According to recent reports, Arabic-speaking Android users have been targeted with spyware by the “Arid Viper” threat actor, also known as APT-C-23, Desert Falcon, or TAG-63). This threat actor has been using counterfeit dating apps designed to exfiltrate data from compromised devices.
Arid Viper is a cyber espionage group that has been active since 2017. This threat actor has been speculated to be associated with Hamas, an Islamist militant movement. To compromise victims, Arid Viper uses malicious links masquerading as updates to dating applications that deliver malware to the user’s device.
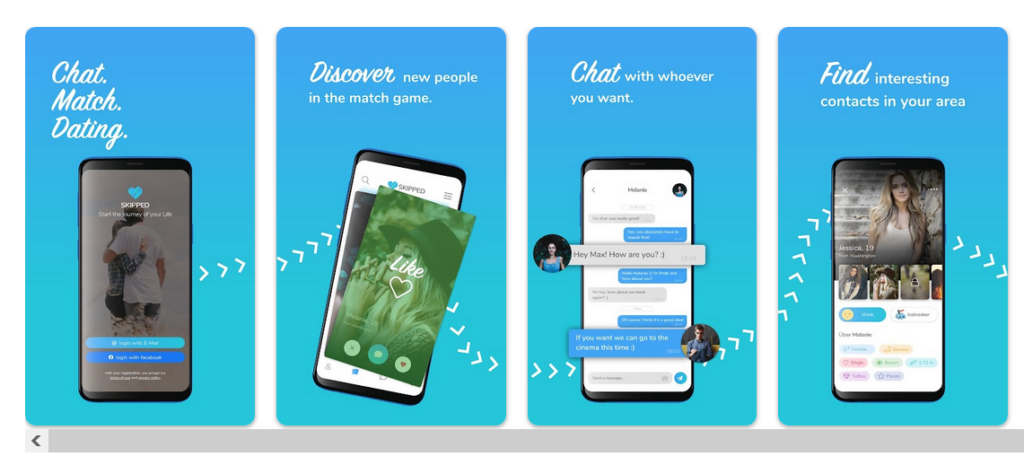
Malicious applications similar to Non-malicious application
The malware supplied by the threat group appears to have similarities with a legitimate online dating application called “Skipped” which creates suspicion as to whether the threat actors are linked with the application’s developers or acquired a copy of the application’s feature to spoof.
Webinar on Cyber Resilience for Financial Sector
Ensure your Cyber Resiliance with the recent wave of cyber-attacks targeting the financial services sector. Almost 60% respondents not confident to recover fully from a cyber attack.
However, there were also other applications detected that have similar themes like “Skipped” and are available in the Google Play Store and App Store.
The applications were VIVIO, Meeted, SKIPPED, and Joostly. Skipped and Joostly combined contain 60,000 downloads on the Google Play Store.
Once installed, this malware hides itself by turning off security notifications from any Android OS containing the “security” APK package.
It also requests for permissions like microphone, camera, contacts, call logs, SMS messages, Wi-Fi settings, background applications, Photos, and SYSTEM for malicious purposes.
Additionally, the malware is also capable of retrieving system information, updating the C & C domain from the current C2, and downloading additional malware that is hidden under legitimate app names like Facebook, Messenger, Instagram, and WhatsApp.
A complete report about this malware has been published by Cisco Talos, which provides detailed information about the malware, threat actor, and other additional information.
Indicators of Compromise
Cisco Talos has provided a GitHub repository containing IOCs related to this research.
- d5e59be8ad9418bebca786b3a0a681f7e97ea6374f379b0c4352fee1219b3c29
- 8667482470edd4f7d484857fea5b560abe62553f299f25bb652f4c6baf697964
- d69cf49f703409bc01ff188902d88858a6237a2b4b0124d553a9fc490e8df68a
- 1b6113f2faf070d078a643d77f09d4ca65410cf944a89530549fc1bebdb88c8c
- 57fb9daf70417c3cbe390ac44979437c33802a049f7ab2d0e9b69f53763028c5
- f91e88dadc38e48215c81200920f0ac517da068ef00a75b1b67e3a0cd27a6552
- a8ca778c5852ae05344ac60b01ad7f43bb21bd8aa709ea1bb03d23bde3146885
- fb9306f6a0cacce21afd67d0887d7254172f61c7390fc06612c2ca9b55d28f80
- 682b58cad9e815196b7d7ccf04ab7383a9bbf1f74e65679e6c708f2219b8692b
- e0e2a101ede6ccc266d2f7b7068b813d65afa4a3f65cb0c19eb73716f67983f7
- f15a22d2bdfa42d2297bd03c43413b36849f78b55360f2ad013493912b13378a
- ee7e5bd5254fff480f2b39bfc9dc17ccdad0b208ba59c010add52aee5187ed7f
- ee98fd4db0b153832b1d64d4fea1af86aff152758fe6b19d01438bc9940f2516
- 9a7b9edddc3cd450aadc7340454465bd02c8619dda25c1ce8df12a87073e4a1f
- 33ae5c96f8589cc8bcd2f5152ba360ca61f93ef406369966e69428989583a14e
Network IOCs
- luis-dubuque[.]in
- haroldramsey[.]icu
- danny-cartwright[.]firm[.]in
- conner-margie[.]com
- junius-cassin[.]com
- junius-cassin[.]com
- hxxps[://]orin-weimann[.]com/abc/Update%20Services[.]apk
- hxxps[://]jack-keys[.]site/download/okOqphD
- hxxps[://]elizabeth-steiner[.]tech/download/HwIFlqt
- hxxps[://]orin-weimann[.]com/abc/signal[.]apk
- hxxps[://]lightroom-61eb2[.]firebaseio[.]com/
- hxxps[://]skippedtestinapp[.]firebaseio[.]com/
Protect yourself from vulnerabilities using Patch Manager Plus to patch over 850 third-party applications quickly. Try a free trial to ensure 100% security.



.png
)
