CYFIRMA’s Research and Advisory team has identified a new strain of ransomware labeled “Nnice,” following the continuous monitoring of underground forums as part of its Threat Discovery Process.
This ransomware specifically targets Windows systems, utilizing advanced encryption methods and employing multiple sophisticated evasion and persistence techniques.
It poses significant risks to enterprise security, emphasizing the need for robust defenses and comprehensive incident response strategies.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
Encryption and Target Behavior
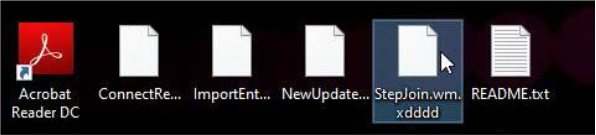
The Nnice ransomware encrypts files on the infected system and appends the distinctive extension “.xdddd” to the original file names.
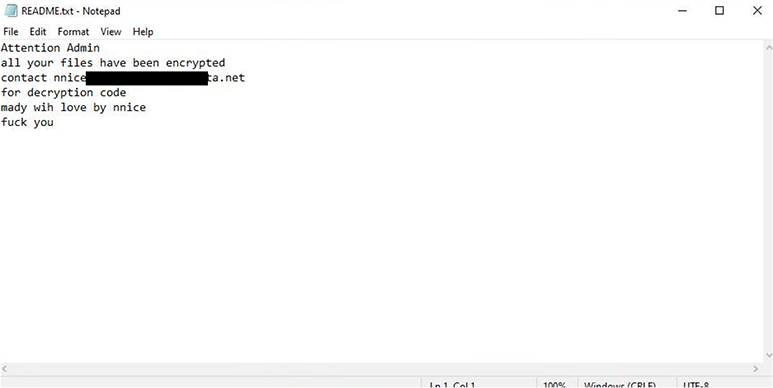
After encryption, victims encounter a ransom note titled “Readme.txt,” which provides detailed instructions for restoring their data.
Additionally, the ransomware modifies the system wallpaper to further alert the victim of the attack.
Persistence and Evasion Mechanisms
Nnice ransomware demonstrates advanced persistence techniques, including bootkit deployment, DLL side-loading, and registry key manipulations, designed to ensure continued presence on the impacted systems.
It also employs obfuscation, rootkits, and sandbox detection to evade detection by conventional security mechanisms.
Beyond encryption, the ransomware incorporates methods to hinder system recovery, such as deleting forensic artifacts and modifying security tools.
To mitigate risks, organizations are advised to monitor and block the identified SHA-256 hash associated with the ransomware:
4dd08b0bab6f19d143cca6f96c8b780da7f60dbf74f1c16c3442bc9f07d38030.
Implement strong authentication mechanisms, such as multifactor authentication (MFA), and adopt zero-trust architecture across all critical systems.
Ensure regular backups of all essential data, stored offline and tested periodically for integrity and restorability.
Design and implement a comprehensive data breach response plan that assesses data types, storage locations, remediation processes, and regulatory notification requirements.
According to the Cyfirma, Regularly apply the latest updates and security patches across all devices, operating systems, and software applications.
Actively monitor for IOCs and enhance defensive measures based on the intelligence provided, such as blocking the hash values linked to Nnice ransomware.
The emergence of Nnice ransomware highlights the growing sophistication of cyber threats targeting Windows platforms.
Organizations must remain vigilant by strengthening their defenses and proactively monitoring for threat indicators to mitigate potential data breaches and operational disruptions.
Integrating Application Security into Your CI/CD Workflows Using Jenkins & Jira -> Free Webinar
.webp?w=696&resize=696,0&ssl=1)


.png
)
