A new malware dubbed SystemBC delivered by RIG and Fallout exploit kit, sets up a SOCKS5 proxy connection on victims machine to hide the Command and Control center traffic for popular banking malware such as Danabot.
In recent years most of the banking trojans are served through exploit kit, among them, RIG and Fallout are most Fallout and actively used by threat actors.
Proofpoint researchers observed the new proxy malware with multiple Fallout and RIG exploit campaigns that used to deliver Maze ransomware, Danabot banking, and Amadey Loader.

Malware Advertised in Hacking Forums
As the malware spotted in multiple campaigns, Proofpoint researchers checked with the underground marketplace for the existence of the malware. “we found an advertisement from April 2, 2019, on an underground forum that described a malware named “socks5 backconnect system” that matched the functionality of the malware seen in the above campaigns.”
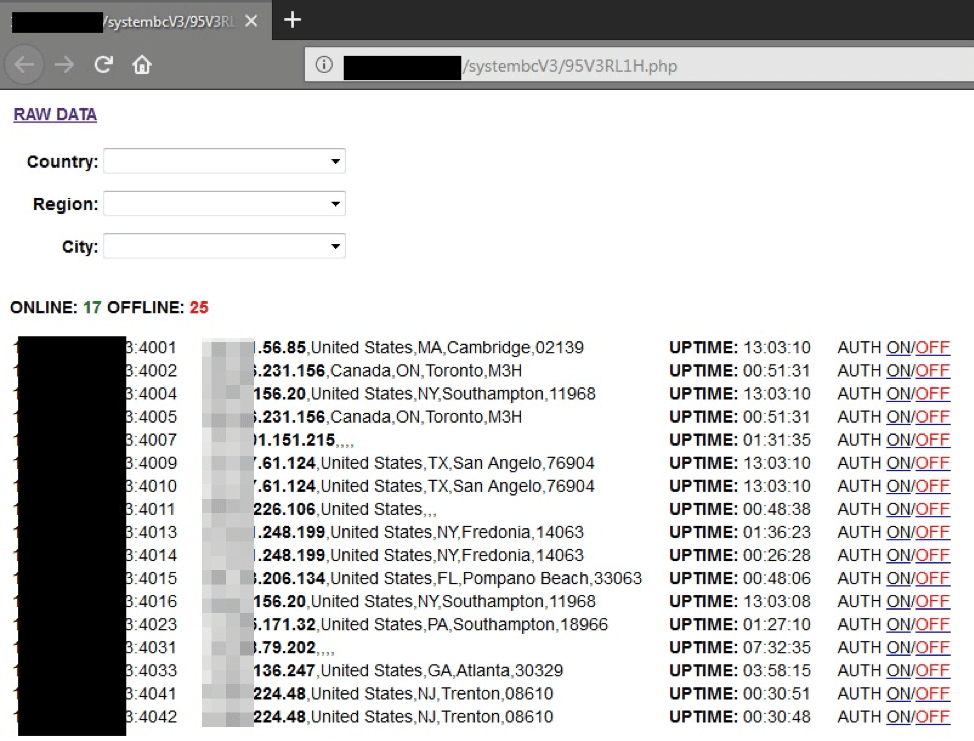
To differentiate from other malware using SOCKS5, the malware is named as SystemBC, the advertisement also details the C&C servers, list of victim machines and authentication.
The SystemBC malware written in C++ and it set’s up tunnel network in the infected machine to hide the traffic associated with other malware. The connection between the Command and Control are encrypted using RC4.
SystemBC Advertised as Below
• loader with update function every N hours (for long survivability it is necessary to update the crypts)
• firewall (access to socks only from trusted ip)
• authorization on socks by login and password
• GeoIP
Proofpoint published a detailed report, that covers the functionality and the detailed analysis report including the Indicators of Compromise.
Administrators are recommended to remain vigilant to keep the Windows client and server’s updated and the infrastructure devices patched and retire legacy systems.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity course online to keep yourself updated.



.png
)
