A new botnet dubbed GoldBrute attacks more than 1.5 million RDP servers that are exposed to the Internet. The botnet scans for random IP addresses to detect windows machines with RDP exposed.
Like other botnets GoldBrute is not using weak passwords or reusing the passwords form data breaches, instead, it uses its own list of usernames and passwords to launch brute force attacks.
Security researchers from Morphus labs detected the ongoing malicious campaign which is controlled from a single C&C server and the communication exchanges between the bots are encrypted with the symmetric algorithm AES through port 8333.
GoldBrute Botnet Attack
The bot starts by scanning the Internet to find Windows hosts with Remote desktop protocol services exposed. Once it finds a host, it reports to C&C server, if the bot reported 80 victims then C&C server will assign a set a target to launch brute force attack.
It is worth noting that each bot will try only one username and password against the target to avoid detections. “This is possibly a strategy to fly under the radar of security tools as each authentication attempt comes from different addresses,” reads the blog post.
Once the attack successful, it downloads the zip archive which is GoldBrute Java code on targeted RDP server along with the Java runtime. It uncompresses and then runs a jar file called “bitcoin.dll.”
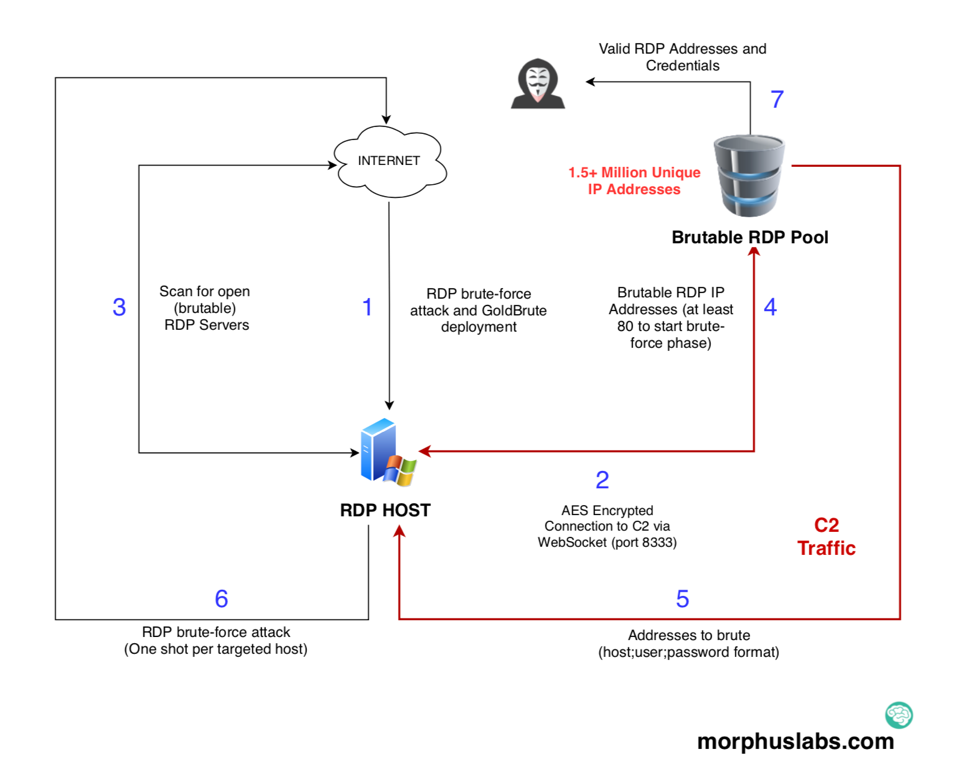
Then the new bot starts scanning the Internet for open RDP servers. If it finds any new IP, then it reports to the C&C server.
Once it reaches 80 brutable RDP servers, then C&C server will assign a set of targets to the new bot.
In the brute-force phase, the bot will continuously get username & password combinations from the C&C server.
Researchers tested the bot under lab environments, “after 6 hours; we received 2.1 million IP addresses from the C2 server from which 1,596,571 are unique. Of course, we didn’t execute the brute-force phase.”
The heatmap reveals that GoldBrute targets exposed RDP machines around the globe.

Make sure that you have patched for Bluekeep RCE vulnerability, now it’s time to prepare against GoldBrute as the bot continues to scan and grow.
Indicators of Compromise
Files(SHA256)
af07d75d81c36d8e1ef2e1373b3a975b9791f0cca231b623de0b2acd869f264e (bitcoin.dll)
Network
104[.]248[.]167[.]144 (Zip download)
104[.]156[.]249[.]231:8333 (C2 server)
Other Botnet Attacks
Hacker Compromised Several IoT Botnet C2 Servers and Taken Control of It Due to Weak Credentials
Newly Emerging DDoS Botnet Attack on Electrum Takes 152,000 Hosts Under its Control
Hackers Offered IoT Botnet as Service “TheMoon” : Botnet-as-a-Service



.png
)
