Cisco released an open-source hardware tool called “4CAN” for automobile security researchers and car manufacturers to find the potential security vulnerabilities in connected cars to ensure vehicle security.
Automobile systems such as cars integrated with hundreds of sensors and control systems that connected with computers and communicate with software systems in order to provide various features to the driver.
Vulnerabilities in these systems and the software that controls the car will cause serious threats in modern cars even it allows hackers to remote control of the vehicle.
New hardware security tool 4CAN let security researchers perform a variety of security assessments in components that connected with the vehicle such as Wi-Fi, Bluetooth, and cellular communication protocol, Controller Area Network (CAN)also called as CAN bus.”
If hackers physically access to the CAN bus via an ODB2 connector that fixed on the driver-side lower dash easily take complete control of the vehicle.
CAN bus communicate with various critical components including airbags and brakes and other non-critical components such as radio or interior lights.
By accessing the CAN bus, penetration testers and researchers can test the separate component to find the vulnerabilities.
4CAN
George Tarnovsky, a member of Cisco’s Customer Experience Assessment & Penetration Team (CX APT) designed the 4CAN with the various perspective of analysing the vulnerabilities and following goals.
1. Validating communication policy for intra-CAN bus communication.
2. Fuzzing (sending randomized payloads) to components to identify vulnerabilities.
3. Exploring the CAN commands used to control/interact with the vehicle.
4. Simplify our testbench set up to keep everything organized and in sync.
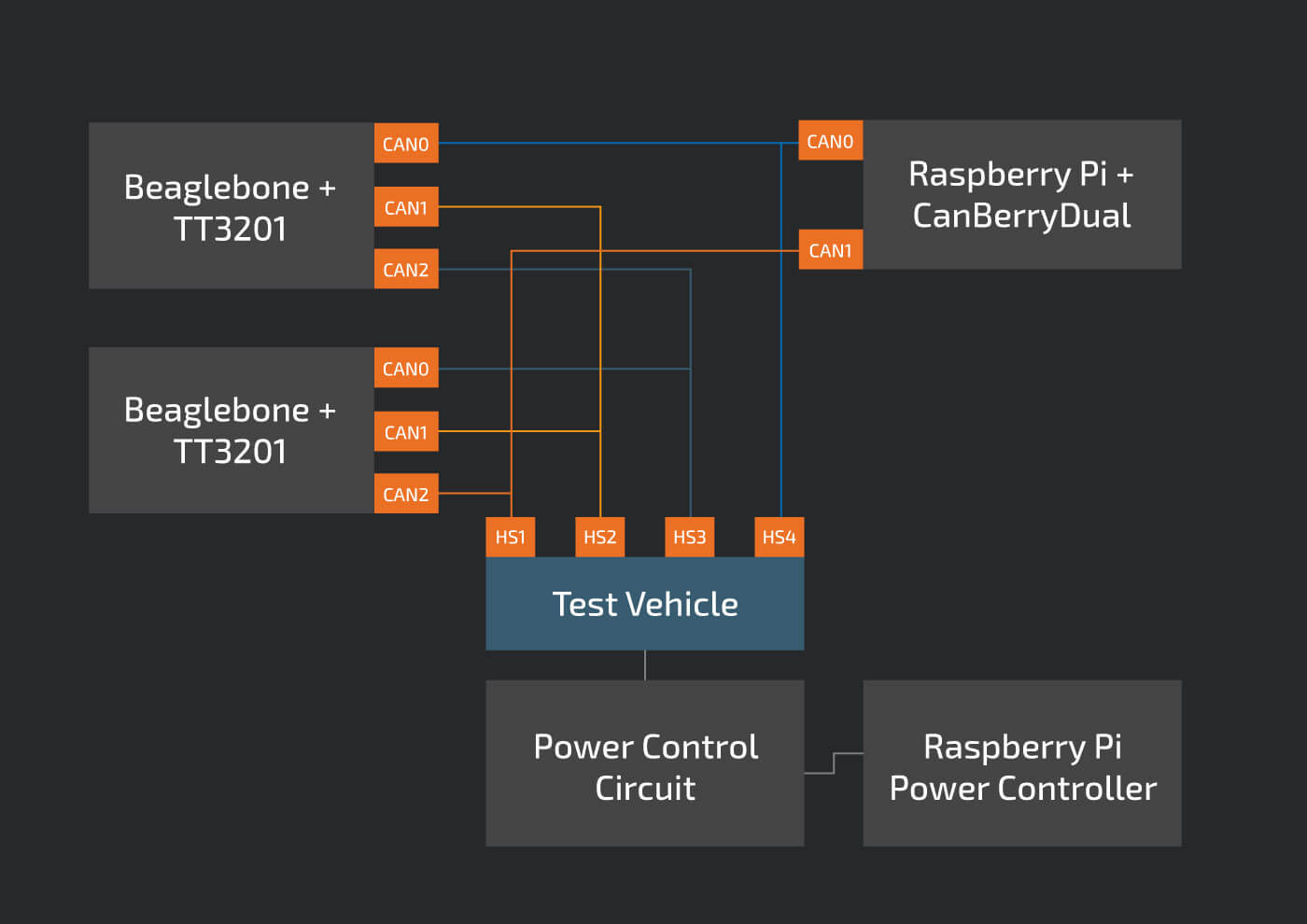
Before 4CAN arrives, There are three CAN devices required to simultaneously test four CAN buses.
