Researchers found nearly 8 Million Android users infected with adware that hides in the phone and display ads as per the attacker’s command.
Researchers from ESET security identified dozens of apps with such behavior.
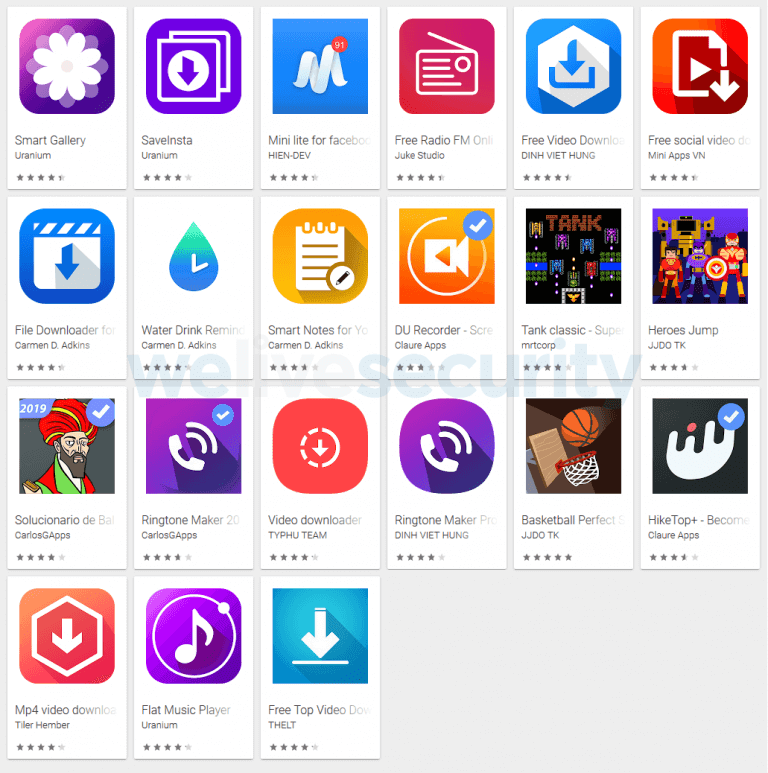
In total 43 apps observed on Google play with more than eight million installations, the campaign was tracked since July 2018. All the apps form the same Vietnamese developer.
Ashas Adware Functionality
Dubbed Ashas, the adware infected app offers the function they promise, on the other hand, it includes adware functionality and ability to steal data from the infected device.
The malicious applications contain components required to establish communication with the remote server. Once the app installed and launched it establishes communication with the C&C server.
The adware app sends the data of the infected device such as OS version, language, number of installed apps, free storage space, battery status and other details such as rooted/Developer mode and checks Facebook and FB Messenger.
Stefanko, a Security researcher from ESET observed the C&C server sending required configuration data for displaying ads and to stay stealthy and resilience.
Displaying ads – Three-Step Process
In the first step, the malicious app tries to check for the victim’s IP range, if the IP address within the range of Google servers then the app will not trigger the adware payload.
Next to the app setup the time interval between displaying tools and then based on the server response it hides the icon and creates a shortcut.
“Once the malicious app receives its configuration data, the affected device is ready to display ads as per the attacker’s choice; each ad is displayed as a full-screen activity,” reads ESET report.
App Developer Track Down
Stefanko tracked the malicious actor behind the apps by using openly available information, based on the domain used for the C&C server.
The malicious actor behind the campaign was a student at a Vietnamese university, the malicious actor also having apps in Apple’s App Store, a Youtube channel propagating the Ashas adware and a Facebook page.
According to ESET telemetry data, the following are the countries affected with Ashas adware.

This adware annoys users by displaying full-screen ads, drain batteries and also harvest information from the infected device. By automatically displaying the adware generate revenue to their operators.
You can find the complete details of IoC here.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



