Since the lockdown huge portion of employees working remotely through personal devices to access sensitive organization computers Windows’ Remote Desktop Protocol (RDP).
RDP is a proprietary protocol developed by Microsoft which helps a user to get another computer graphically over a network connection.
According to ESET telemetry reports, there is a huge uptick with several unique clients targeted via RDP brute‑force attacks.

These attack campaigns pose serious cases as some organizations neglect to implement protection settings and Employees use easy-to-guess passwords without any additional layer of protection.
In the current situation, most of the people started working remotely, so the RDP and the video communication platforms usage will be high.
RDP Attack Growing
Shodan already reported that “number of devices exposing RDP to the Internet has grown over the past month which makes sense given how many organizations are moving to remote work.”

Since the lockdown the remote traffic is increased, attackers taking advantage of the situation to steal the corporate resources.
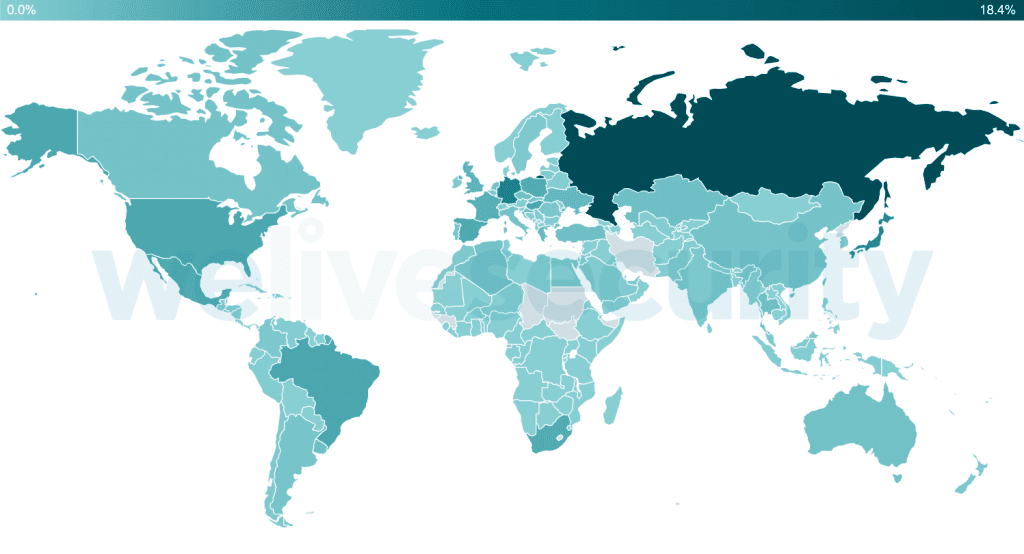
Here is the Countries with the most brute-force attacks reported by ESET telemetry.
In the case of RDP brute-force attacks, hackers use to scan the network using various tools to identify the IP address and the port ranges used by RDP servers.
Once RDP servers are tracked attackers use the various username and password combinations to gain access to the RDP servers.
If the attacker gains access to the RDP server they can sell the RDP credentials in dark web forums, disable antivirus software, install malware, steal company data, encrypt files, and much more.
Recently as well-know trojan TrickBot has included a new module for RDP that specifically built for brute-forcing RDP connections.
Mitigations
- Recommended to set strong RDP passwords
- Setup Network Level Authentication
- Two-factor Authentication
- If RDP not in use disable it
- Implement Account lockout policy
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



