A new Android bug dubbed StrandHogg 2.0 affects all devices running Android 9.0 and earlier. The bug lets malicious apps pose a legitimate app and steal victim data.
The bug was found by the Promon researchers tracked as (CVE-2020-0096) and it is similar to the original StrandHogg bug that was discovered as last year.
StrandHogg 2.0 The ‘evil twin’
StrandHogg 2.0 app enables attackers to hijack nearly any app and to exfiltrate sensitive user data, like contacts, photos, and track a victim’s real-time location.
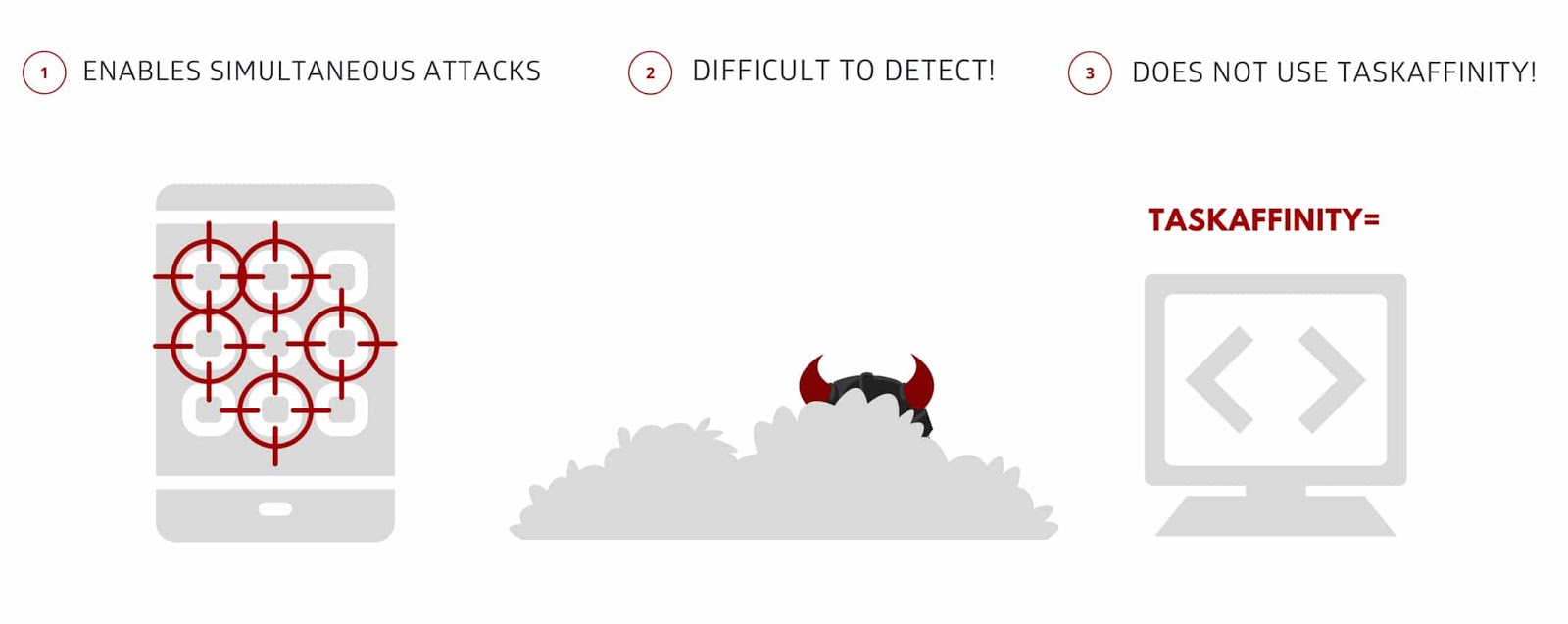
The Version 2.0 is different from original strandhogg, with the original version that attack is via Android control setting called ‘taskAffinity’ which allows any app – including malicious ones – to freely assume any identity in the multitasking system they desire.
The second version of the bug allows “executed through reflection, allowing malicious apps to freely assume the identity of legitimate apps while also remaining completely hidden.”
By using the StrandHogg 2.0, if a malicious app installed on the device it allows attackers to gain “access to private SMS messages and photos, steal victims’ login credentials, track GPS movements, make and/or record phone conversations, and spy through a phone’s camera and microphone.”

