, counting on license conditions. Their service activity was well structured and offered regular updates and customer support to the clients.
The criminals also offered a Counter Antivirus platform allowing criminals to test their malware samples against antivirus software until the malware becomes fully undetectable (FUD). The costs of this service varied between US$7 to US$40.
The Action took place against this Case
The agreed action, in this case, was led by Europol’s European Cybercrime (EC3) which smooth the progress of the exchange of data and provided forensic, malware, and operational analysis in grounding for the action.
European enforcement agencies and therefore the FBI collaborated to chase down the service operators. Therefore, the CyberSeal (cyber-seal.org) and Cyberscan (cyberscan.org) websites are now offline. These services were very well-networked on the dark web.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
Top 10 Best Free Antivirus Download For PC 2020
Mobile spyware that steal Twitter credentials uses sandbox to Evade antivirus detections



.png
)
