Recent research has linked a series of cyberattacks to The Mask group, as one notable attack targeted a Latin American organization in 2022, where attackers compromised the organization’s MDaemon email server and exploited the WorldClient webmail component to maintain persistent access.
While the initial compromise vector remains unknown, the successful exploitation of the MDaemon server highlights the potential risks associated with outdated or misconfigured email systems.
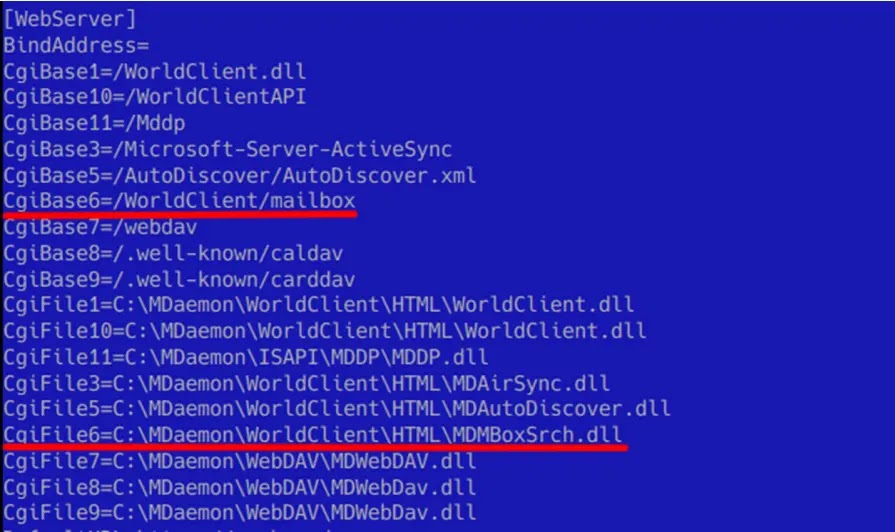
The threat actor exploited a vulnerability in MDaemon WorldClient’s extension loading mechanism. By leveraging the WorldClient.ini configuration file, they were able to introduce malicious extensions.
These extensions, designed to intercept and manipulate HTTP requests, provided a persistent backdoor into the email server, which allowed the attacker to maintain unauthorized access and potentially execute further malicious activities.
Free Webinar on Best Practices for API vulnerability & Penetration Testing: Free Registration
The threat actor exploited WorldClient’s extension feature by crafting a malicious extension DLL and configuring it with malicious URLs in the CgiBase6 and CgiFile6 parameters.
It allowed the actor to remotely interact with the malicious extension via HTTP requests to the specified URL on the webmail server, bypassing security measures and potentially gaining unauthorized access to sensitive information.

Attackers leveraged a malicious eThe extension to infiltrate a Latin American organization in 2022, which executed commands to gather system information and laterally move within the network.
By employing legitimate software like HitmanPro Alert’s driver and malicious DLLs, .bat files, and XML files for scheduled tasks, they propagate the infection, compromising multiple systems within the organization.
They exploited a vulnerability in the Tpm-HASCertRetr.xml description file to schedule tasks that executed commands from the ~dfae01202c5f0dba42.cmd file, which installed the hmpalert.sys driver, which, due to a lack of verification, could load malicious DLLs.
By placing their payload DLLs at C:\Windows\System32\hmpalert.dll, the attackers were able to inject these DLLs into privileged processes like winlogon.exe and dwm.exe on system startup, gaining persistent and elevated access to the compromised systems.
In early 2024, adversaries exploited a vulnerability in the hmpalert.sys driver to infect a system. Unlike previous attacks, they bypassed scheduled tasks, employing a novel technique involving Google Updater.
The malicious hmpalert.dll payload, identified as FakeHMP, enabled attackers to steal files, log keystrokes, capture screenshots, and deploy additional malware, where threat actors further compromised systems with a microphone recorder and file stealer.
The organization was compromised by an advanced attack leveraging two malicious frameworks, Careto2 and Goreto, where Careto2, installed via a multi-stage process, used COM hijacking for persistence and a virtual filesystem to store plugins for various malicious activities.
While Goreto, a Golang-based toolset, connected to Google Drive for command-and-control, executing commands, keylogging, and capturing screenshots. Both frameworks employed advanced techniques, indicating a sophisticated and persistent threat actor, likely the Mask.
According to Secure List, the threat actor known as Careto remains a formidable force in the cyber threat landscape.
Despite a decade-long absence, the group continues to innovate, employing advanced techniques like persistence through MDaemon and implant loading via HitmanPro Alert.
Their ability to craft intricate, multi-component malware underscores their technical prowess. While the timing of their next campaign is uncertain, it is anticipated to be equally sophisticated and disruptive.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free



