Maze ransomware, one of the most dangerous and potent strains of Windows ransomware that have hit companies and organizations around the world and demanded a payment in cryptocurrency in exchange for a safe recovery of encrypted data, has now officially announced the shutting down of its operations on its website on the dark web.
Though many ransomwares exist, Maze had differentiated itself from the others by not just stealing the data it finds but by also passing it on to servers controlled by hackers who then threaten to release it on public websites if they demanded ransom is not paid.
Major Maze Attacks
Earlier in April 2020, the Cybersecurity & Infrastructure Security Agency (CISA) had issued an alert stating that the Maze ransomware has hit US Healthcare centers releasing samples of data stolen, such as patient name, Social Security number, DoB, and other such information.
There are reports stating that Maze has also targeted companies such as Canon, Xerox, Visser, LG Electronics and many more.
The most prolific hit by Maze ransomware appears to be the IT giant, Cognizant. Earlier this year, Cognizant confirmed the attack, stating that several employees’ data appeared to be stolen.
However, not all companies choose to pay the ransom, as seen in the case of Allied Universal, a company providing security systems, janitorial services, and staffing.
The ransom demanded was 300 Bitcoins, which works out to approximately USD 4.15 million as per today’s conversion. Due to the lack of cooperation, 700MB worth of confidential Allied Universal data was published on public forums. Post this, the ransom ask was raised to 450 Bitcoins, approximately USD 6.2 million. However, there is no further clarity on whether the ransom was paid or the moral high road taken.
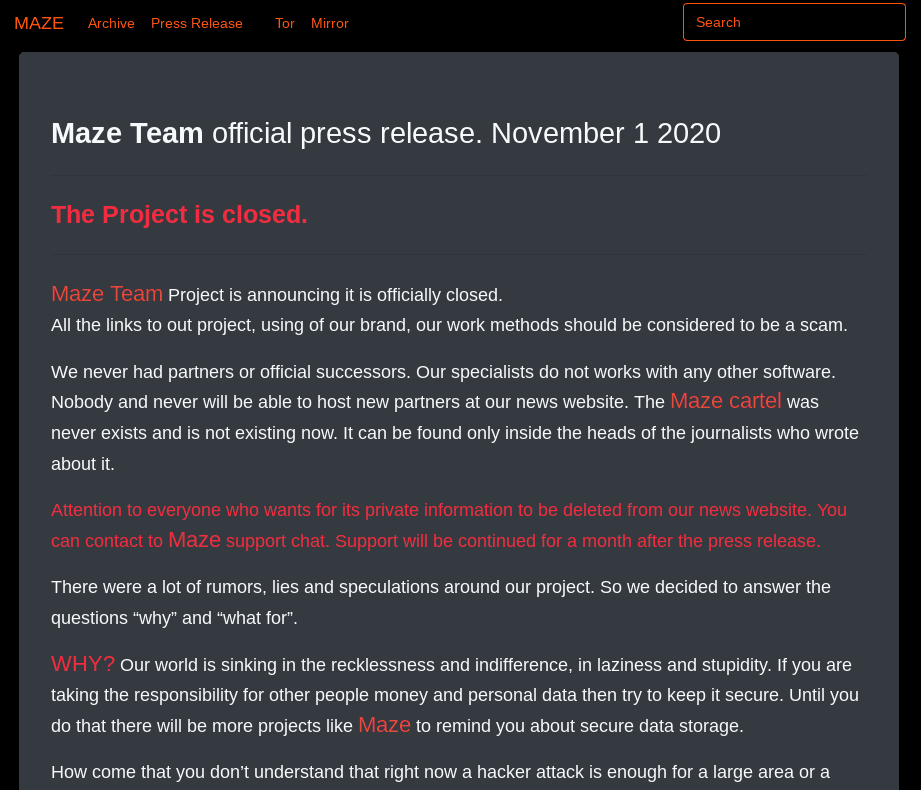
Announcement on closure
The group operating Maze ransomware officially announced their retirement on its website on the dark web.
Is this really the end or just a break to regroup and attack in a new avatar with renewed vigor? Only time will tell.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.



.png
)
