Security researchers spotted the first mass cyberattack campaign exploiting BlueKeep RDP Flaw to install a cryptocurrency miner on the vulnerable installations.
Bluekeep(CVE-2019-0708) is a wormable critical RCE vulnerability in Remote desktop services that let hackers access the vulnerable machine without authentication. As vulnerability is wormable, it could rapidly compromise millions of machines in a short period.
Microsoft and U.S. Government agencies warned users multiple times to patch their system. Microsoft said that “we are confident that an exploit exists for this vulnerability, and if recent reports are accurate, nearly one million computers connected directly to the internet are still vulnerable to CVE-2019-0708″.
The vulnerability exists with following Microsoft Windows Operating Systems, including both 32- and 64-bit versions.
- Windows 2000
- Windows Vista
- Windows XP
- Windows 7
- Windows Server 2003
- Windows Server 2003 R2
- Windows Server 2008
- Windows Server 2008 R2
On September Metasploit published a public exploit for BlueKeep, the exploit module targets 64-bit versions of Windows 7 and Windows 2008 R2.
The released exploit works on manual targeting, it only scans the machine to check it is vulnerable to BlueKeep or not.
Bluekeep Exploitation Spotted
Security researcher Kevin Beaumont spotted the RDP attacks, he stated that his Bluekeep RDP honeypots that expose only port 3389 going crash and rebooted.
“All have been up for 6 months without any crashes, but now all bar one keeps BSODing. They do have SCCM AV, Sysmon and Azure agents,” he added.
Kevin shared the honey port dumps with Marcus Hutchins’s popular security researcher also known as Marcus Hutchins, according to Marcus analysis hackers leveraging the Bluekeep vulnerability to install Monero Cryptocurrency miner.
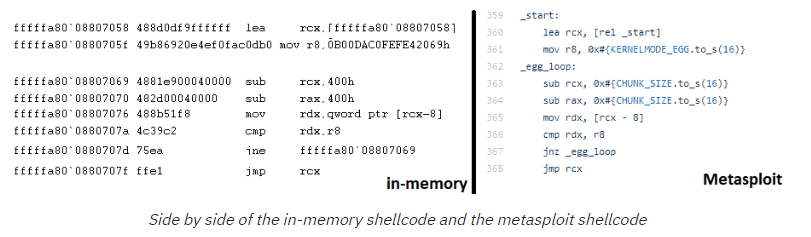
“Finally, we confirm this segment points to executable shellcode. At this point we can assert valid BlueKeep exploit attempts in the wild, with parts of the shellcode that even matches that of the shellcode in the BlueKeep Metasploit module!” reads the blog post.
The shellcode is an encoded PowerShell command, this PowerShell command downloads another encoded PowerShell command and another, which executes the actual binary.
The binary is the Monero cryptocurrency mining malware, known to Virus total. The malware used in exploiting BlueKeep RDP Flaw is not wormable, as researchers didn’t see any spike in scanning for vulnerable ports.
Mitigations
- Block Remote Desktop Services if they are not in use.
- Block TCP port 3389 at the Enterprise Perimeter Firewall.
- Apply the patch to the vulnerable Machines that have RDP Enabled



.png
)
