A new and sophisticated phishing scam has been uncovered, leveraging Microsoft 365 domains to trick users into compromising their PayPal accounts.
The attack exploits legitimate-looking sender addresses and URLs, making it harder for victims to recognize the phishing attempt.
Security experts, including Chief Information Security Officers (CISOs), have raised alarms about the growing menace, urging caution and vigilance, shared by Fortinet.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free
How the Scam Works
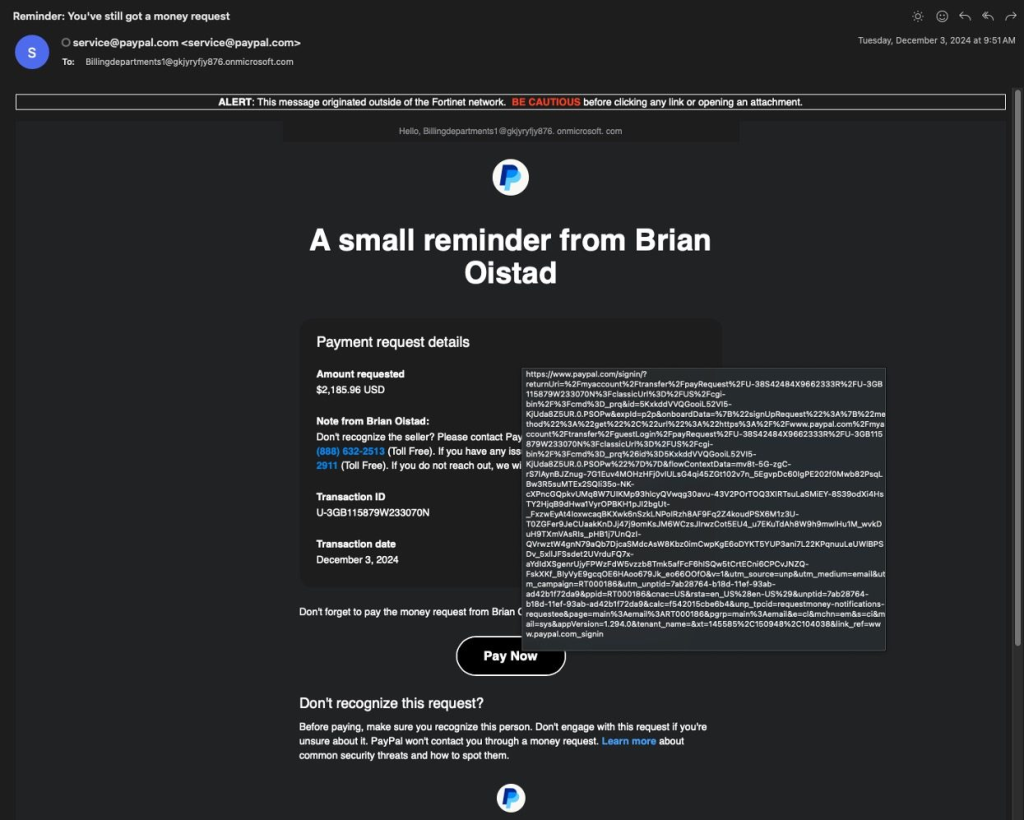
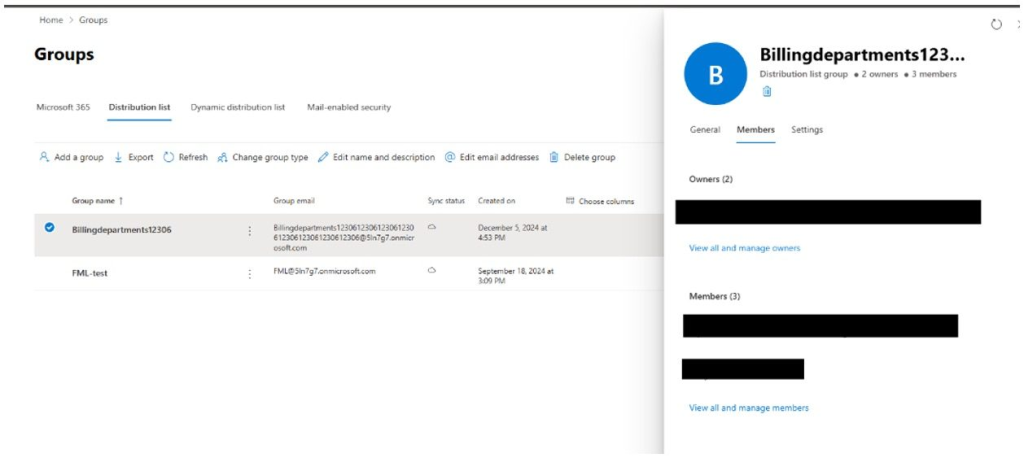
This phishing campaign uses Microsoft 365’s free trial domains to craft authentic-looking email addresses.
