The CVE-2024-49112 vulnerability in Windows LDAP allows remote code execution on unpatched Domain Controllers, as a zero-click exploit leverages this by crafting malicious LDAP requests, which, sent without any user interaction, exploit a memory corruption vulnerability within the LDAP service.
Upon receiving the malicious request, the vulnerable DC attempts to process it, leading to a memory crash and ultimately system instability, which can potentially be used to gain initial access to the domain, compromising critical systems and data.

Researchers identified a critical remote code execution vulnerability (CVE-2024-49112) in Windows LDAP services, which likely an integer overflow, resides within the wldap32.dll library, a core component of the LDAP client implementation.
By exploiting this flaw, unauthenticated attackers can remotely trigger a domain controller to perform a DNS lookup of a malicious domain and when processed by the vulnerable LDAP client code, this leads to a memory corruption, ultimately enabling arbitrary code execution within the context of the LDAP service running on the target domain controller.
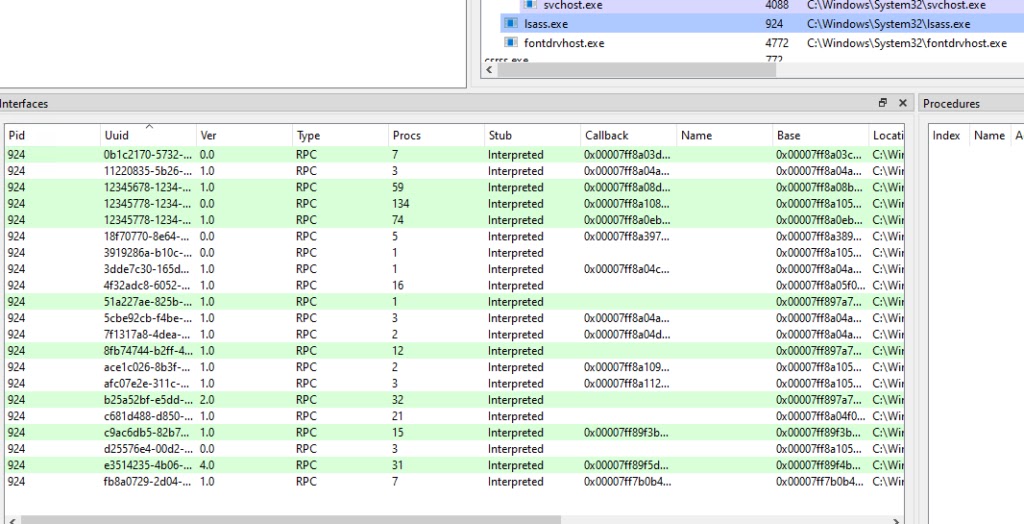
The attacker used the DsrGetDcNameEx2 function to trigger a remote LDAP request on the victim DC, as DsrGetDcNameEx2 is an RPC function that retrieves information about a domain controller in the specified domain and site.
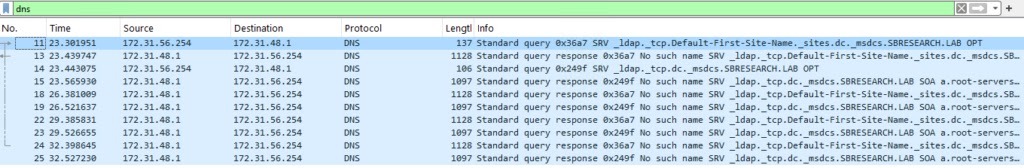
They set the DomainName parameter to be a domain that they controlled, and the victim DC sent a DNS query to its DNS server about a subdomain of that domain.
Then created SRV records for that subdomain that pointed to the attacker’s DC, and when the victim DC queried the DNS server again, it received the IP address of the attacker’s DC and sent an LDAP request to it.
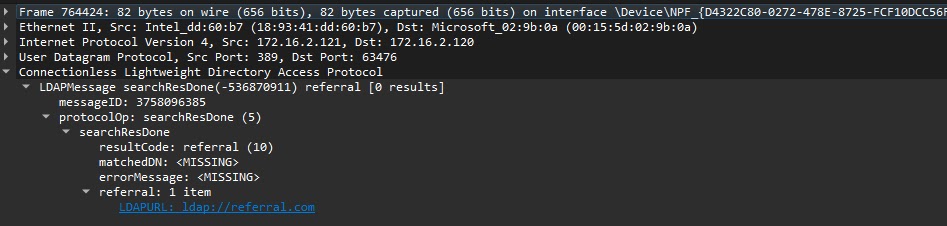
A malicious LDAP response packet was crafted by the attacker in order to take advantage of the LdapChaseReferral vulnerability.
By manipulating the length field of a specific value within the packet, they caused the “lm_referral” variable in the “ldap_message” struct to become non-zero, which triggered a vulnerability check within the LdapChaseReferral function.
Since the “referral table” pointer was null and “lm_referral” was non-zero, the function attempted to dereference a null pointer, leading to an access violation and potentially allowing remote code execution on the victim’s DC.
SafeBreach research into the LDAP CVE-2024-49112 vulnerability demonstrated successful exploitation beyond Domain Controllers, impacting any unpatched Windows Server.
By manipulating LDAP referrals with specific malicious values, researchers crafted an exploit chain that leverages DsrGetDcNameEx2 calls and DNS SRV queries to trigger memory corruption and potential remote code execution.
Proof-of-concept exploit and mitigation strategies, including patching and implementing detections for suspicious LDAP referrals and system calls, have been developed to assist organizations in addressing this critical vulnerability.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free



.png
)
