Recent discoveries by Binary Security have revealed critical vulnerabilities in Azure API Management (APIM) that could allow attackers with minimal privileges to escalate their access and take full control over the APIM service.
These vulnerabilities were reported to Microsoft, leading to some fixes. However, certain issues remain unresolved, exposing many users unless they manually disable legacy API versions.
Vulnerabilities in Azure API Management
Azure API Management is Microsoft’s cloud-based offering for managing APIs at scale.
It provides features like API definition, security policies, and rate limiting essential for enterprise-grade API management.
Build an in-house SOC or outsource SOC-as-a-Service -> Calculate Costs
However, vulnerabilities in the older versions of its Azure Resource Manager (ARM) API have exposed a significant attack vector for privilege escalation.
The primary issue revolves around the use of older API versions. Despite Microsoft’s updates, old versions of the ARM API are still accessible and can be exploited by attackers.
These APIs allow users with Reader permissions—only meant to have read-only access—to perform actions reserved for administrators. These actions include:
- Deploying new APIs
- Modifying existing APIs
- Reading sensitive secrets and subscription keys
A notable vulnerability involves subscription keys, secrets used to grant access to APIs in APIM.
Attackers with Reader privileges can dump all subscription keys by manipulating API calls to older ARM API versions, bypassing restrictions Microsoft introduced in newer versions.
For example, an outdated API call like the one shown below can retrieve all subscription keys:
GET /Microsoft.ApiManagement/service/tmp-apim-sf/subscriptions?api-version=2014-02-14&$top=20 HTTP/1.1
Host: management.azure.com
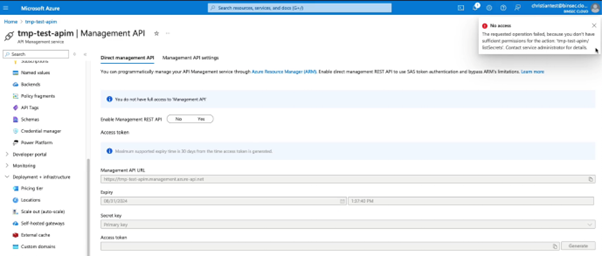
Authorization: Bearer eyJ…The most severe vulnerability allows attackers to escalate privileges from a Reader to a full Administrator role.
By exploiting legacy API endpoints, attackers can retrieve a Shared Access Signature (SAS) token, granting them administrative access to the APIM service.
Here’s an example of the API call that retrieves the SSO token, which can be exploited to gain full control:
GET /providers/Microsoft.ApiManagement/service/tmp-apim-sf/getssotoken?api-version=2016-07-07 HTTP/1.1
Host: management.azure.com
Authorization: Bearer eyJ…The returned token lets the attacker authenticate as an administrator, compromising the entire service.
Microsoft has introduced a toggle called “Disable old API versions” to reduce this risk. However, the toggle is not enabled by default, leaving many APIM services vulnerable.
Binary Security criticized Microsoft’s handling of the issue, pointing out that while some fixes were implemented, key vulnerabilities remain exploitable.
The company also noted that Microsoft’s communication regarding these vulnerabilities was lacking.
While Microsoft has addressed some vulnerabilities in Azure API Management, the remaining issues highlight the importance of staying vigilant and applying best practices for cloud security.
Enterprises using APIM should ensure legacy APIs are disabled and take proactive steps to secure their API environments against privilege escalation attacks.
Run private, Real-time Malware Analysis in both Windows & Linux VMs. Get a 14-day free trial with ANY.RUN!



.png
)
