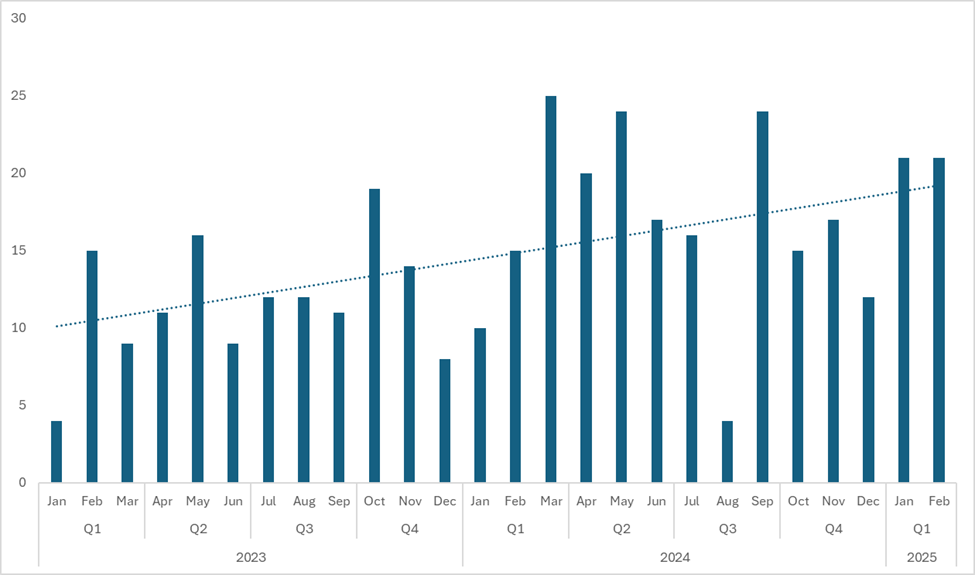
Medusa ransomware attacks have seen a significant increase, rising by 42% between 2023 and 2024, with a further escalation in early 2025.
This surge is attributed to the group Spearwing, which operates Medusa as a ransomware-as-a-service (RaaS) model.
Spearwing and its affiliates are known for conducting double extortion attacks, where they steal data before encrypting networks to pressure victims into paying ransoms.
If victims refuse, the stolen data is threatened to be published on their leak site.
Tactics and Techniques
Spearwing primarily gains access to victim networks by exploiting unpatched vulnerabilities, particularly in Microsoft Exchange Servers.
They also hijack legitimate accounts, possibly using initial access brokers.
Once inside, attackers use remote management tools like AnyDesk and SimpleHelp to further access and download drivers.
The Bring Your Own Vulnerable Driver (BYOVD) technique is frequently employed to disable security software by deploying signed vulnerable drivers.
Tools like KillAV and associated drivers are commonly used in this process.
PDQ Deploy is another hallmark of Medusa attacks, used to drop tools and move laterally across networks.
Other tools include Navicat for database queries, Rclone for data exfiltration, and NetScan for network discovery.
The consistency in tactics, techniques, and procedures (TTPs) suggests that Spearwing may not operate as a typical RaaS with multiple affiliates but instead provides a structured playbook for attacks.
Impact
Medusa ransomware attacks have targeted large organizations across various sectors, including healthcare and financial institutions.
Ransoms range from $100,000 to $15 million, with victims given a 10-day deadline to pay.
The ransomware adds a .medusa extension to encrypted files and drops a ransom note named !READ_ME_MEDUSA!!!.txt.
It can also delete itself post-execution, complicating investigations.
To mitigate these threats, organizations should ensure all software is up-to-date, monitor network activity closely, and implement robust security measures to prevent initial access.
Symantec provides protection updates and indicators of compromise to help detect and block malicious files associated with Medusa attacks.
Collect Threat Intelligence on the Latest Malware and Phishing Attacks with ANY.RUN TI Lookup -> Try for free



.png
)
