TA397, also known as Bitter, targeted a Turkish defense organization with a spearphishing email containing a RAR archive, which included a decoy PDF, a malicious LNK file disguised as a PDF, and an ADS file with PowerShell code.
This technique, common for TA397, leverages NTFS ADS to establish persistence and deploy further malware like wmRAT and the newly identified MiyaRAT.
The attack takes advantage of a common theme of public investment projects, indicative of TA397’s targeted approach.
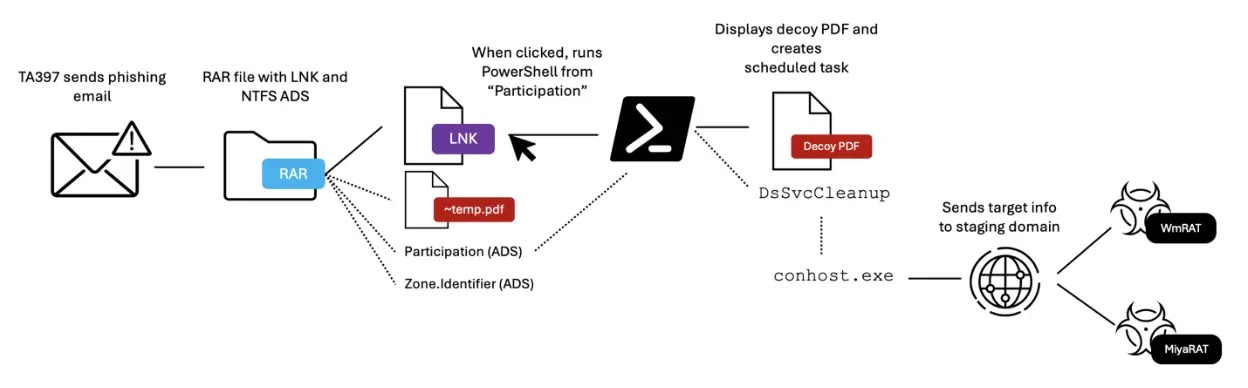
It leveraged a spearphishing email with a malicious RAR archive containing a decoy PDF and a malicious LNK file, which executed a PowerShell script hidden in the PDF’s ADS stream, establishing a persistent backdoor.
Free Webinar on Best Practices for API vulnerability & Penetration Testing: Free Registration
The backdoor sent system information to a C2 server, enabling TA397 to deploy additional payloads, which included WmRAT and MiyaRAT, remote access trojans that provided the attackers with extensive control over the compromised system.

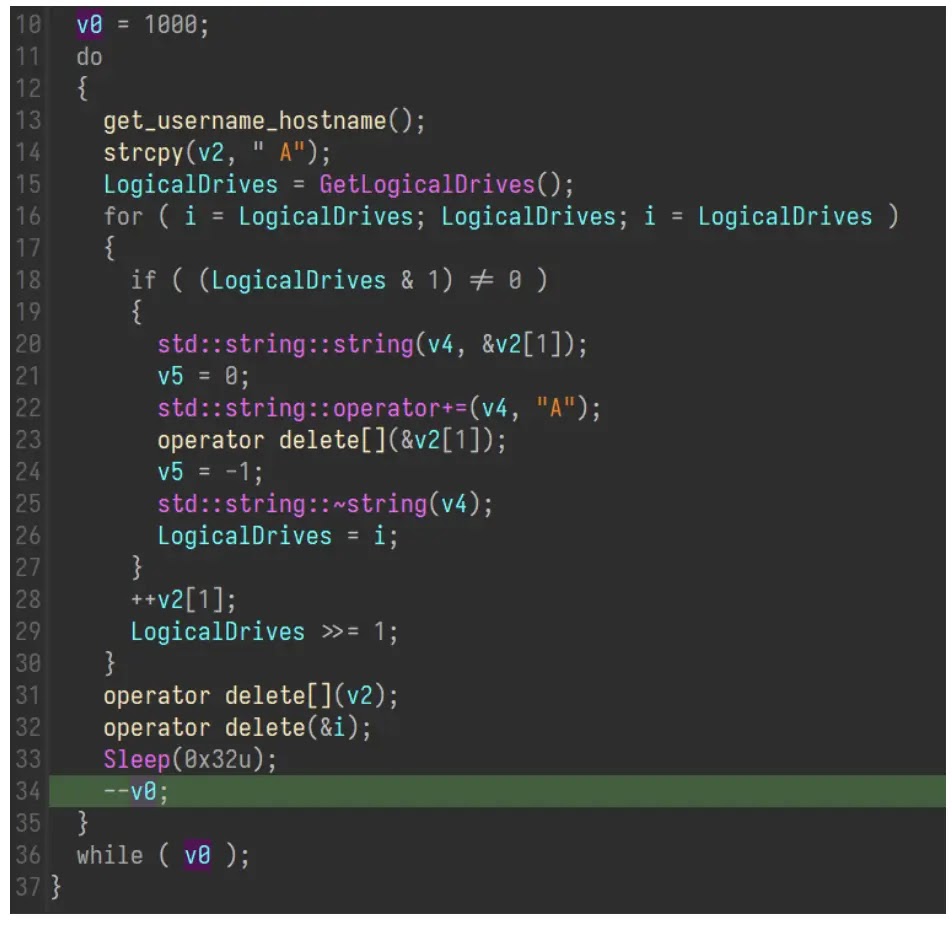
WmRAT is a C++-based remote access trojan (RAT) that leverages socket communication to execute various malicious operations and stealthily gathers system information, exfiltrates files, captures screenshots, and acquires geolocation data.
It can also enumerate directories and files and execute arbitrary commands through cmd or PowerShell and employs obfuscation techniques like junk threads and a simple decryption algorithm to hinder analysis.
By establishing a persistent connection with a hardcoded C2 server, it receives and executes commands, ultimately compromising the infected system.
MiyaRAT, a C++-based malware, begins by decrypting its hardcoded C2 server domain, “samsnewlooker[.]com,” using a simple substitution cipher and then establishes a socket connection to this C2 server on port 56189.
After initialization, MiyaRAT collects basic system information such as disk space, user information, OS version, and malware version, which is encrypted using a simple XOR cipher before being sent to the C2 server.
The C2 server is then able to issue commands to MiyaRAT, which may include the operation of files, the initiation of reverse shells, the capture of screenshots, and other commands.

According to ProofPoint, TA397 leveraged a multi-domain infrastructure to deploy WmRAT and MiyaRAT, where the staging domain jacknwoods[.]com, hosted on a multi-tenanted IP, distributed the malware.
Once deployed, the malware communicated with the C2 domains academymusica[.]com and samsnewlooker[.]com, likely attacker-controlled infrastructure, to receive further instructions, which setup aligns with previous TA397 campaigns, demonstrating their preference for multi-domain approaches to evade detection and maintain persistence.
The campaigns leverage RAR archives to deliver wmRAT and MiyaRAT payloads, indicative of their evolving tactics. The attacks target defense organizations in EMEA and APAC, particularly during UTC+5:30 working hours.
The use of scheduled tasks and similar infrastructure to past campaigns, along with the geographic and temporal patterns, strongly suggest a South Asian state actor is behind these operations, aiming to collect sensitive information for intelligence purposes.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free



.png
)