Once a scammer registers a trial domain, they set up deceptive distribution lists with obscure addresses resembling legitimate ones.
For example, an email might appear to originate from “Billingdepartments1[@]gkjyryfjy876.onmicrosoft.com,” which at first glance might look credible to unsuspecting users. Here’s the scam’s modus operandi step-by-step:
- The Money Request Email: The attacker uses the PayPal interface to send payment requests to the distribution list they created. This makes it appear PayPal itself is seeking money from the victims. The email is technically legitimate and passes sender authentication methods like SPF, DKIM, and DMARC checks, making it indistinguishable from real PayPal communications.
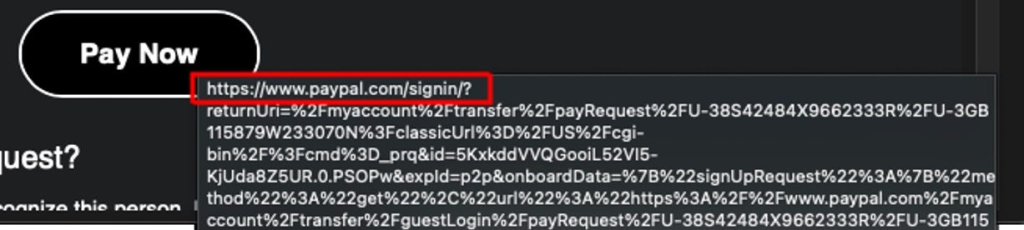
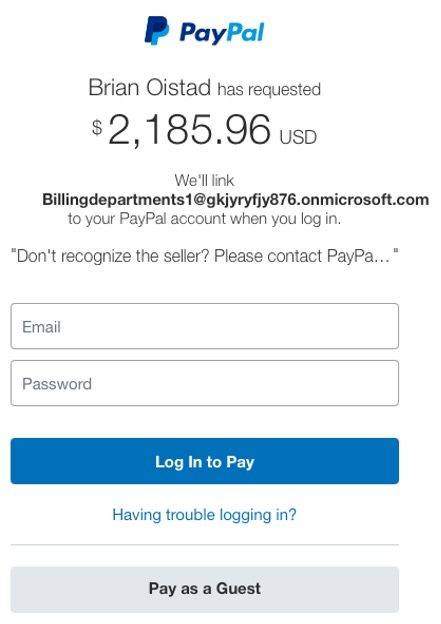
- The Phishing Hook: Upon receiving the email, victims who click the embedded link are directed to what looks like an official PayPal login page. The page displays the payment request, creating a sense of urgency and panic. Many victims proceed to log in without suspicion, thereby falling into the scammer’s trap.
- Account Takeover: Once the victim logs in, their PayPal account becomes linked to the scammer’s email address, such as “Billingdepartments1[@]gkjyryfjy876.onmicrosoft.com.” This allows the attacker to access the victim’s account, potentially transferring funds or stealing sensitive information.
Why This Scam is Dangerous
The cleverness of this attack lies in its leveraging of legitimate technologies. By using free Microsoft 365 test domains, the scammers bypass conventional detection systems.
The distribution list feature further obfuscates the true sender, creating plausible deniability. Even PayPal’s phishing detection instructions would fail to flag this method.
Most dangerously, the phishing email’s sender address and links appear authentic, and the email passes standard security checks. This raises the stakes, as even tech-savvy users might fall for the scam.
Experts urge vigilance when handling payment requests, even from seemingly legitimate sources. Here are some safety recommendations:
- Verify Requests: Always double-check payment requests directly within your PayPal account rather than relying on email links.
- Scrutinize Sender Addresses: Look carefully at the sender address for anomalies or inconsistencies.
- Enable Two-Factor Authentication (2FA): This adds an extra layer of protection to your PayPal account.

As attackers continue to innovate, staying informed and cautious is vital. PayPal users, especially those handling corporate accounts, must prioritize cybersecurity to avoid falling victim to threats like these.
Find this News Interesting! Follow us on Google News, LinkedIn, and X to Get Instant Updates!



.png
)
