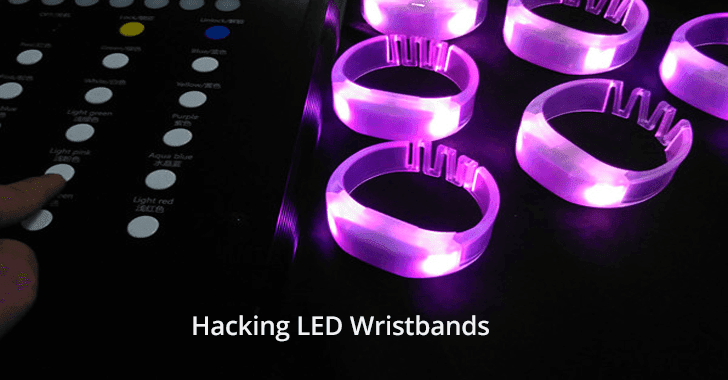
LED wristbands to light up large shows and events, it will be provided by event organizers to attendees, the wristbands are a part of lighting systems and it can be remotely controlled by DJ.
RF remote controllers are the common techniques used in these LED wristbands, security researchers from Trend Micro shows that these wristbands can be hacked and they able to reconstruct the packet structure.
LED wristband Security Analysis
Trend Micro researchers conducted an RF security analysis to determine the components used to light up the wristbands and they found a transmitter located in the DJ stage and wristband have interacted with it.
By opening one of the LED wristbands, they found a CC113L receiver made by Texas Instruments. It is a receiver only version of CC1101 transceiver.
To capture and analyze radio signals researchers used BladeRF SDR. a full bus-powered device that has a frequency range of 47 MHz to 6 GHz. It supports USB 3.0 SDR, useful to explore wireless communications.
“Multiple captures allowed us to compare different packets and reveal the overall packet structure. With the help of the DJ, we were able to capture different packets corresponding to different effects or commands,” researchers said.
Once the signals are captured they filtered and made some error correction’s to make it perfect and to obtain a packet structure.
Researchers used an open-source tool Sigrok to “interpret the signals captured with a logic analyzer and decode the SPI transactions.”
Sigrok gives a reconstruction of the register values and by SmartRF Studio RF parameters derived from the register values.
By the end researchers able to reconstruct 99% of the packet structure and right parameters to reconstruct the transmitter and now they could gain control over the LED wristbands and do whatever possible.
This case shows that commonly used RF technology and it’s wide attack surface.
Related Read
Radio Tech Used to Hack Everything From Airplanes to Defibrillators
A Critical Vulnerability in Tesla Model S Let Hackers Clone The Car Key Within 2 Seconds & Steal Car