Advanced persistent threat (APT) campaign aims to steal sensitive information form corporations doing business in China.
The malware GoldenSpy was observed by Trustwave SpiderLabs in a threat-hunting operation on behalf of it’s the UK Technology-based client.
GoldenSpy Malware Hidden in Tax software
Trustwave observed that since April 2020, the GoldenSpy backdoor found to be embedded in the Aisino Intelligent Tax software suite.
The tax software suite is mandatory for a corporation operating in China to conduct business, this software suite that would enable payment of local taxes.
The “Intelligent Tax” software as expected handel tax operations, but in the background, after 2 hours it downloads and executes a file called svminstaller.exe, which downloads the other two executables called svm.exe and svmm.exe.

The file was downloaded from the URL download.ningzhidata[.]com, Svm.exe(GoldenSpy) is responsible for gathering information and sends data to www.ningzhidata[.]com via port 9006.
Both the files svm and svmm are installed as autostart services nad they operate with System-level privileges if the process killed it will get restarts automatically.
“At this point, we are unable to determine how widespread this software is. We currently know of one targeted technology/software vendor and a highly similar incident occurring at a major financial institution, but this could be leveraged against countless companies operating and paying taxes in China or may be targeted at only a select few organizations with access to vital information,” reads the report.
Corporations that have installed the tax software are at high risk, by having a backdoor into their network attackers can compromise the networks, leads to breach and loss of sensitive information.
Network Communications
GoldenSpy (svm.exe) communicates with ningzhidata[.]com for sending data and to receive commands, researchers observed that “domain and its subdomains have resolved to a number of IP addresses, however, based on their certificates, most are a part of the qcloud CDN and appear to only host download.”
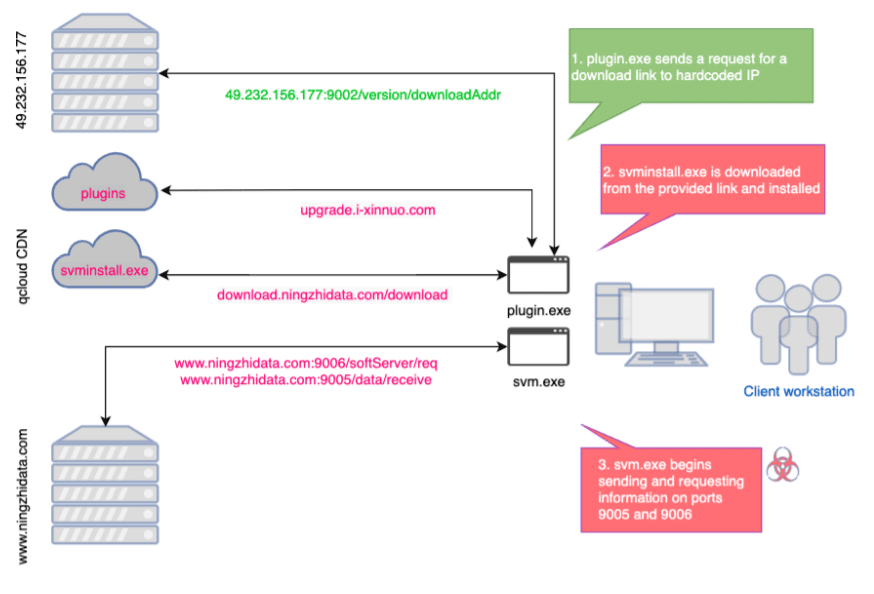
Following are the ports used in communication
- Ports 9005, 9006: Ports used for svm.exe network traffic.
- Port 9002: Used by updater service to request a link to download svm.exe.
- Port 8090: While we didn’t observe this directly in our analysis, there are indicators on public scan sites that svm is downloaded over this port in some circumstances.
- Port 33666: WebSocket established by Golden Tax software on installation
Trustwave SpiderLabs published a complete report along with IOC’s, organizations operating with China are recommended to investigate the network connections.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read
How to Detect Obfuscated Malware on Your Server
Certified Malware Analyst – Exploit Development, Expert Malware Analysis & Reverse Engineering



.png
)
