Security researchers from WizCase uncovered a massive data leak in the Microsoft Bing mobile app that exposes search queries, device details, and GPS coordinates.
Ata Hakcil uncovered the massive leak in the server owned by Microsoft for logging data related to its Bing mobile app.
Bing app used to perform millions of searches per day and it has more than 10,000,000 downloads on Google Play alone.
Microsoft Bing Server Data Leak
Hakcil confirmed his findings by running a search for “Wizcase” through a mobile app and while checking with the unprotected bing server “he found his information, including search queries, device details, and GPS coordinates, proving the exposed data comes directly from the Bing mobile app.”
The exposed server has records of search queries from more than 70 countries. The server believed to have exposed more than 6.5TB log files and the storage growing by 200GB per day.
According to the Wizcase scanner “server was password protected until the first week of September. Our team discovered the leak on September 12th, approximately two days after the authentication was removed.”
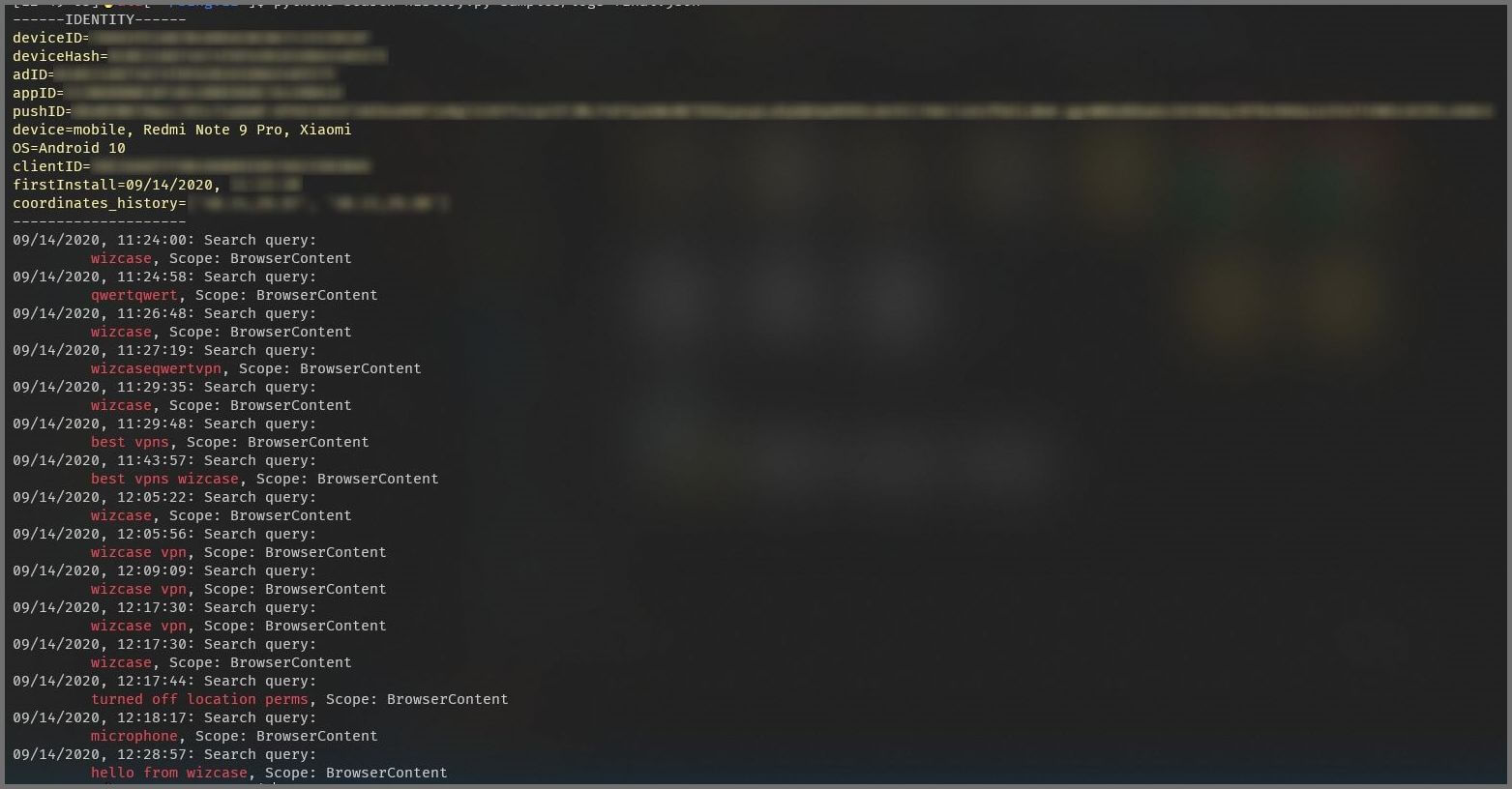
Users who used bing mobile app for searching in the meantime has been exposed is at risk. The following are the data exposed that includes;
- Search Terms in clear text excluding the ones entered in private mode
- Location Coordinates
- The exact time of the search
- Firebase Notification Tokens
- Coupon Data
- URLs clicked from search results
- Device model
- Operating System
- Unique ID(ADID, deviceID, devicehash)
The issue was reported to MSRC – Microsoft Security Response Center by September 13th and the server was secured on September 14.
In the meantime, researchers observed that Meow hackers attacked and deleted nearly the entire database. The second Meow attack on the server on September 14.
Meow hackers are known for destroying unsecured databases, they use some bots which overwrites all of the data, effectively destroying the contents of the database.
The data was exposed to all types of hackers and scammers, having the data attackers can launch a variety of attacks against users of the Bing mobile app.
If you are a bing mobile app user, pay a bit more attention to the when opening emails from unknown senders.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
Top 10 Best App Locks and Privacy Lock for Android Devices in 2020



.png
)
