Tens of Thousands of Printers Exposed Online opens the door for hackers to steal sensitive information, service disruption, and in some cases remote command execution.
Shadowserver Foundation is a nonprofit security organization aiming that analyzes malicious Internet activity, particularly in IoT.
They are part of a project called VARIoT(Vulnerability and Attack Repository for IoT), it’s the ultimate goal is to “provide actionable security-related information about the Internet of Things (IoT).”
Printers Exposed Online
The company used to scan for online printers over TCP port 631, and they start regular scanning “of all 4 billion routable IPv4 addresses on the 5th of June 2020 and added Open IPP reporting as part of our daily public benefit remediation network reports on the 8th of June 2020.”
The scan indicates that an average of 80,000 printers exposed online via IPP(Internet Printing Protocol) on a daily bases, they were able to query those printers using parameter IPP Get-Printer-Attributes.
The IPP is an Internet Printing Protocol service that enabled on port 631/TCP. If an attacker connects the device, then it may results in information disclosure, also manipulation of printing jobs, in some cases remote code execution.
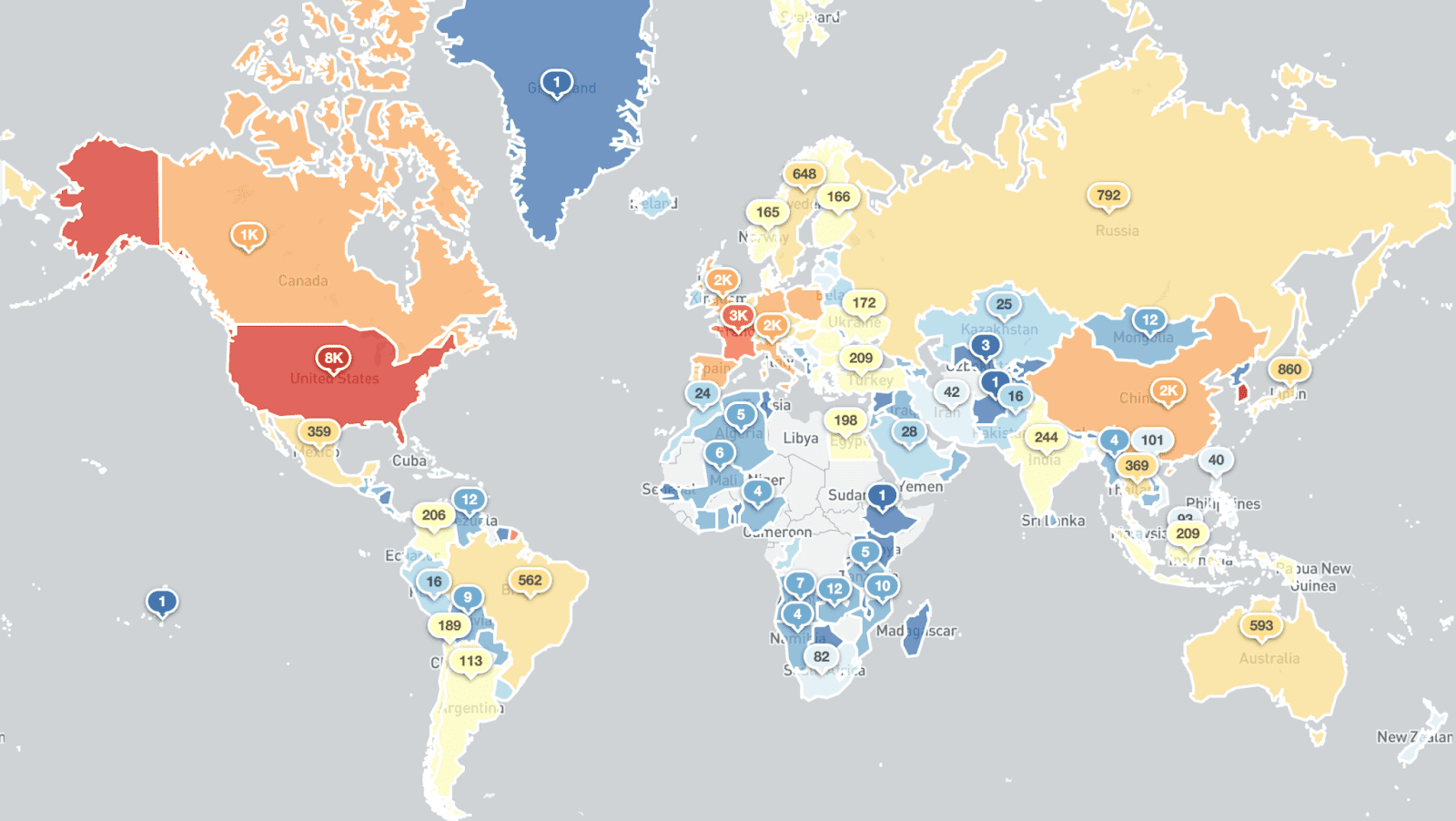
These printers are not behind the firewall and they are directly exposed over the Internet. Shadowserver Foundation provides a country-wise breakdown.
The top countries affected are South Korea(36.3k), United States(7.9k), Taiwan(6.7k), France (2.8k), and others.

Among the exposed 79,174 devices on that day (7th of June 2020), 58,091 devices using open source printing system CUPS developed by Apple Inc. It supports for macOS and other UNIX-like operating systems.
“Out of the roughly 80,000 exposed services, a large percentage returned additional printer information attributes, such as printer names, locations, models, firmware versions, organizational units, and even printer wifi ssids.”
Exposing the printers to online without nay firewalls may pose serious attacks can use it as a gateway to propagate further in the network.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity and hacking news updates.
Also Read:
100,000 Printers Hacked Worldwide Again by Hackers to Promote PewDiePie YouTube Channel
Thousands of Printers Hacked Worldwide & Hackers Promote PewDiePie YouTube Channel To Subscribe



.png
)
