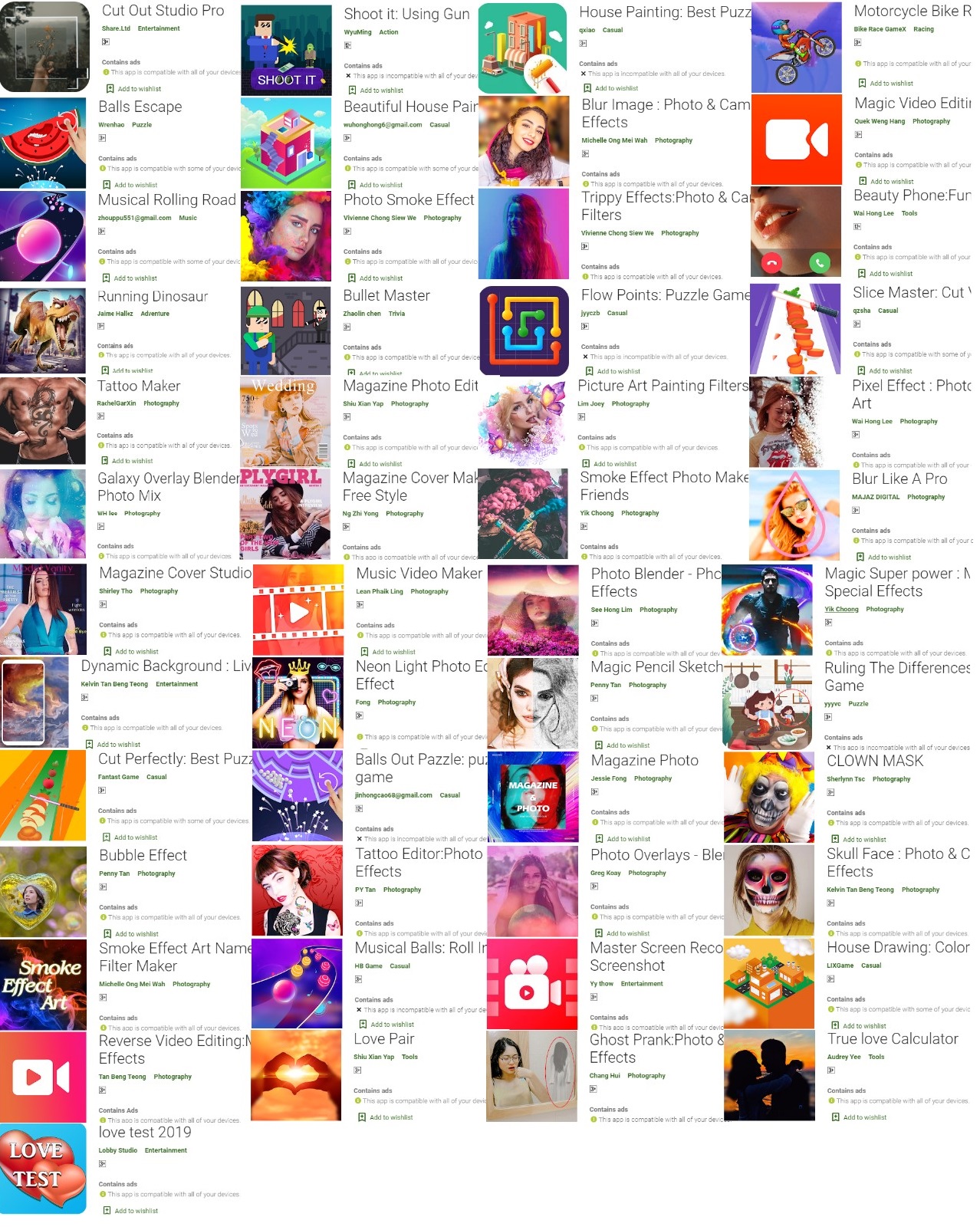
Researchers discovered nearly 49 malicious Android Adware Apps from Google play store related to games & stylized cameras, and these apps were downloaded by 3 million Android users around the globe.
Adware is a trending threat in 2019, especially targeting Android users, and it is a sweet spot for cybercriminals due to the over popularity of Android.
“GBHackers on Security” reported several adware incidents in the past few months, and it’s rapidly growing to exclusively target the Android users to generate millions of dollars revenue.
Android adware apps that discovered in this report have an ability to hiding themselves within mobile devices to display the ads, also deploying anti-uninstall, and evasion functions that’s a kind of sophisticated method compare to the traditional adware infection.
Very recently we have reported 85 fake photography and gaming adware apps that also employed unique techniques to evade detection.
Android Adware Apps Infection and Behavior
Apps that spotted in Google play that pushing adware is disguise their icons and push full-screen ads on the victim’s devices, and ads don’t allow users to exit, instead, victims need to click the HOME button to exit the ads page.
App developers are cleverly written code to hide the app icon malicious app’s icon, and also it used several evasion techniques to make sure it remains undetected.

Researchers from Trend Micro discovered the following technique used by these adware apps developers and published their apps in the Google Play store.
- Adware apps code is heavily obfuscated.
- Strings are not only encoded by base64 but also encrypted with custom algorithms with the package name as the key
- The adware shortcut is disguised as a popular default browser and uses the same icon, if users click on it then it opens an ad page and creating multiple shortcuts in the home screen.
- Adware action is differs based on the OS version from lower to higher.
- The adware is kept alive with the StartForgroundService function (deployed after Android OS 8.0). It registers itself as a foreground service, meaning it can run even if the user is not interacting with it.
Once anyone of the Android adware apps installed, it creates too many browser shortcuts, when users clicked on a fake chrome icon, a blank web page opens, and the page gets refreshed into a full-screen ad.
“After seeing the full-screen ad, the user may try to click ‘recent Screen’ button to check where it came from or close the ad. But there is no information displayed and no clue about where the ad came from”, Trend Micro said.

Code is written for these adware apps to provides a maximum show count and also sets an interval time to decide when the ad needs to appear on the victim’s device.
“All the malicious adware apps were taken down by Google, the total number of downloads was more than 3 million.” Trend Micro said.
You can also read the Top 5 Best Adware Removal Tool to Block Annoying Ads.



.png
)
