Ubuntu has announced its availability on Microsoft’s new tar-based Windows Subsystem for Linux (WSL) distribution architecture.
This enhancement simplifies deployment and improves scalability, making Ubuntu on WSL more accessible and optimized for enterprise environments.
Ubuntu has long been a popular choice among developers using WSL, thanks to its robust ecosystem and compatibility with development tools.
With this new distribution format, Ubuntu takes a significant step toward meeting the demands of businesses that require flexibility, enhanced control, and security in their IT infrastructure.
Key Features and Benefits
The new tar-based WSL distribution format introduces several advantages:
- Easier Deployment: Users can now install Ubuntu from a tar file, bypassing the need for Windows-specific packaging or the Microsoft Store. This is particularly useful for environments that restrict internet access or have strict software installation policies.
- Enterprise-Ready Solutions: Organizations can host and manage Ubuntu WSL images internally. This means IT teams can centrally control which images are distributed across the network, ensuring compliance with security and organizational policies.
- Customization and Automation: The tar-based format allows administrators to fully customize Ubuntu installations by modifying the image directly. Furthermore, Ubuntu’s native support for cloud-init enables advanced configuration and automatic setup during installation, simplifying large-scale deployments.
How to Get Started
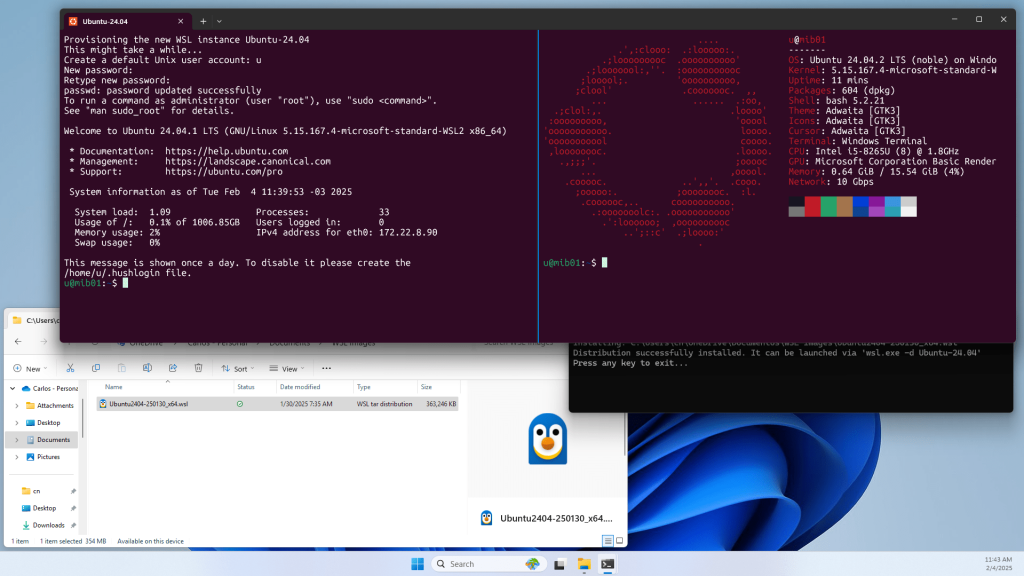
Users eager to try this new format can install Ubuntu on WSL by ensuring they have WSL version 2.4.8 or higher installed. From there, they can choose any of the following methods to install Ubuntu:
- Install Ubuntu directly from the web using the command:
wsl --install ubuntu- Alternatively, download the tar-based image and run:
wsl --install --from-file ubuntu.tar.wsl- For added convenience, users can also double-click the .wsl file to initiate installation.
Comprehensive documentation is available for those looking to explore advanced configurations or deploy custom Linux distributions, ensuring a seamless experience for all types of users.
This launch reflects Ubuntu’s commitment to innovation and usability on WSL, empowering developers and enterprises alike.
Whether you’re an individual developer looking for streamlined workflow integration or a business aiming to enhance IT operations, the new tar-based WSL format offers a game-changing solution.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free



.png
)