“Along with that Two TT3201 three-channel CAN Capes attached to Beaglebones, and one CanBerryDual attached to a Raspberry Pi. also another Raspberry Pi to remotely control the test vehicle.”
With this configuration, we can test sending CAN frames between any two combinations of CAN channels but the testing process is very difficult which required to set up a lot of wires making the connection.
According to Cisco, “Using 4CAN, the test bench setup is vastly simplified. With a single Raspberry Pi, we can simultaneously test four CAN channel, and since the 4CAN exposes the entire 40-pin GPIO header, we can remotely control the test vehicle.”
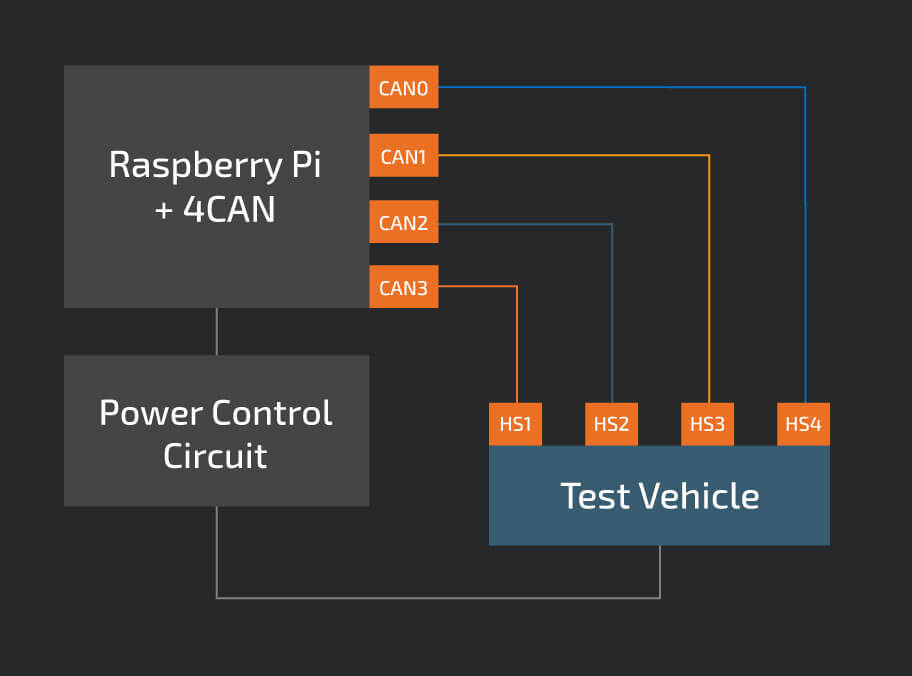
4CAN allow the researchers to test the vulnerabilities including sniff CAN traffic, send CAN messages, replay captured CAN traffic, implement a CAN gateway to facilitate CAN-in-the-middle and other tests.
You can down download the 4CAN from GitHub.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and Hacking New updates.



.png
)