Tom Lysemose Hansen, CTO and founder of Promon said that “We see StrandHogg 2.0 as StrandHogg’s even more evil twin”.
The version 2.0 attackers nearly any app on a given device simultaneously at the touch of a button, and it is difficult to detect because of its code-based execution.
To exploit this vulnerability root access is not required, it enables sophisticated attacks, even on unrooted devices.
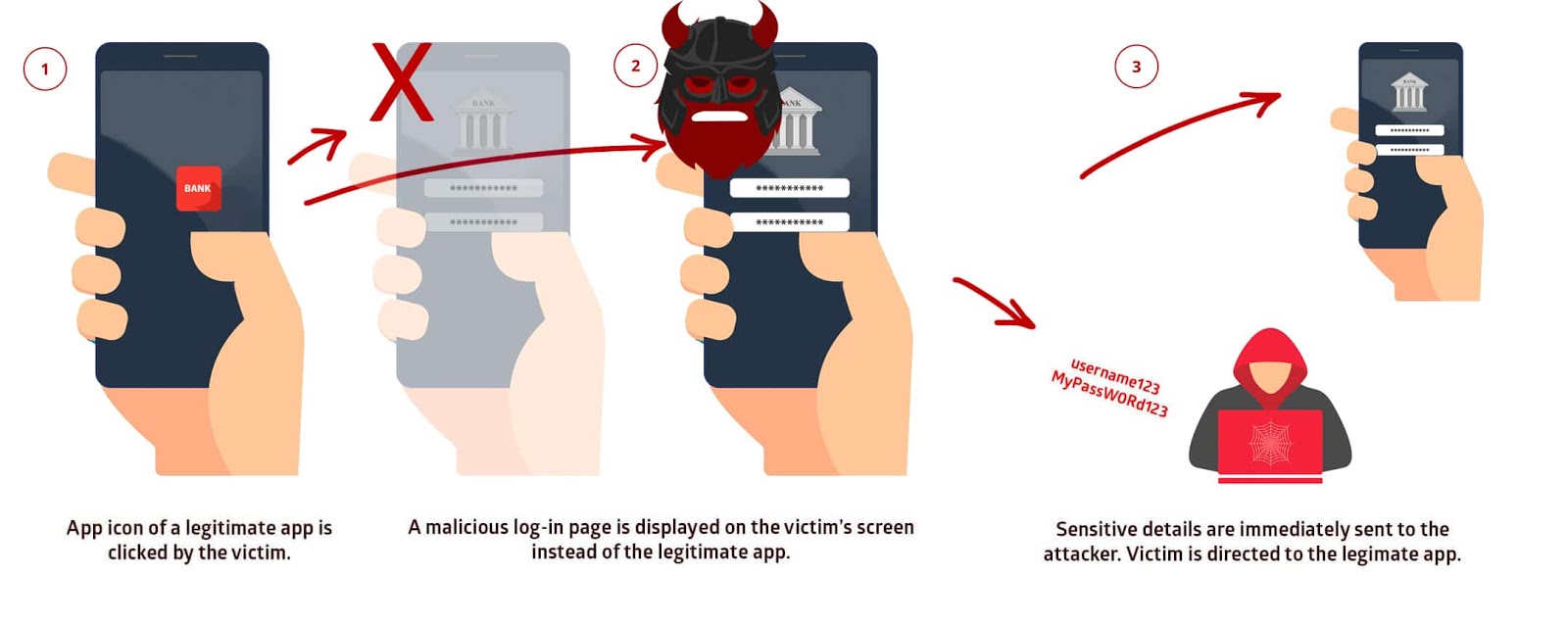
“By exploiting this vulnerability, a malicious app installed on a device can attack and trick the user so that when the app icon of a legitimate app is clicked, a malicious version is instead displayed on the user’s screen,” reads the research.
If victims input the login credentials and sensitive data with the malicious app, then the details are sent to the attackers’ server.
Malware that exploits StrandHogg 2.0 is a nightmare for the users because even anti-virus and security scanners unable to detect it.
“According to data from Google, as of April 2020, 91.8% of Android active users worldwide are on version 9.0 or earlier: Pie (2018), Oreo (2017), Nougat (2016), Marshmallow (2015), Lollipop (2014), KitKat (2013), Jellybean (2012) and Ice Cream Sandwich (2011).”
Android users need to update their devices with the latest version firmware as soon as possible to protect themselves from Strandhogg 2.0 attack.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
