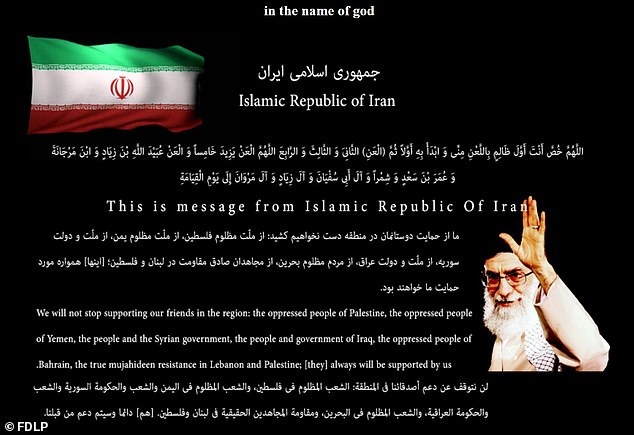
U.S government website agency website hacked by Iran cybersecurity group hackers and posted a revenge message for killing top military commander Qassem Suleimani.
The hacker’s group calming to represent the government of Iran and posted a picture with a warning message that refers to the death of Qassem Soleimani.
Fdlp.gov, the U.S government website run by the Federal Depository Library Program that provides government publications to the public for free of cost.
Once the Iran hackers defaced the website on Saturday, they left the following message ” in the name of god. >>>>> Hacked By Iran Cyber Security Group HackerS … ; This is only small part of Iran’s cyber ability ! We’re always ready.’ ”
Security Experts and U.S intelligence agencies have already warned that possibly cyber attacks could be targeting the U.S systems as a part of Iran’s retaliation for the U.S. airstrike.
During this cyberattack, we could see some of the non-Government websites also defaced by the same group of hackers, and the websites are owned by Sierra Leone Commercial Bank, the Taiwan Lung Meng Technology Company, and the Human Rights Protection Association of India.
Hackers posted a message on another page “Martyrdom was (Suleimani’s)… reward for years of implacable efforts,” read a graphic depicting US president Donald Trump being punched by a fist emanating from Iran as missiles fly by.
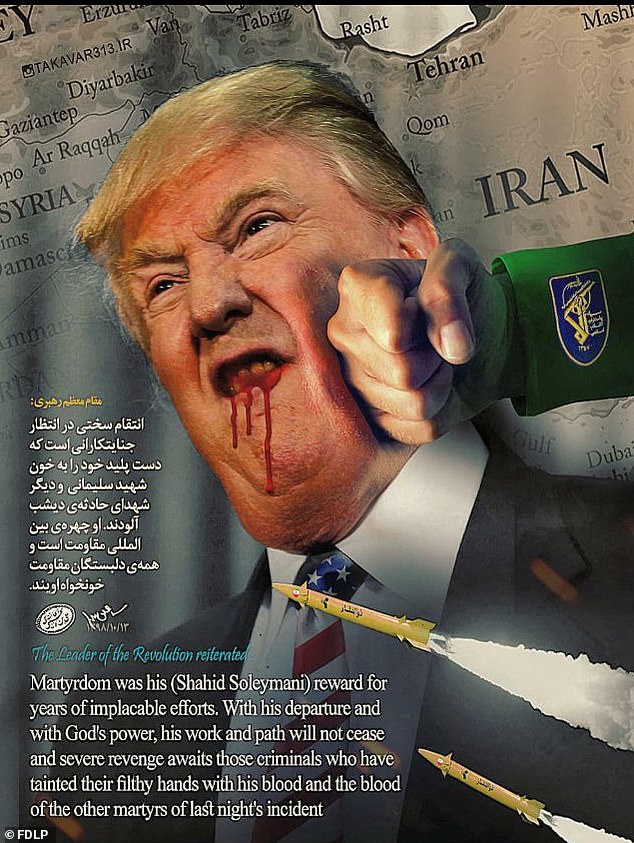
“With his departure and with God’s power, his work and path will not cease and severe revenge awaits those criminals who have tainted their filthy hands with his blood and blood of the other martyrs,”
The compromised Government website is still down at the time of writing.
GBHackers have reported various high profile cyber attackers associated with infamous Iranian hackers and they are involved in various cyberattacks that targeted the U.S public and private sectors.
Mid of the last year, U.S Launched cyber attack on Iranian Military Computers After U.S Military Drone Shot Down by Iran.
The attack was mainly targeting the Iran military computer systems with the approval of U.S president Trump and the cyber-attack disabled computer systems controlling rocket and missile launchers.
In the recent past, Iran based cyberespionage groups attempted to exploit various government, military networks, and other sectors including finance, oil, and gas by sending of spear-phishing emails. Multiple private U.S. cybersecurity firms reported it.



.png
)
