A new report shows that 61% of malicious ads on the Internet targeting Windows computers to infect with malware or to steal the information.
The malicious ads act as a platform to distribute malware, by attracting users and redirect them to malicious websites which results in downloading the malware.
Windows as Prime Target
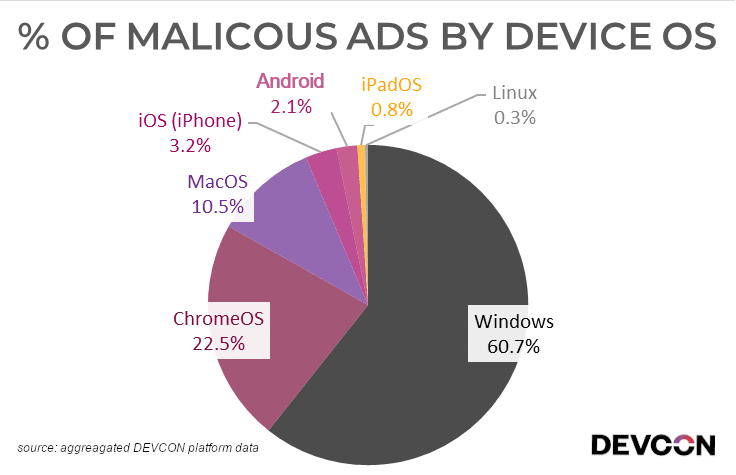
According to Devcon observation between July 11 – November 22, 2019, 61% of the malicious ad campaigns primarily targeting the Windows operating system, when compared to other popular operating systems.
Next to the Windows operating system, the second most targeted operating system in ChromeOS which accounts for 22.5%, next is MacOS at 10.5% and the least targeted device is Apple iPads at 0.8%.
In another report published by Confiant, the malicious ads increased from Q2 to Q3. The Q3 attacks are targeting desktop computers, mainly running Windows and they are attacking users mainly in Italy, Spain, and Scandinavia.
The Windows operating is the most used one, it’s popularity let malware authors invest more time and resource to develop a more sophisticated malware. Wannacry is an example of it.
We can’t assume Linux OS is the most secured one, nowadays attackers targeting Linux servers also to install various malware, most particularly coin miner scripts.
With Q3 three different variations of ads observed
Malicious ad – Ads with Javascript that force redirection to another website.
In-Banner Video (IBV) ad – Serving Video ads with banner placements.
Low-Quality ad – Noisy ads based on user location
Researchers believe that “nearly 1 in every 250 impressions is dangerous or disruptive to the end-user, which equates to 4 billion malicious or disruptive impressions a month across the entire industry.”
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
